Exposing Russian Malicious Infrastructure: 1,250+ C2 Servers Mapped Across 165 Providers
Published on

Infrastructure analytics and ISP mapping reveal the hidden backbone of cyber threats. By examining hosting providers, cloud services, and telecom networks, analysts can identify patterns of persistent malware, phishing campaigns, and C2 infrastructure.
During the last three months (1 Jan 2026 - 1 Apr 2026) analysis window, we identified more than 1,250 active command-and-control (C2) servers operating across 165 Russian infrastructure providers, spanning shared hosting platforms, virtual server providers, and telecommunications networks.
That provider-level view is what separates actionable intelligence from an endless list of disposable indicators.
How We Analyzed Russian Malicious Infrastructure
Host Radar, a core module of Hunt.io, was designed to address this gap by correlating command-and-control servers, phishing infrastructure, malicious open directories, and public IOCs back to the hosting providers and network operators that sustain them.
Using Host Radar, we analyzed telemetry associated with Russian infrastructure providers. The results reveal not only the scale of active C2 infrastructure, but also the dominance of specific malware families, and the role of major cloud and telecom providers in supporting both commodity cybercrime and advanced threat operations.
This analysis surfaced clear patterns in how malicious infrastructure is distributed, reused, and concentrated across Russian hosting environments.
Before going deeper, these are the findings that shaped the entire analysis.
Key Takeaways
More than 1,250 C2 servers were identified across 165 Russian infrastructure providers within the past 3 months.
C2 infrastructure dominates malicious activity (~88.6%), far exceeding phishing infrastructure (~4.9%), while malicious open directories (~5.3%) and publicly reported IOCs (~1.2%) represent a much smaller portion of observed artifacts.
A small set of hosting providers accounts for a disproportionate share of malicious infrastructure, with TimeWeb, WebHost1, REG.RU, VDSina, and PROSPERO OOO hosting the largest volumes of detected C2 servers.
A small set of malware families (Keitaro, Hajime, Tactical RMM, Cobalt Strike, Sliver, and Ligolo-ng) showing framework-driven, repeatable abuse.
IoT-focused botnets (Hajime, Mozi, and Mirai) remain present within Russian infrastructure, reflecting ongoing abuse of compromised embedded devices and routers.
Russian hosting environments support diverse malicious operations, including phishing campaigns, infