One IP. One domain. One hash. In the hands of a good hunter, that's enough to unravel an entire campaign. But most tools stop at the lookup. Hunt 3.0 doesn't.
This release is built around the idea that every indicator is a doorway, and your job is to walk through it without hitting a dead end. We rebuilt the whole platform to make that possible, giving investigators full infrastructure context from a single indicator, inside one platform. We're also launching a free API, no credit card required, so you can stop copying and pasting and start automating.
Here's a quick look at what's new:
| Highlights | What's New? |
|---|---|
| Data Improvements | Flattened Data Architecture, Cloudflare Buster, Passive DNS History, Threat Actor Enablers, Provider Radar with Registrar intelligence |
| Usability Improvements | Visual Netblock Browsing, Vulnerability Intelligence workflow (CVE drilldowns, cross-CVE navigation, enriched daily digest), AttackCapture Code Search (AI categorization, negative facets, keyword highlighting), Flagged Attacks, Exploit Capture |
| General Improvements | Full platform rebuild, Free API (no credit card required), Provider Radar renamed from Host Radar, AttackCapture search filter dimensions (Intent, Package type, Function, Locale), Exploit Capture Similarity tab |
Let's now take a look at some of the most important improvements in Hunt 3.0
General Updates
Flattened Data Architecture
Legacy SQL previously couldn't perform joins across tables, which meant certain queries were simply off the table. In Hunt 3.0 we rearchitected the underlying data model to a single flattened structure, so hunters can now query across data that was previously out of reach, no workarounds needed.
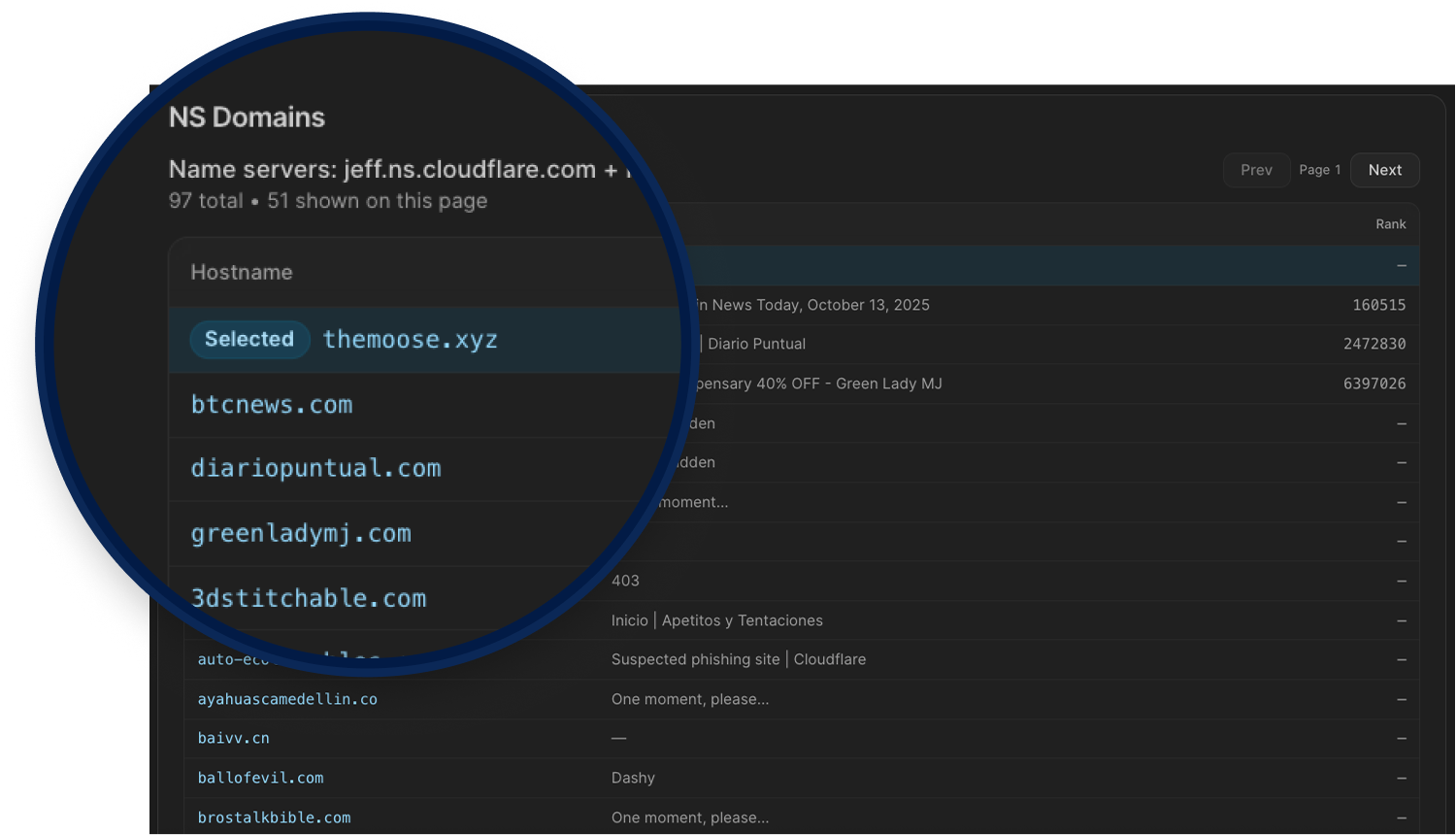
Cloudflare Buster
Amplifies one bad domain into a broader infrastructure view. Pivoting on Cloudflare nameserver pairs helps investigators avoid dead ends, uncover adjacent hosts, and quickly expand threat actor infrastructure clusters.
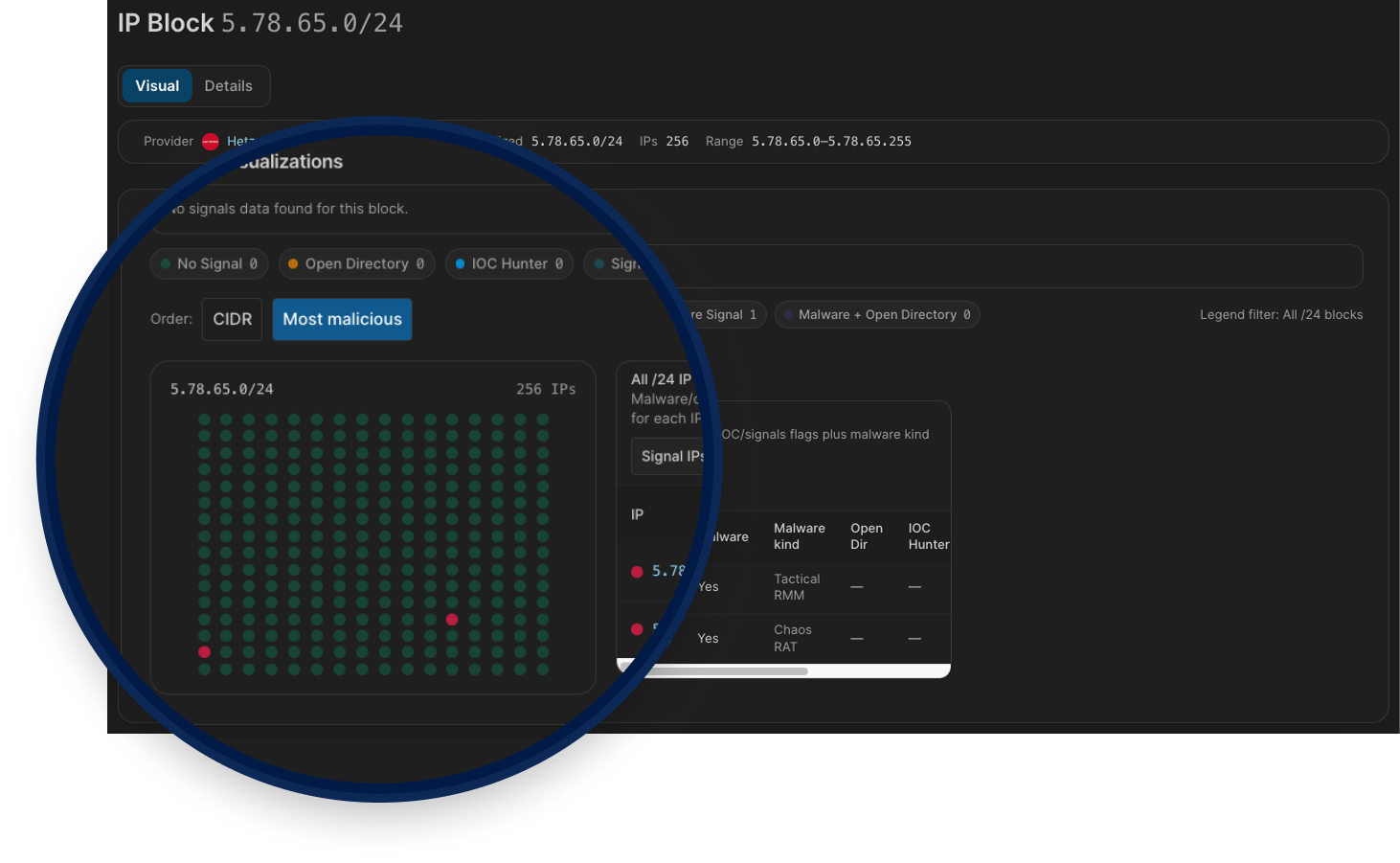
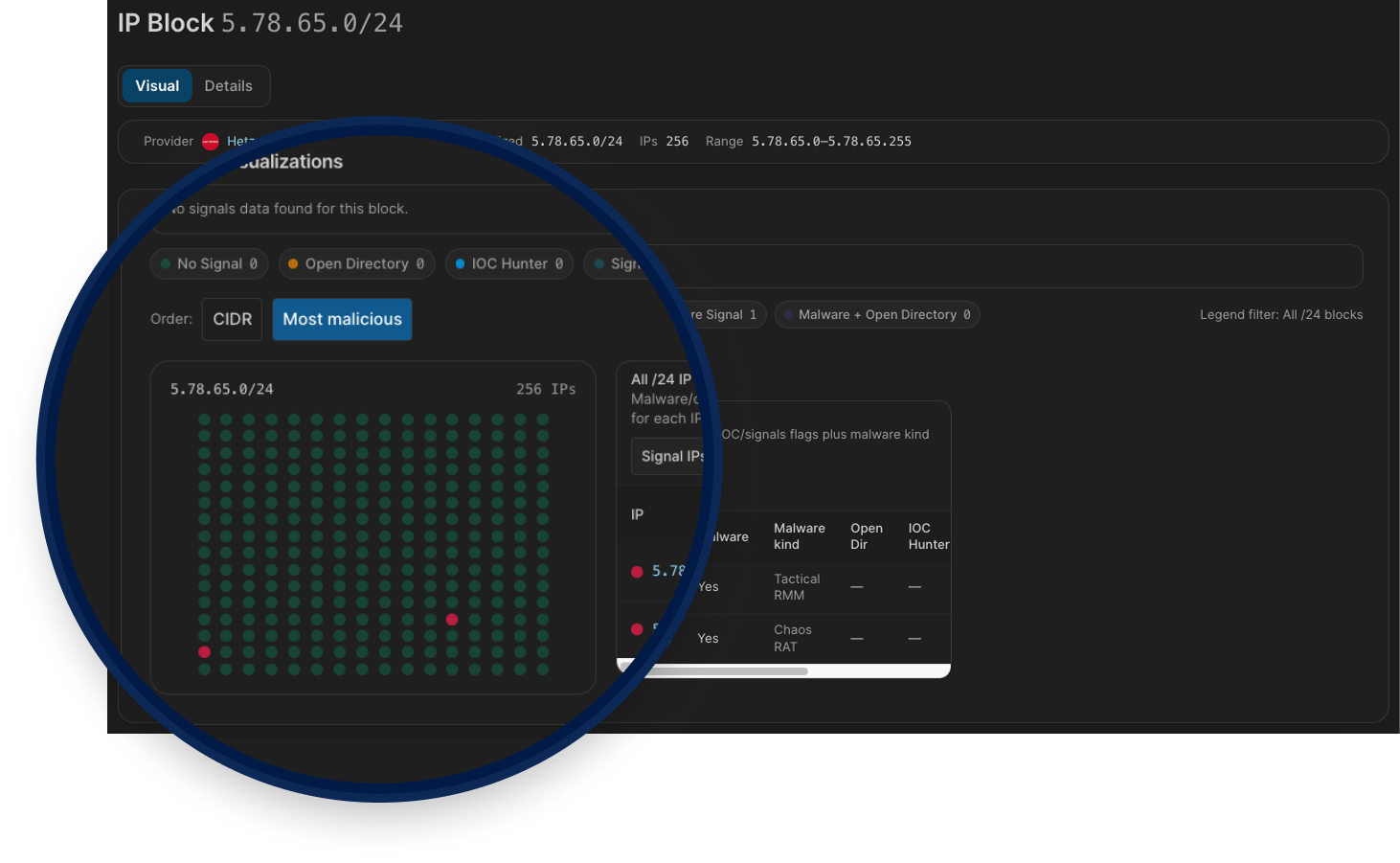
Browsing Netblocks (Visual)
Browsing Netblocks turns a CIDR into an interactive /24 map so you can quickly expand from one indicator to surrounding infrastructure.
It helps you find:
Malicious neighbors in adjacent /24 blocks
Deduce unknown malicious activity across the same netblock
Overlapping risk signals (C2s, AttackCapture, IOC Hunter, Signals)
Blocks that stand out for bulletproof-like, dense, repeated malicious patterns
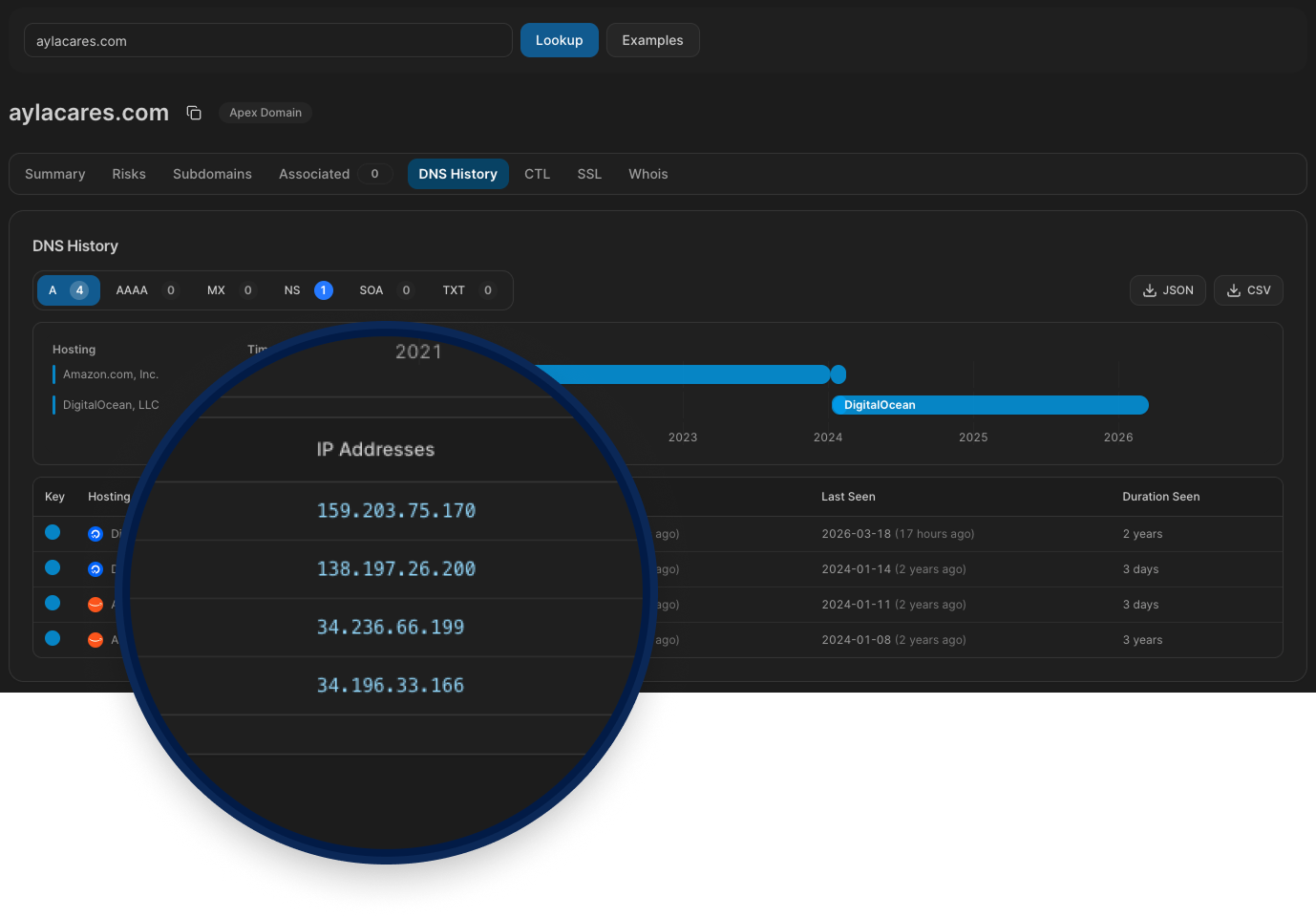
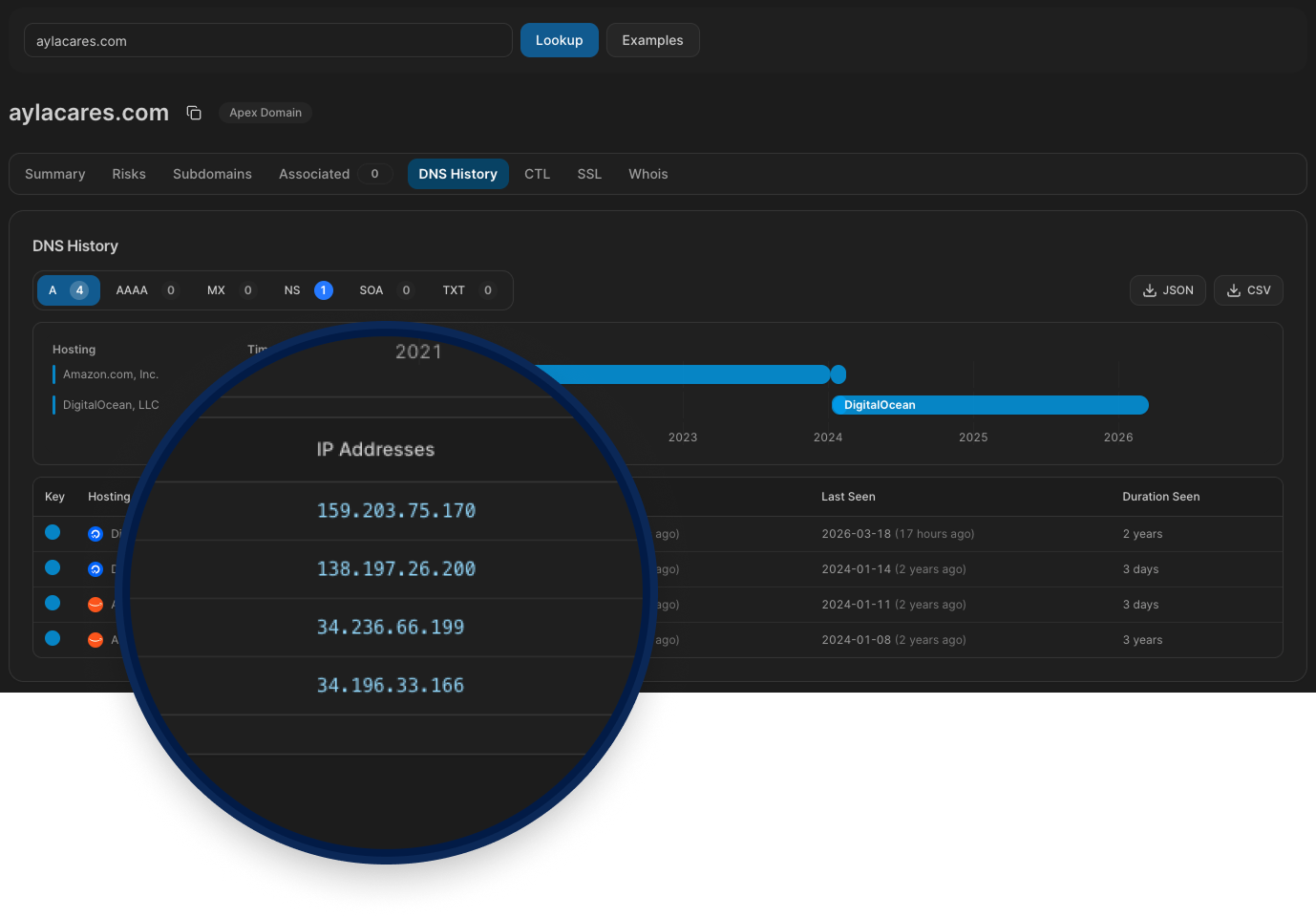
Passive DNS History
Turns passive DNS telemetry into a clear timeline of A, AAAA, MX, NS, SOA, and TXT changes, so you can see what changed, when it changed, and how long it stayed in place.
It helps you quickly spot:
Hosting/provider migrations over time
Malicious pivots between IPs, name servers, and mail routes
Short-lived or rotating records that point-in-time lookups miss
Related infrastructure you can pivot into from historical values
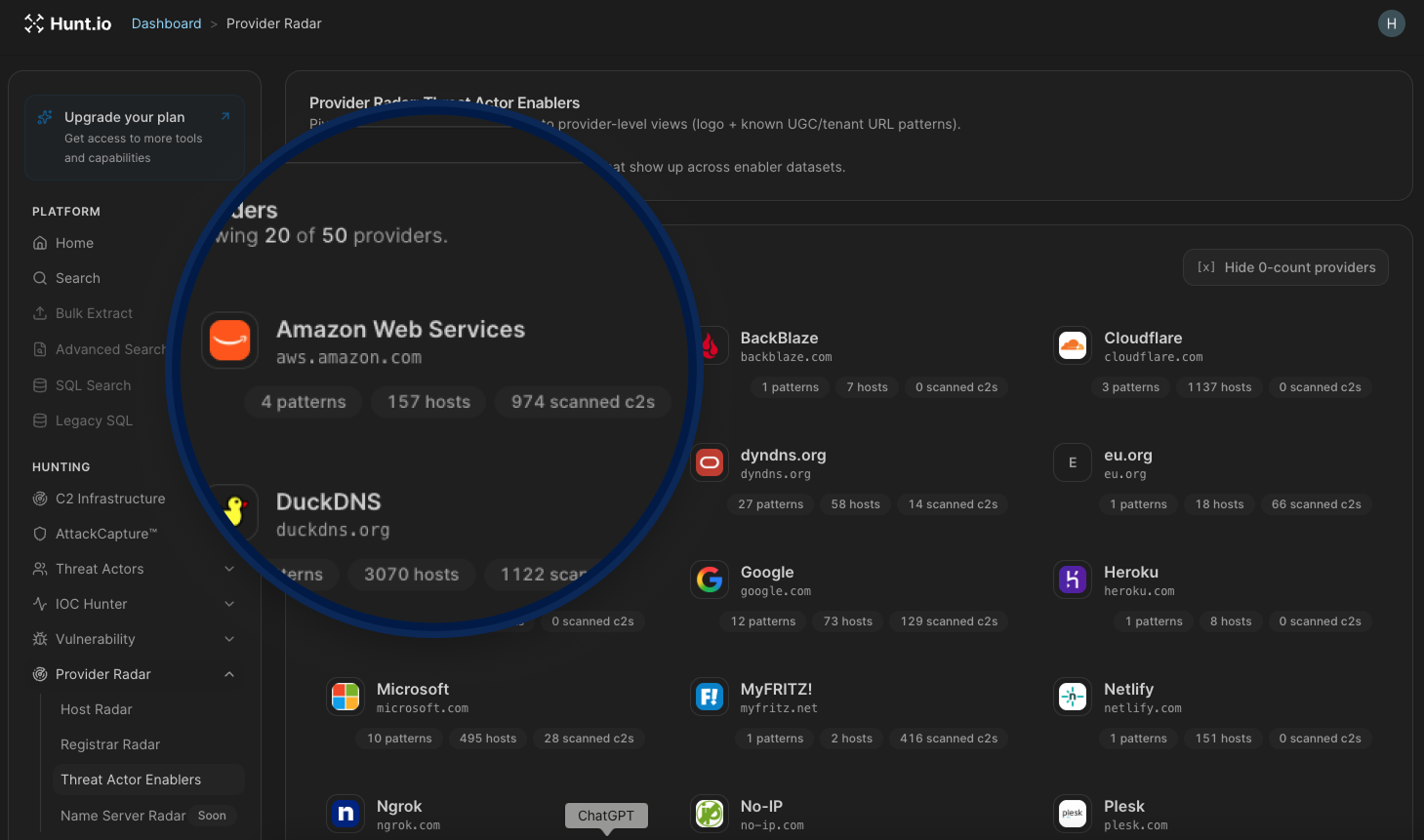
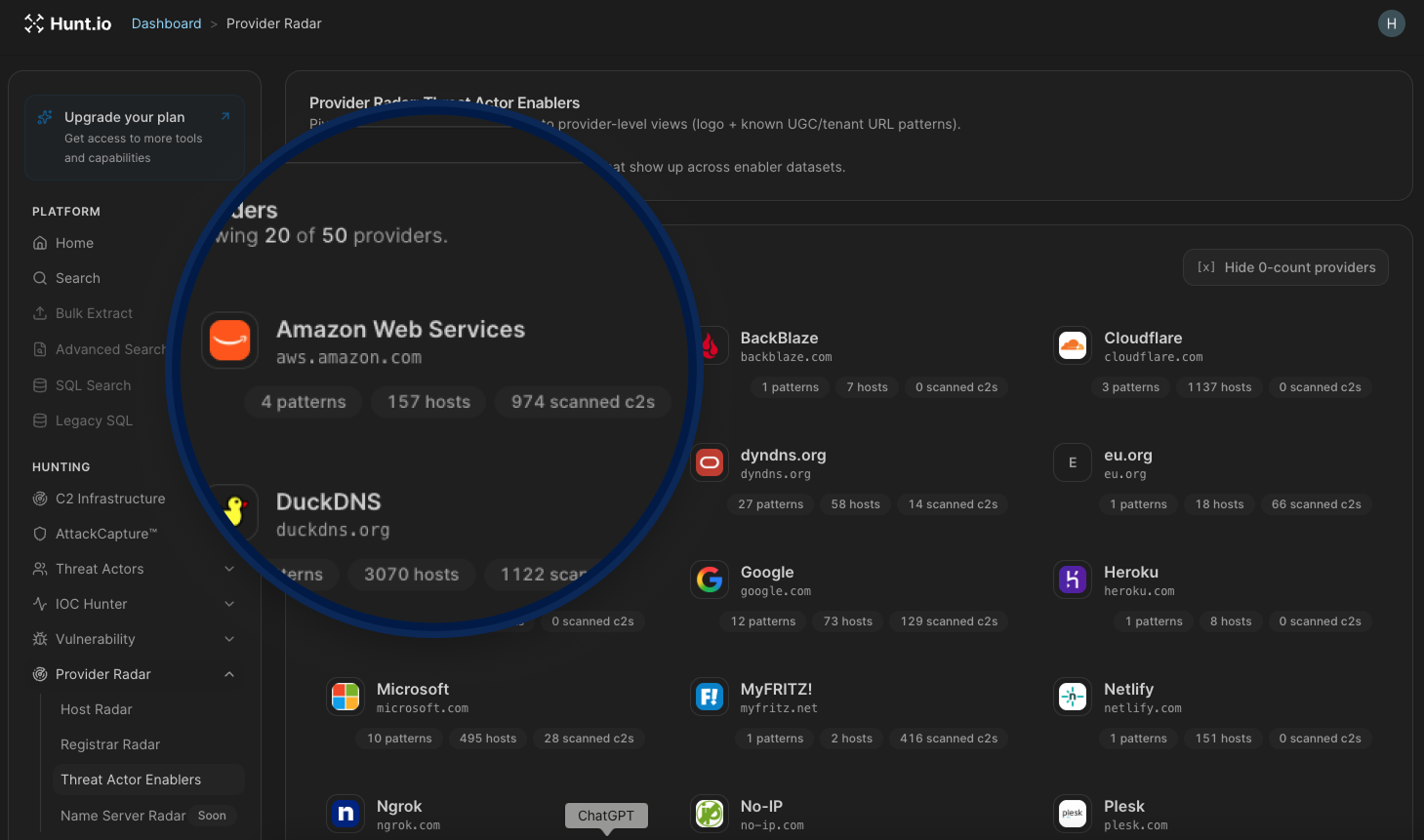
Threat Actor Enablers
Turns abused legitimate services into a structured map of attacker infrastructure so teams can investigate faster.
It helps you find:
Reused tenant domains and URL patterns across Dynamic DNS, PaaS, CDN/object storage, and other service categories
High-churn Dynamic DNS/tunneling infrastructure used for disposable phishing and C2 operations
Trusted cloud and PaaS surfaces where malicious activity blends into normal platform traffic
Provider-level enabler patterns that complement Hosting Radar by showing why a hosting company appears hot
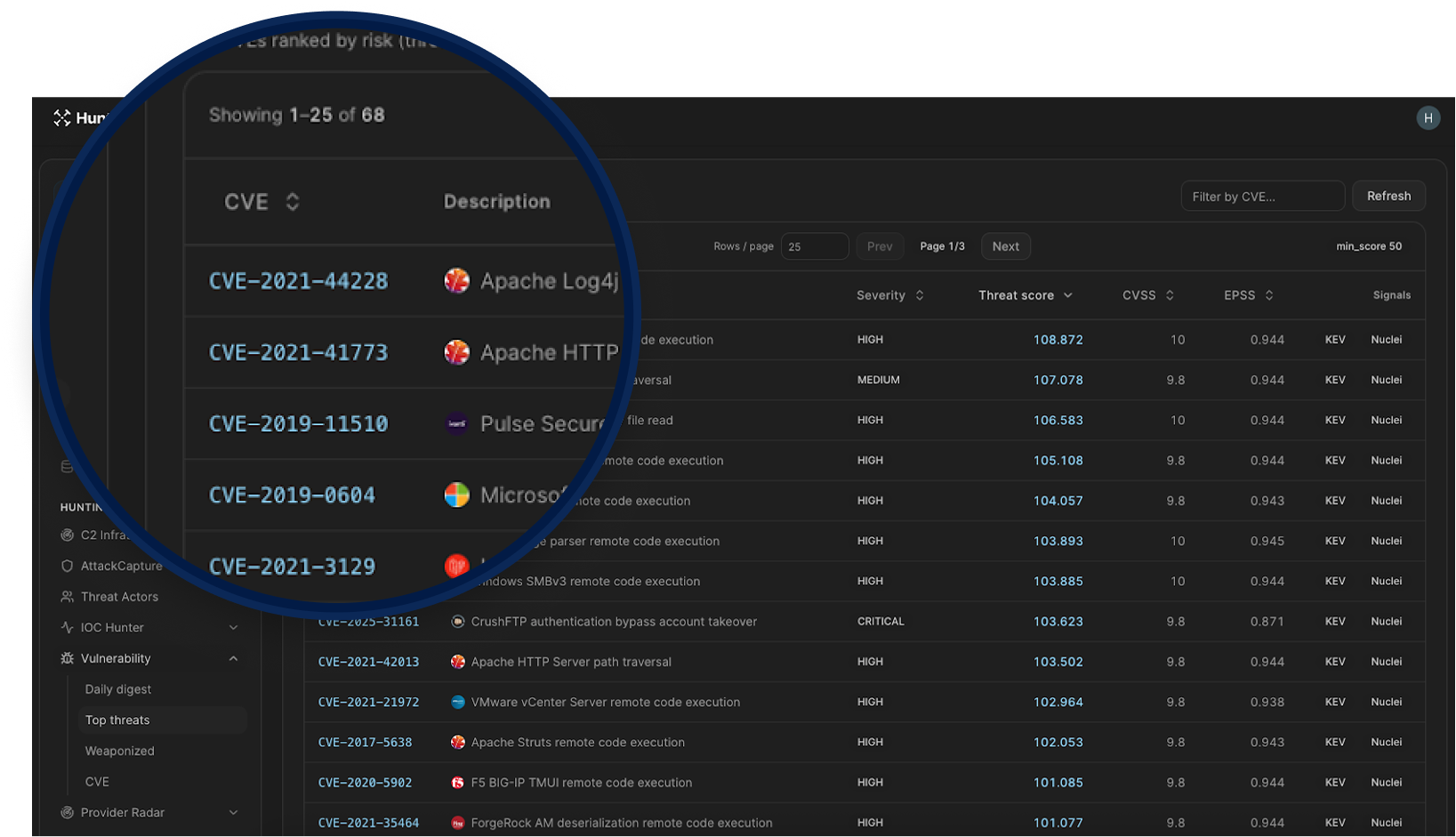
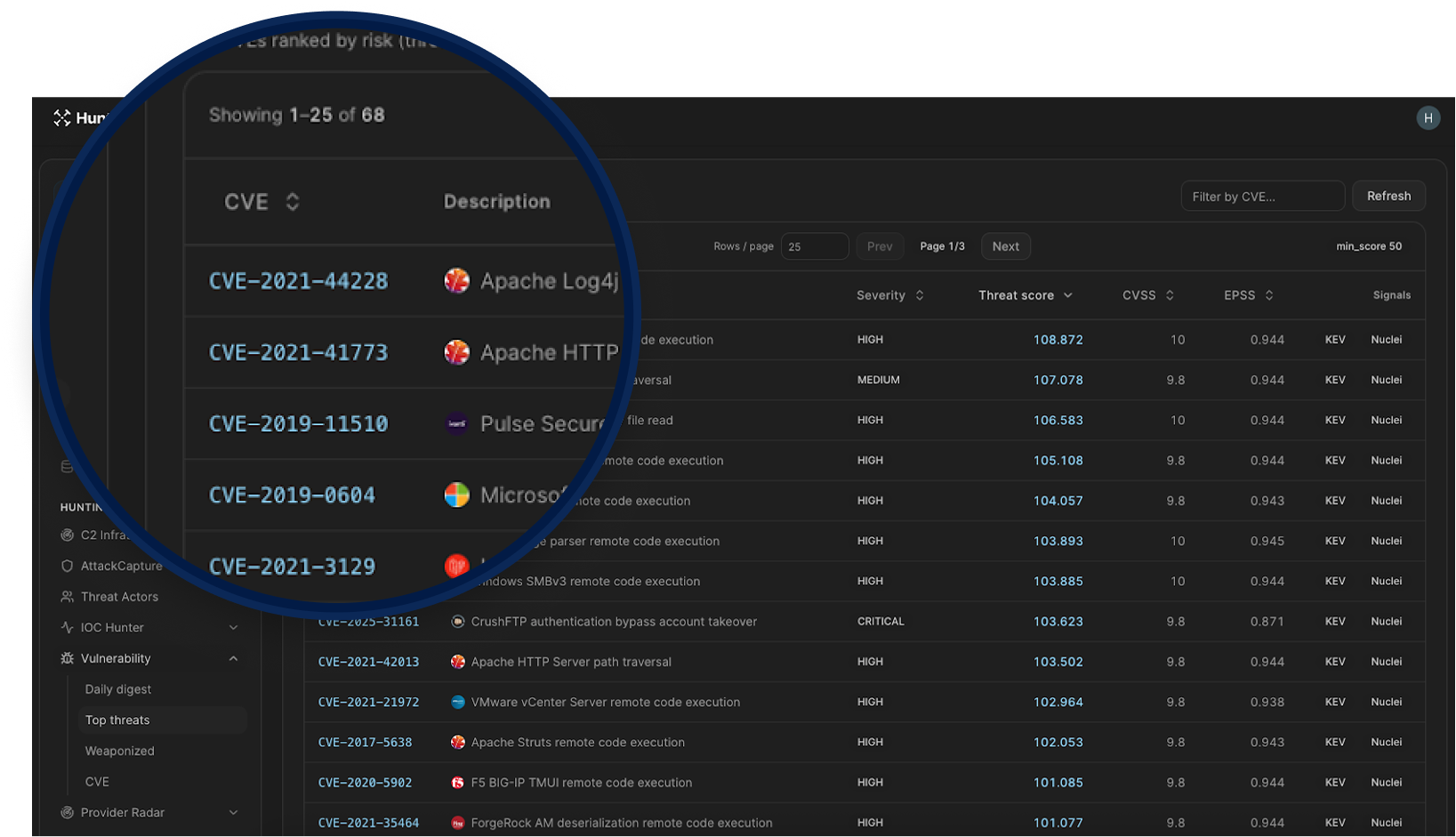
Vulnerability intelligence
Adds a connected workflow so you can move from trend detection to CVE-level investigation without context switching.
Linked views across the Vulnerability section: Daily digest, Top threats, and Weaponized now flow into the same CVE drilldown path.
Direct CVE drilldowns: CVE IDs open dedicated pages with tabs for Intel, Exploits, and Nuclei.
Cross-CVE navigation: CVE mentions inside vulnerability descriptions are linkified, so related CVEs are one click away.
Richer daily signal view: Daily digest now combines Hot in news, Reddit discussion, new KEV additions, and new exploits with rolling lookback windows.
Better prioritization signals: Top/Weaponized views surface threat score, CVSS, EPSS, KEV status, ransomware indicators, and exploit/detection evidence.
Integrated evidence links: CVE detail pages connect to IOC Hunter stories and primary sources like NVD, CISA KEV, EPSS, ExploitDB, GitHub, and ProjectDiscovery.
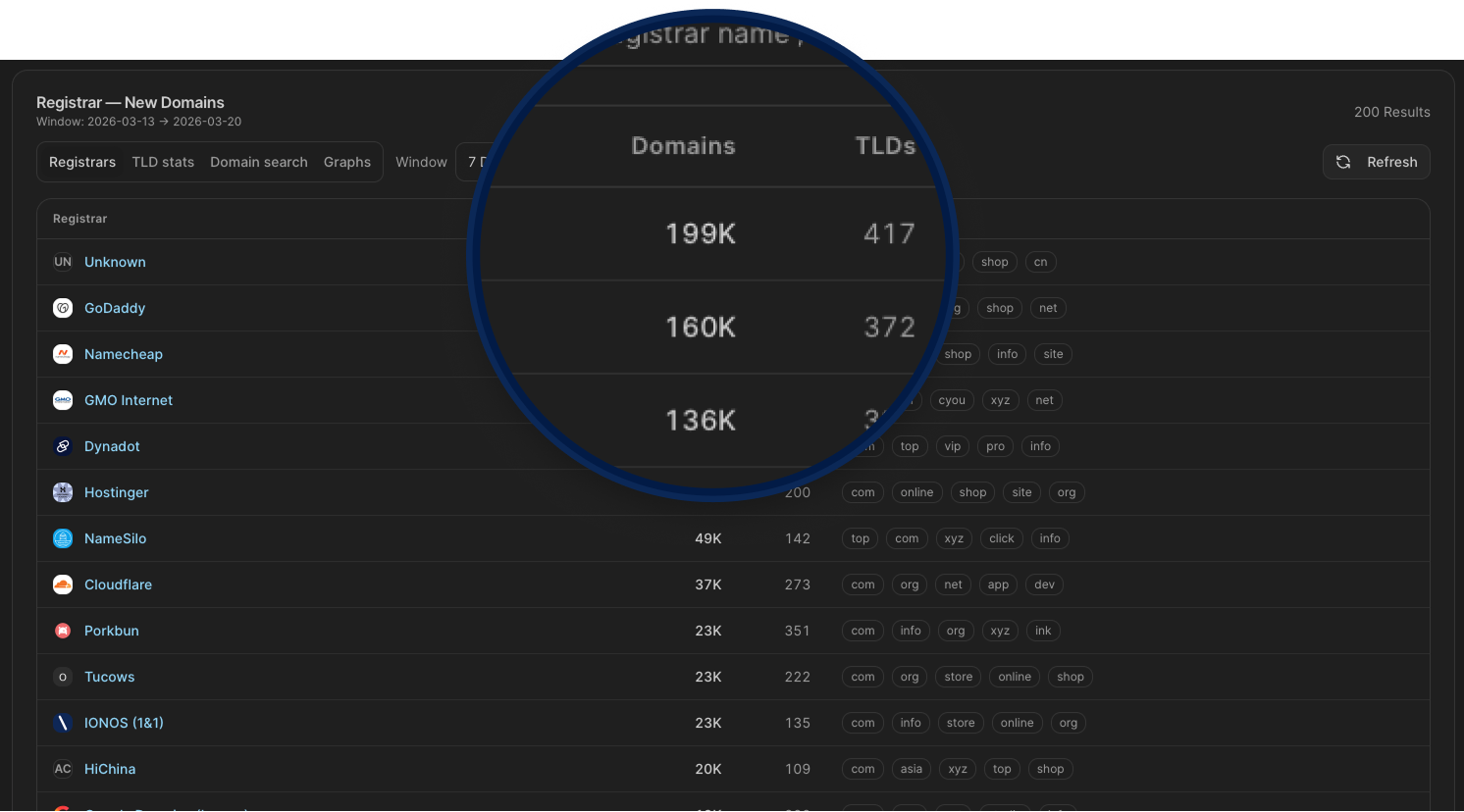
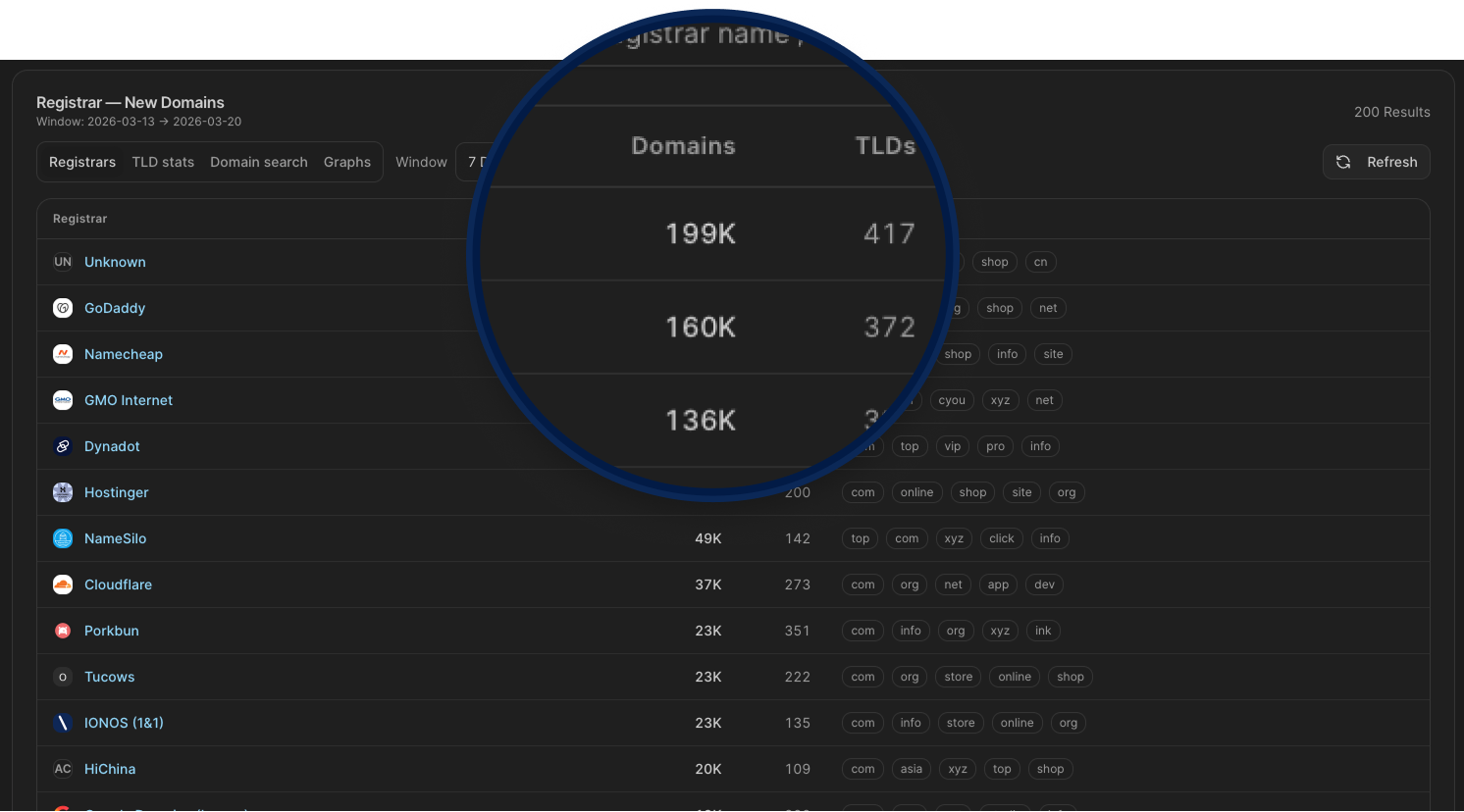
Registrar Radar
Host Radar is now Provider Radar, and includes Domain Registrar intelligence so you can track newly registered domains across 200+ registrars, monitor registration volume by TLD, spot unusual spikes in domain creation activity, and drill into specific registrars to see exactly what's being registered and when.
For hunters tracking threat actor infrastructure, this means catching domain provisioning patterns early, identifying registrars commonly abused for malicious campaigns, and correlating new domain activity with known attacker behavior before those domains go live in an attack.
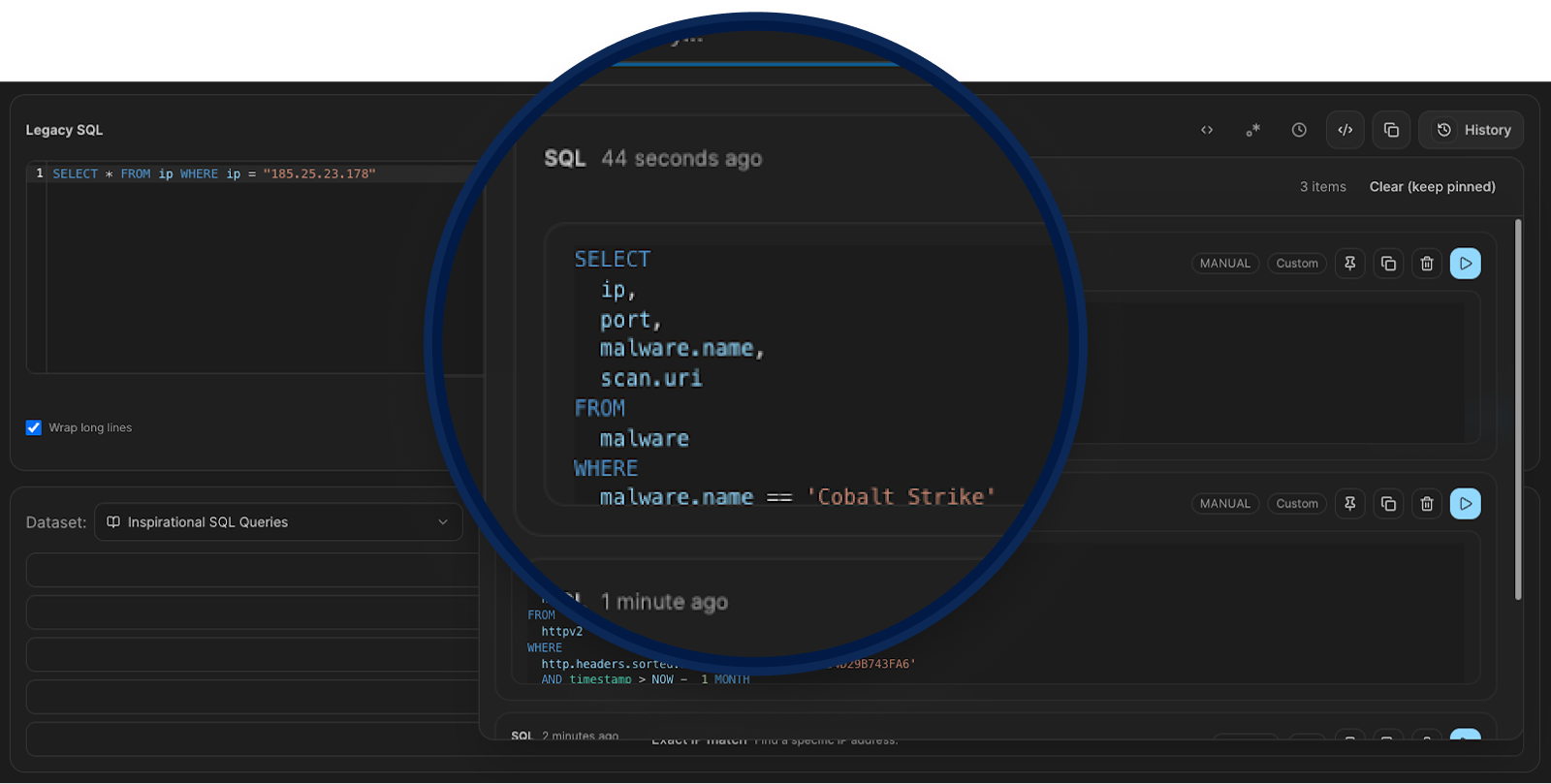
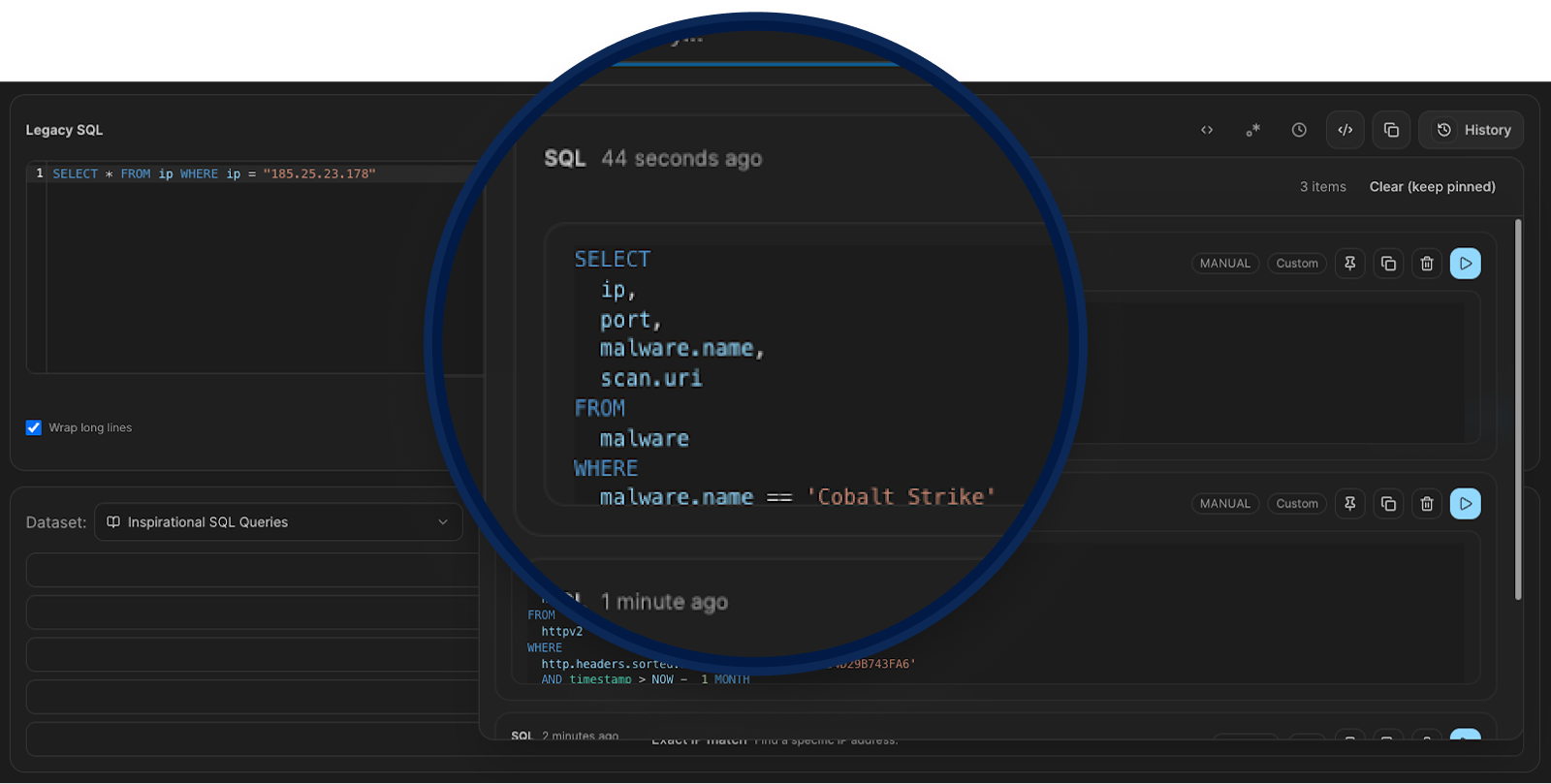
Legacy SQL History
Legacy SQL now saves your query history so you can backtrack without rewriting from scratch. Past queries are stored with timestamps, filterable, and can be pinned or re-run directly from the history panel. Useful when you're mid-investigation and need to revisit a query you ran ten minutes ago without losing your current work.
AttackCapture
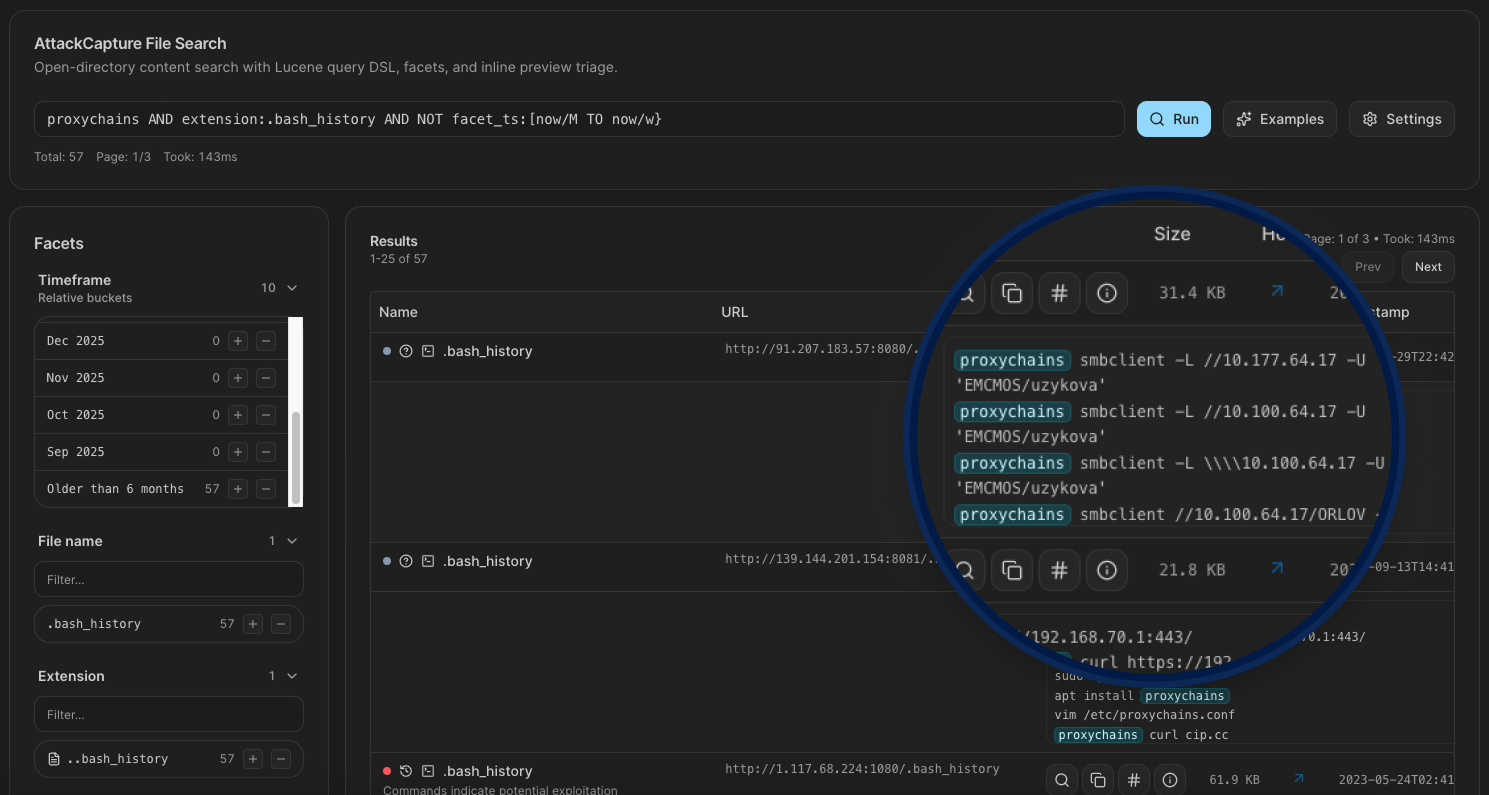
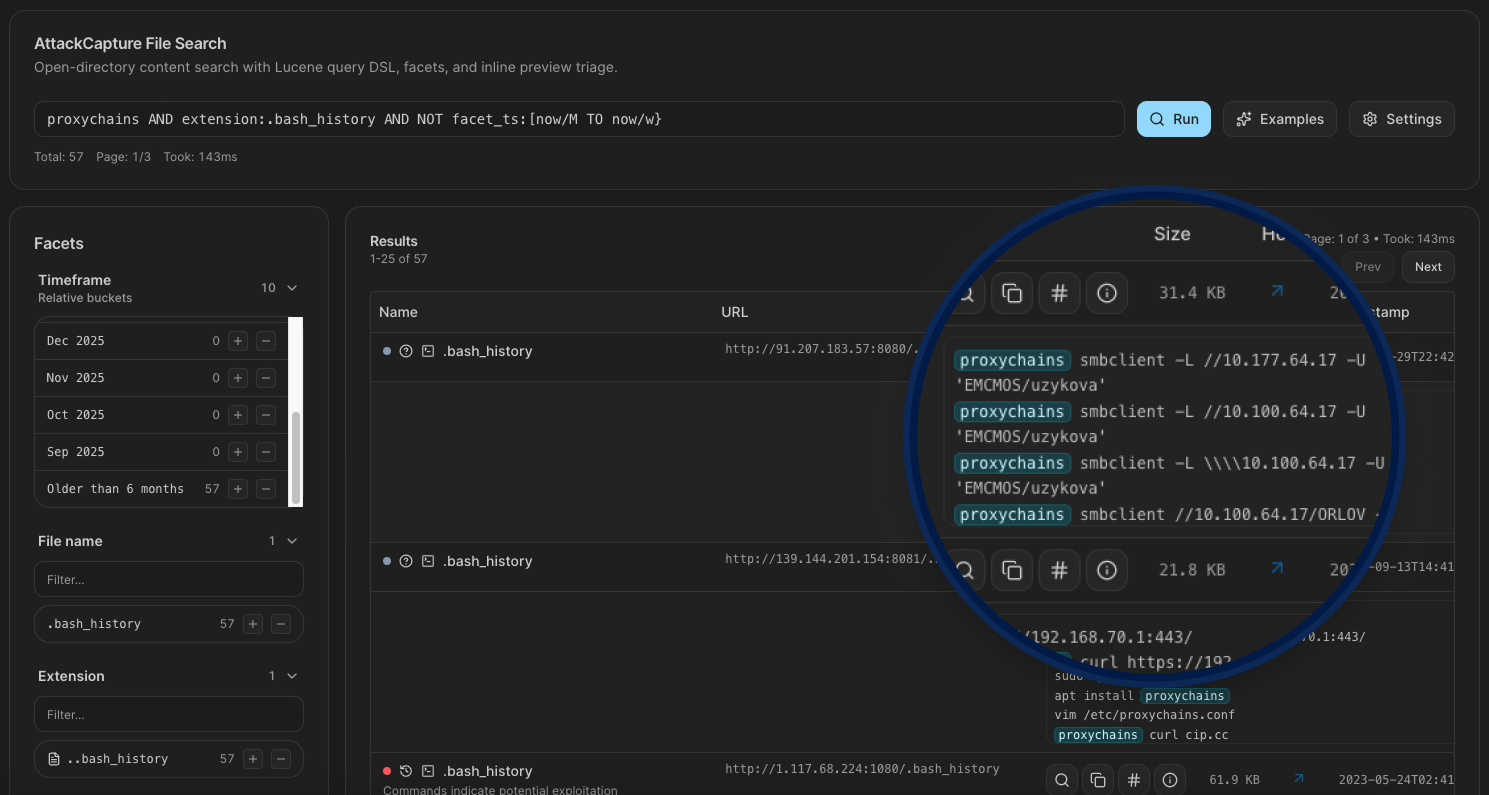
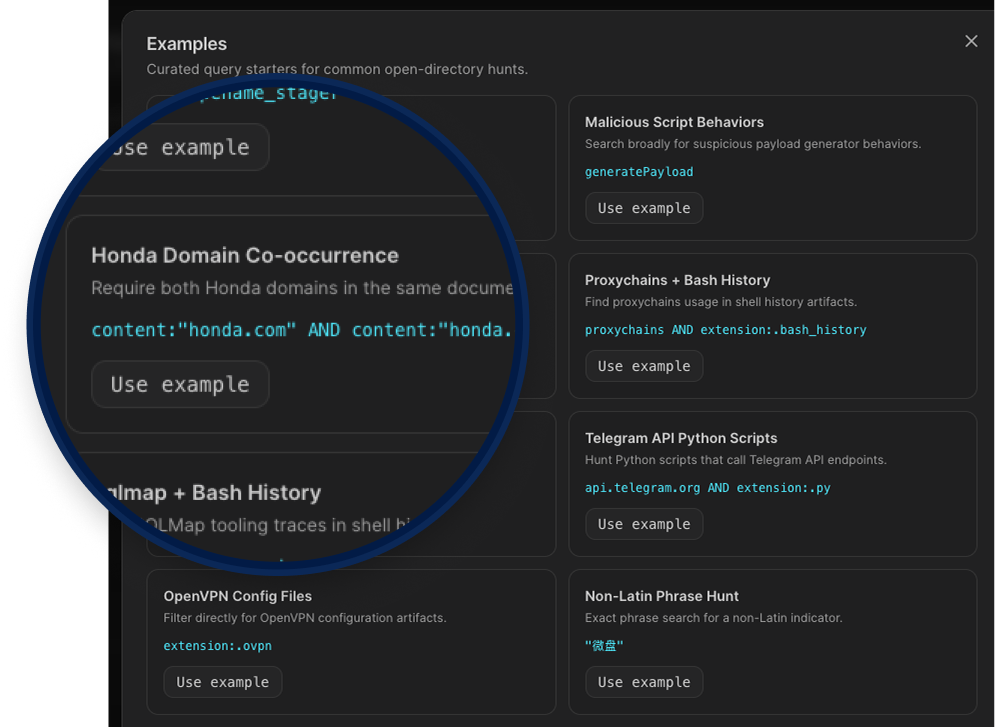
Improved Code Search
Files are now AI-categorized automatically, giving you intent and function classification without manual tagging. Facet filtering is broader with more dimensions to work with, and you can now exclude results using negative facets to cut out the noise fast. Keyword highlighting in file previews helps you spot what you're looking for without having to open and read through each file manually.
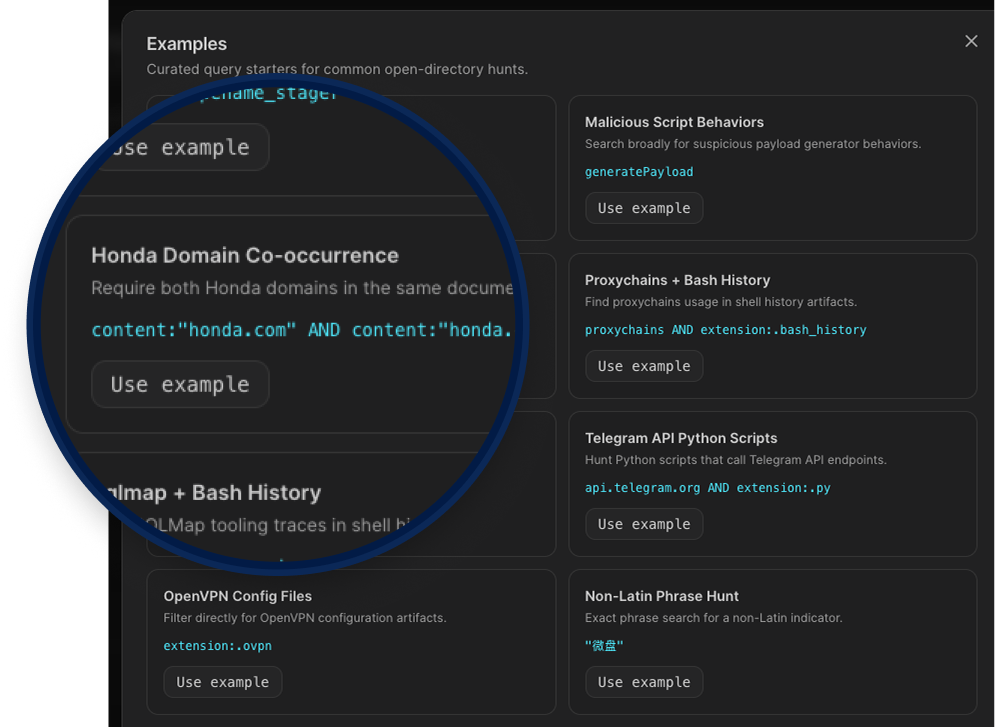
The search filters panel lets you narrow results across six dimensions: file name, extension, file type, hostname, file intent, and file function. Each filter supports free-text input and bucket selection, and you can combine multiple values using AND or OR logic, giving you the flexibility to cast a wider net or get very specific depending on what you're hunting for.
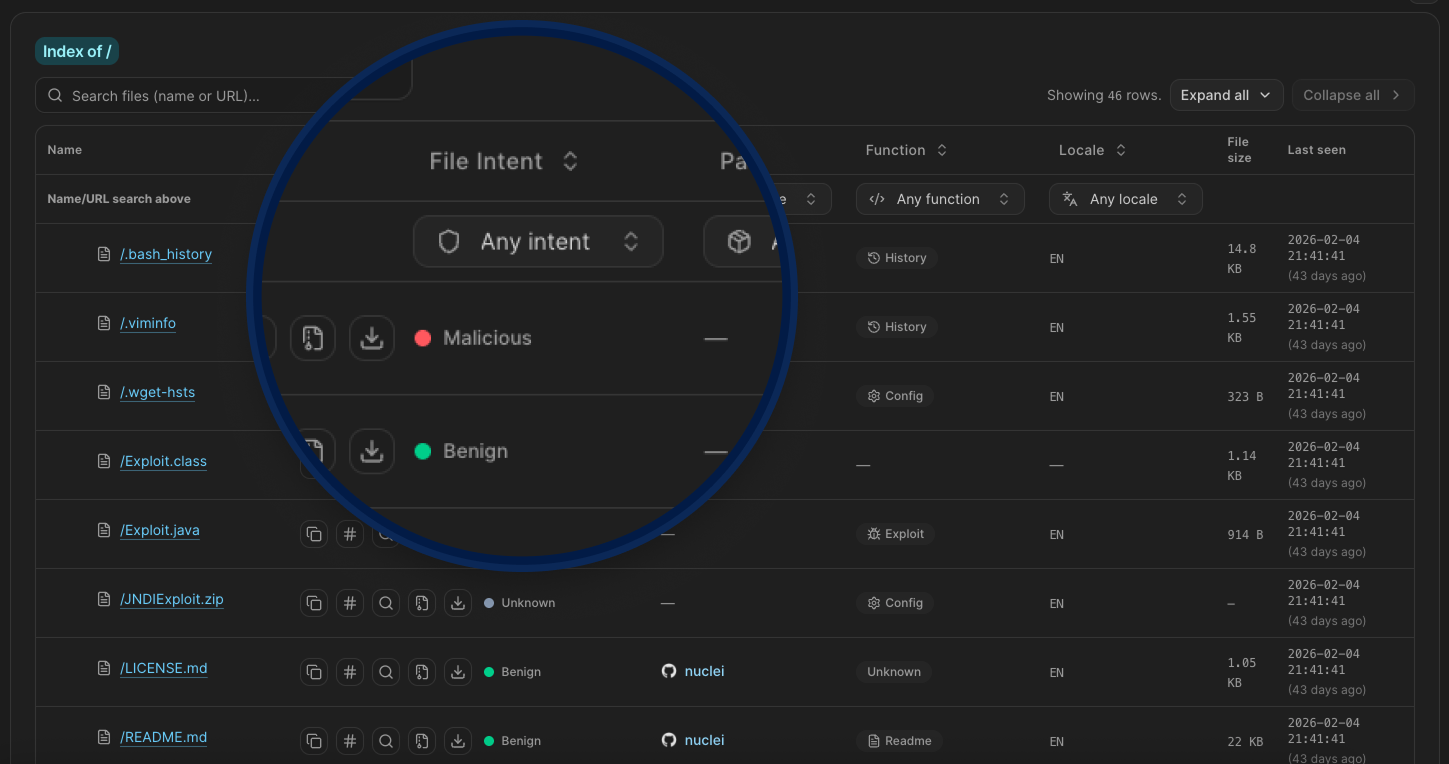
New Search Filters
Hunt 3.0 adds granular filtering to exposed open directory browsing inside AttackCapture. You can now filter files by:
Intent (Benign, Malicious, or Unknown),
Package type (currently nuclei),
Function (Config, Exploit, History, Readme, Target, or Unknown),
Locale, which gives you a direct signal on the operator's language and likely origin.
Instead of scrolling through hundreds of staged files trying to figure out what matters, you can cut straight to the exploits, configs, or target lists you actually care about.
Flagged Attacks
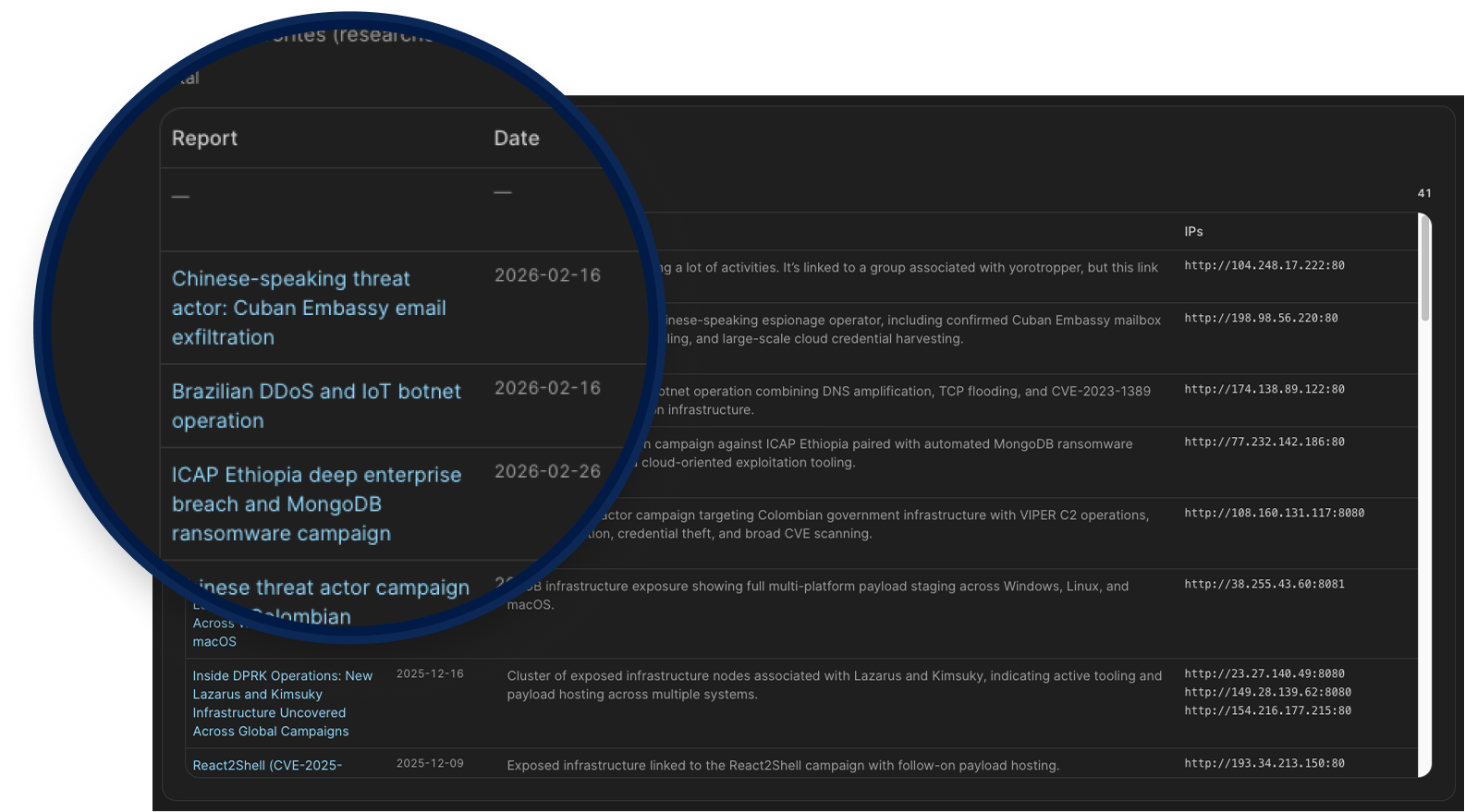
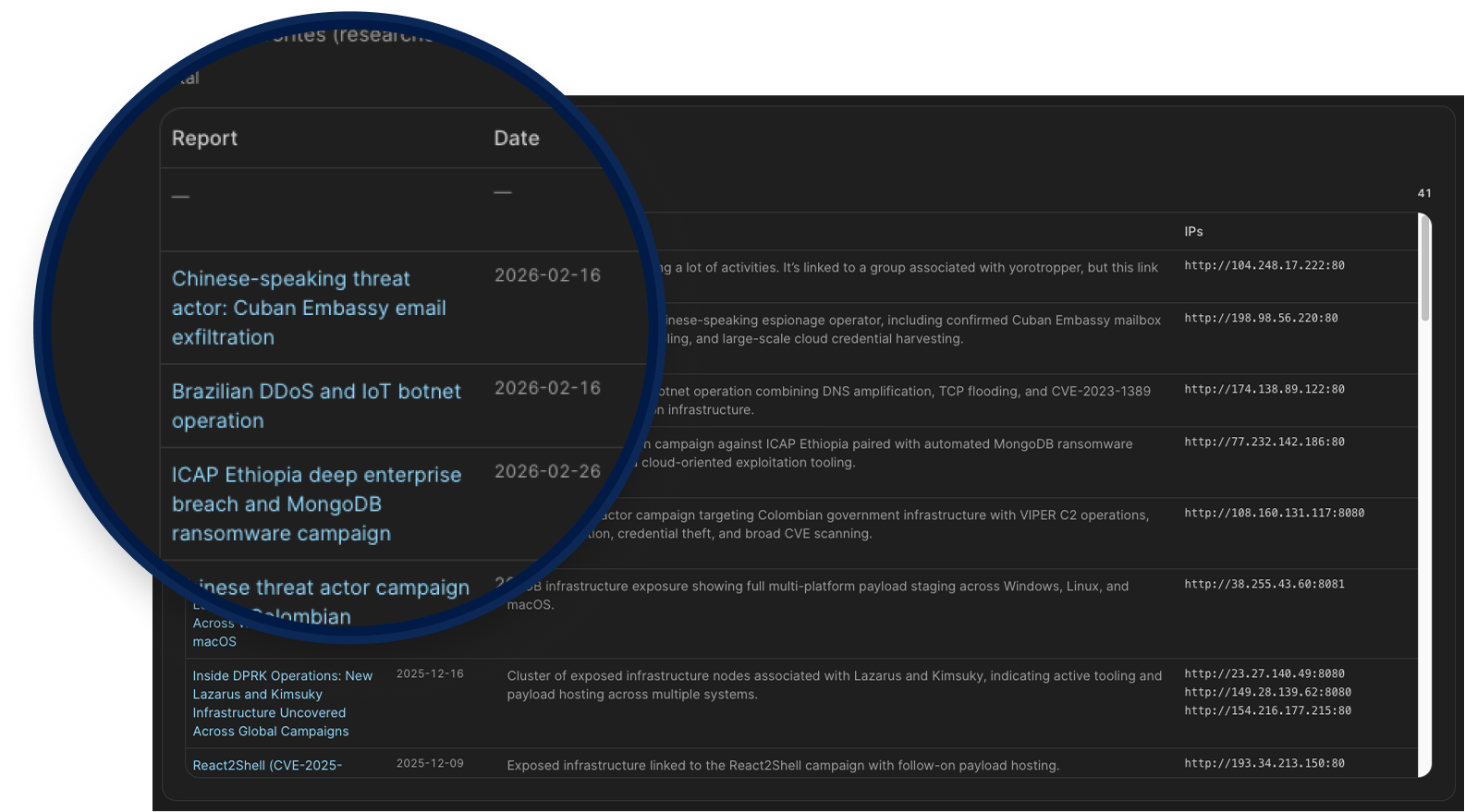
When threat actors leave operational directories exposed, Hunt.io captures what's inside before it disappears. Flagged Attacks turns that raw exposure data into structured campaign reports, each tied to specific IPs, IOCs, exploited CVEs, and attribution indicators. Not inferred, not modeled. Documented from direct observation of attacker infrastructure.
This gives hunters a fast way to check if an IP connects to a known operation, what tooling the actor is running, and what else belongs to the same infrastructure cluster. The kind of context that usually takes hours to piece together is already done.
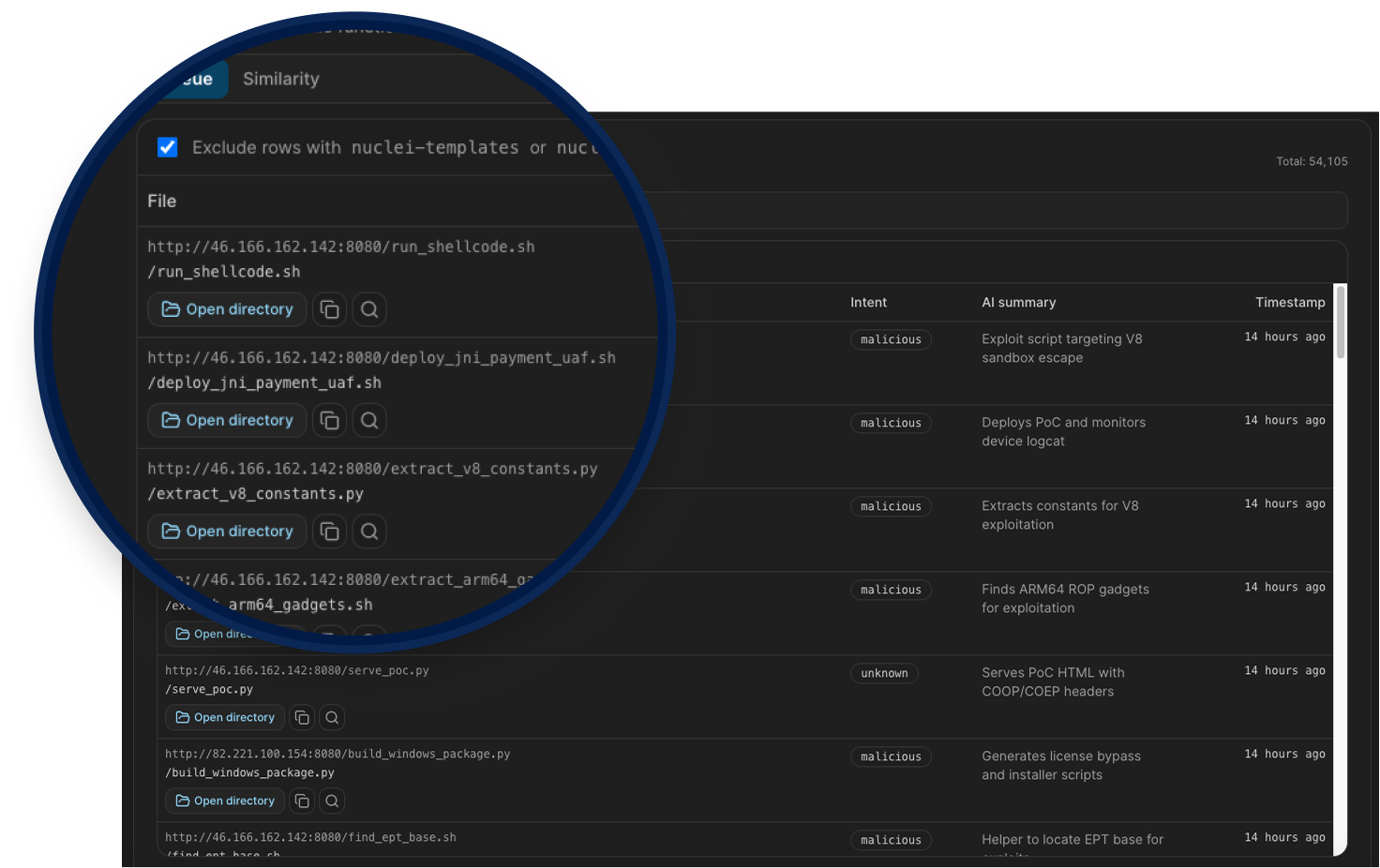
Exploit Capture
This is a dedicated queue inside AttackCapture that surfaces files AI-classified as exploits from exposed open directories, currently indexing over 54,000 files sorted newest first. From each entry, you can pivot directly into the parent open directory, preview file content, or copy the SHA256 hash for use in detections and YARA rules.
A toggle filters out nuclei template noise to keep the queue focused on what matters. The Similarity tab adds sidecar metadata for visible queue rows, helping you cluster related tooling across different attacker infrastructure.
For hunters and analysts, this is direct access to the actual tools attackers are staging and deploying in the wild.
Hunt v3 is a full rebuild, but the goal hasn't changed: give threat hunters better data, better context, and fewer dead ends. Every feature in this release was shaped by the investigations happening on the platform every day, and there's more coming. If something feels off or you have an idea for what we should tackle next, we'd love to hear it.
One IP. One domain. One hash. In the hands of a good hunter, that's enough to unravel an entire campaign. But most tools stop at the lookup. Hunt 3.0 doesn't.
This release is built around the idea that every indicator is a doorway, and your job is to walk through it without hitting a dead end. We rebuilt the whole platform to make that possible, giving investigators full infrastructure context from a single indicator, inside one platform. We're also launching a free API, no credit card required, so you can stop copying and pasting and start automating.
Here's a quick look at what's new:
| Highlights | What's New? |
|---|---|
| Data Improvements | Flattened Data Architecture, Cloudflare Buster, Passive DNS History, Threat Actor Enablers, Provider Radar with Registrar intelligence |
| Usability Improvements | Visual Netblock Browsing, Vulnerability Intelligence workflow (CVE drilldowns, cross-CVE navigation, enriched daily digest), AttackCapture Code Search (AI categorization, negative facets, keyword highlighting), Flagged Attacks, Exploit Capture |
| General Improvements | Full platform rebuild, Free API (no credit card required), Provider Radar renamed from Host Radar, AttackCapture search filter dimensions (Intent, Package type, Function, Locale), Exploit Capture Similarity tab |
Let's now take a look at some of the most important improvements in Hunt 3.0
General Updates
Flattened Data Architecture
Legacy SQL previously couldn't perform joins across tables, which meant certain queries were simply off the table. In Hunt 3.0 we rearchitected the underlying data model to a single flattened structure, so hunters can now query across data that was previously out of reach, no workarounds needed.
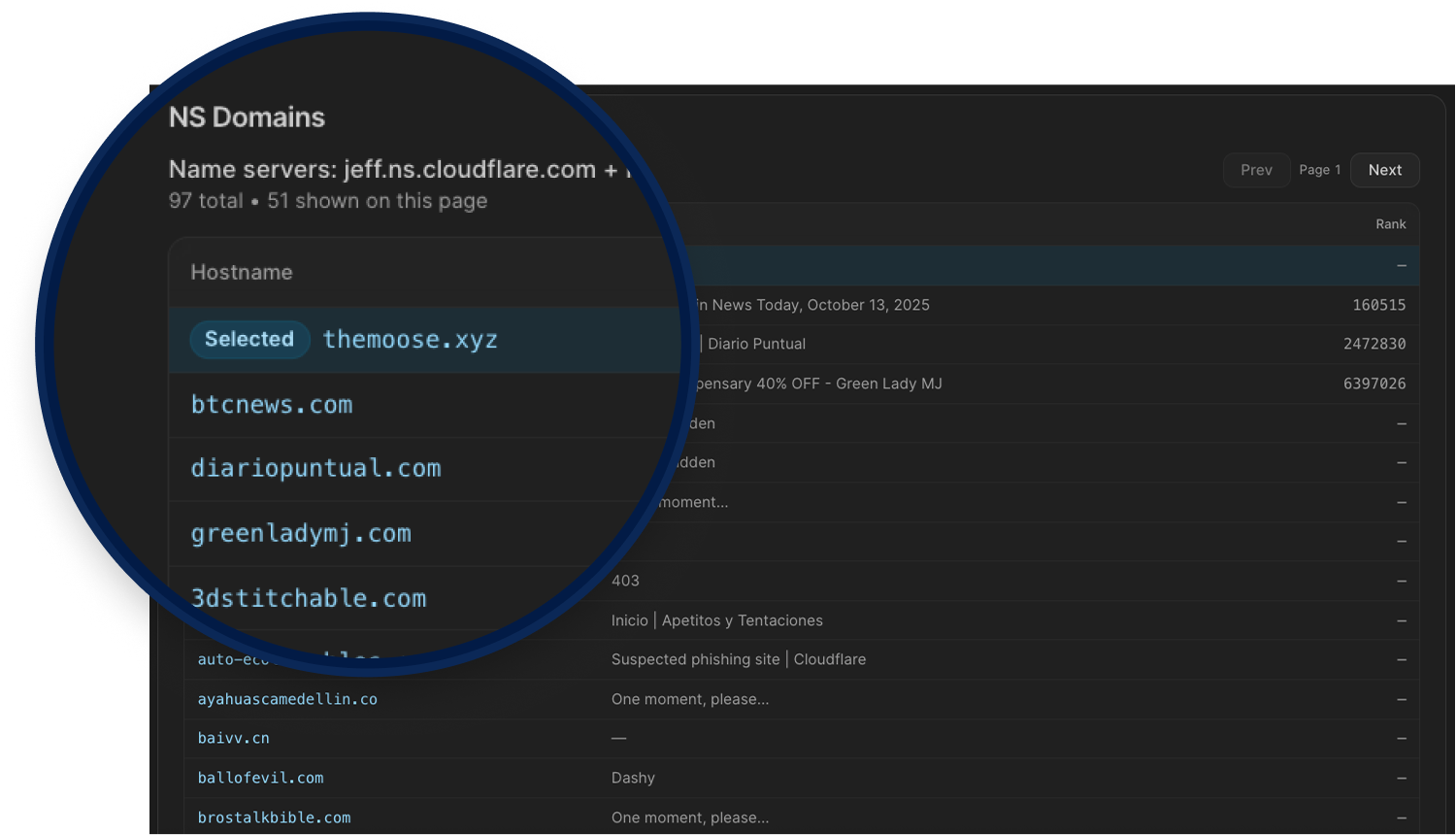
Cloudflare Buster
Amplifies one bad domain into a broader infrastructure view. Pivoting on Cloudflare nameserver pairs helps investigators avoid dead ends, uncover adjacent hosts, and quickly expand threat actor infrastructure clusters.
Browsing Netblocks (Visual)
Browsing Netblocks turns a CIDR into an interactive /24 map so you can quickly expand from one indicator to surrounding infrastructure.
It helps you find:
Malicious neighbors in adjacent /24 blocks
Deduce unknown malicious activity across the same netblock
Overlapping risk signals (C2s, AttackCapture, IOC Hunter, Signals)
Blocks that stand out for bulletproof-like, dense, repeated malicious patterns
Passive DNS History
Turns passive DNS telemetry into a clear timeline of A, AAAA, MX, NS, SOA, and TXT changes, so you can see what changed, when it changed, and how long it stayed in place.
It helps you quickly spot:
Hosting/provider migrations over time
Malicious pivots between IPs, name servers, and mail routes
Short-lived or rotating records that point-in-time lookups miss
Related infrastructure you can pivot into from historical values
Threat Actor Enablers
Turns abused legitimate services into a structured map of attacker infrastructure so teams can investigate faster.
It helps you find:
Reused tenant domains and URL patterns across Dynamic DNS, PaaS, CDN/object storage, and other service categories
High-churn Dynamic DNS/tunneling infrastructure used for disposable phishing and C2 operations
Trusted cloud and PaaS surfaces where malicious activity blends into normal platform traffic
Provider-level enabler patterns that complement Hosting Radar by showing why a hosting company appears hot
Vulnerability intelligence
Adds a connected workflow so you can move from trend detection to CVE-level investigation without context switching.
Linked views across the Vulnerability section: Daily digest, Top threats, and Weaponized now flow into the same CVE drilldown path.
Direct CVE drilldowns: CVE IDs open dedicated pages with tabs for Intel, Exploits, and Nuclei.
Cross-CVE navigation: CVE mentions inside vulnerability descriptions are linkified, so related CVEs are one click away.
Richer daily signal view: Daily digest now combines Hot in news, Reddit discussion, new KEV additions, and new exploits with rolling lookback windows.
Better prioritization signals: Top/Weaponized views surface threat score, CVSS, EPSS, KEV status, ransomware indicators, and exploit/detection evidence.
Integrated evidence links: CVE detail pages connect to IOC Hunter stories and primary sources like NVD, CISA KEV, EPSS, ExploitDB, GitHub, and ProjectDiscovery.
Registrar Radar
Host Radar is now Provider Radar, and includes Domain Registrar intelligence so you can track newly registered domains across 200+ registrars, monitor registration volume by TLD, spot unusual spikes in domain creation activity, and drill into specific registrars to see exactly what's being registered and when.
For hunters tracking threat actor infrastructure, this means catching domain provisioning patterns early, identifying registrars commonly abused for malicious campaigns, and correlating new domain activity with known attacker behavior before those domains go live in an attack.
Legacy SQL History
Legacy SQL now saves your query history so you can backtrack without rewriting from scratch. Past queries are stored with timestamps, filterable, and can be pinned or re-run directly from the history panel. Useful when you're mid-investigation and need to revisit a query you ran ten minutes ago without losing your current work.
AttackCapture
Improved Code Search
Files are now AI-categorized automatically, giving you intent and function classification without manual tagging. Facet filtering is broader with more dimensions to work with, and you can now exclude results using negative facets to cut out the noise fast. Keyword highlighting in file previews helps you spot what you're looking for without having to open and read through each file manually.
The search filters panel lets you narrow results across six dimensions: file name, extension, file type, hostname, file intent, and file function. Each filter supports free-text input and bucket selection, and you can combine multiple values using AND or OR logic, giving you the flexibility to cast a wider net or get very specific depending on what you're hunting for.
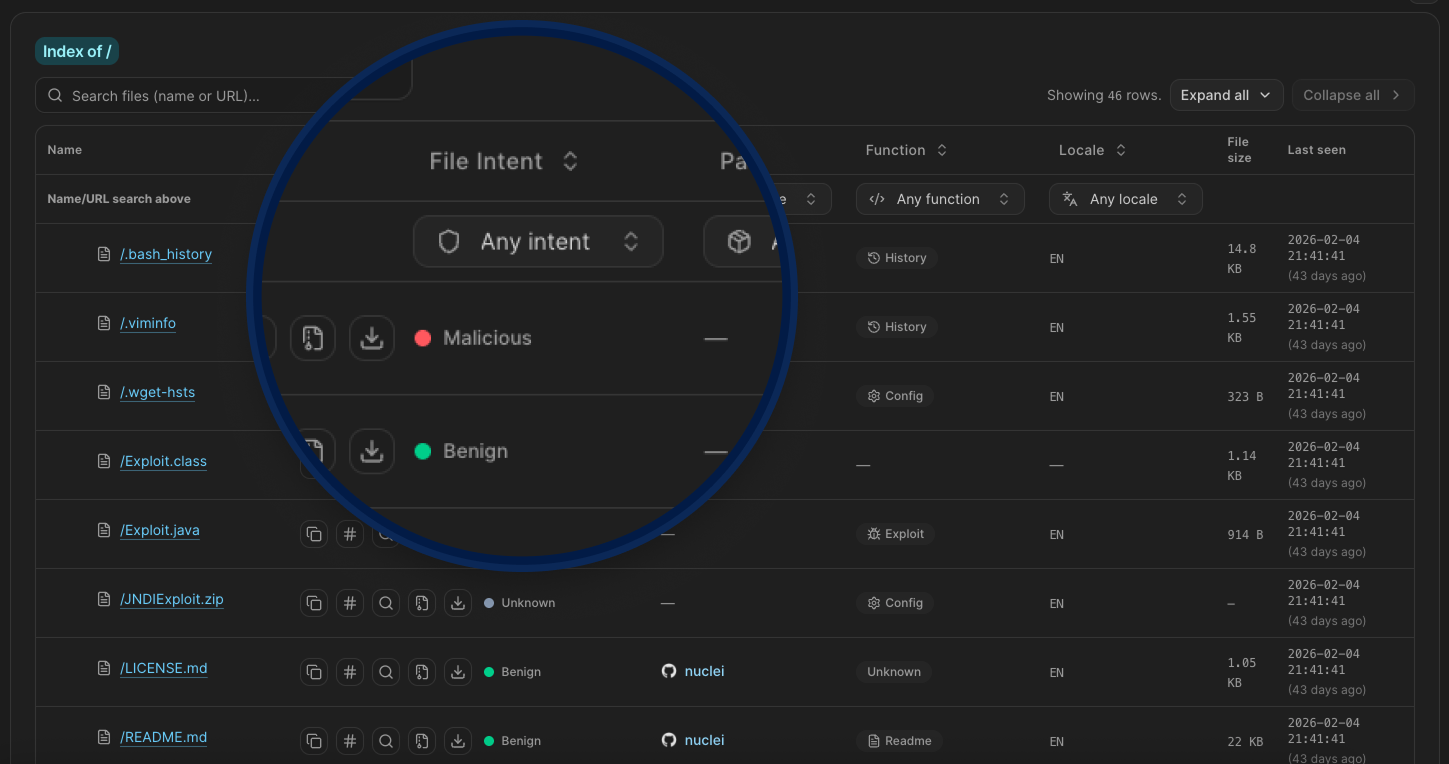
New Search Filters
Hunt 3.0 adds granular filtering to exposed open directory browsing inside AttackCapture. You can now filter files by:
Intent (Benign, Malicious, or Unknown),
Package type (currently nuclei),
Function (Config, Exploit, History, Readme, Target, or Unknown),
Locale, which gives you a direct signal on the operator's language and likely origin.
Instead of scrolling through hundreds of staged files trying to figure out what matters, you can cut straight to the exploits, configs, or target lists you actually care about.
Flagged Attacks
When threat actors leave operational directories exposed, Hunt.io captures what's inside before it disappears. Flagged Attacks turns that raw exposure data into structured campaign reports, each tied to specific IPs, IOCs, exploited CVEs, and attribution indicators. Not inferred, not modeled. Documented from direct observation of attacker infrastructure.
This gives hunters a fast way to check if an IP connects to a known operation, what tooling the actor is running, and what else belongs to the same infrastructure cluster. The kind of context that usually takes hours to piece together is already done.
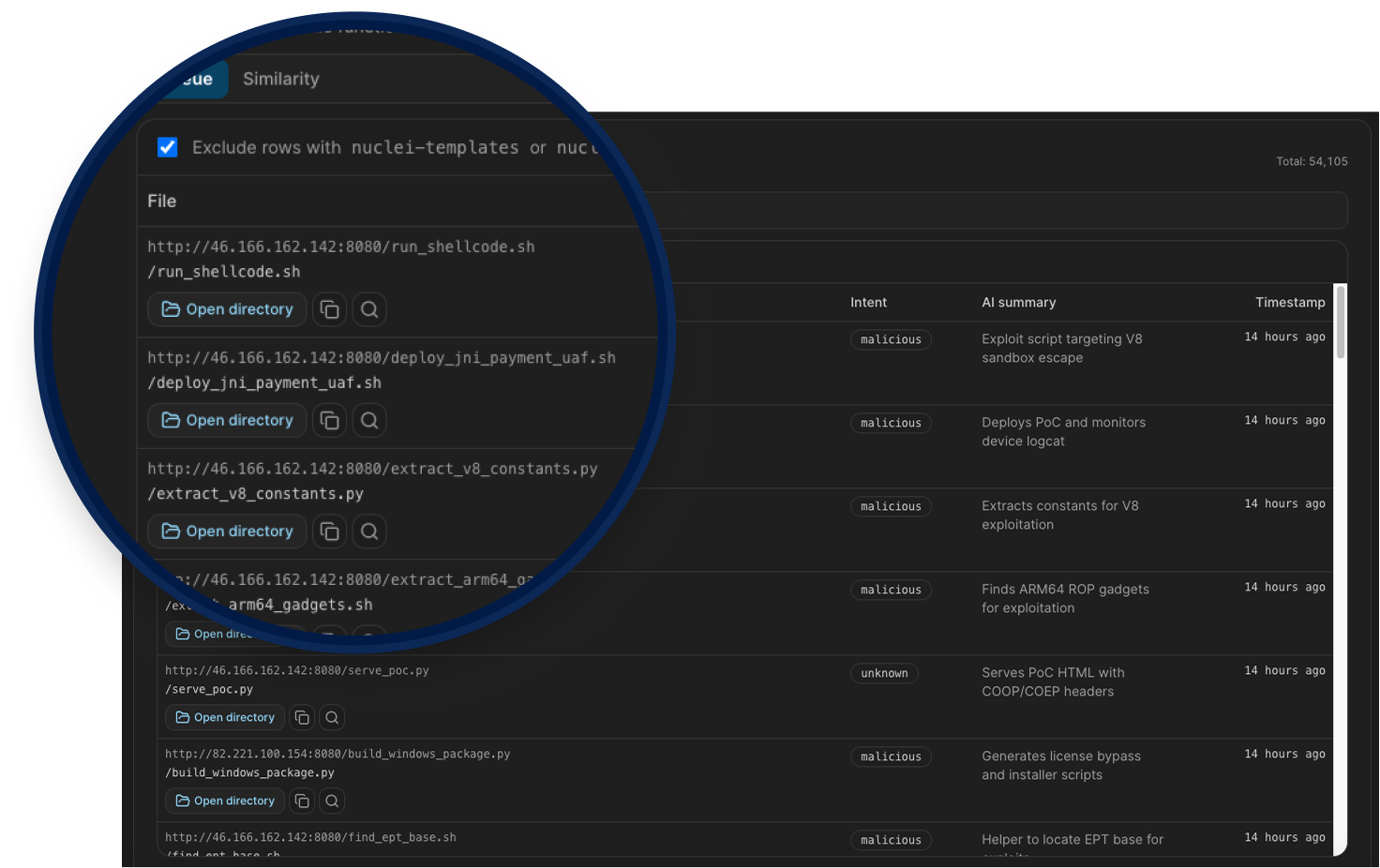
Exploit Capture
This is a dedicated queue inside AttackCapture that surfaces files AI-classified as exploits from exposed open directories, currently indexing over 54,000 files sorted newest first. From each entry, you can pivot directly into the parent open directory, preview file content, or copy the SHA256 hash for use in detections and YARA rules.
A toggle filters out nuclei template noise to keep the queue focused on what matters. The Similarity tab adds sidecar metadata for visible queue rows, helping you cluster related tooling across different attacker infrastructure.
For hunters and analysts, this is direct access to the actual tools attackers are staging and deploying in the wild.
Hunt v3 is a full rebuild, but the goal hasn't changed: give threat hunters better data, better context, and fewer dead ends. Every feature in this release was shaped by the investigations happening on the platform every day, and there's more coming. If something feels off or you have an idea for what we should tackle next, we'd love to hear it.
Related Posts
Related Posts
Related Posts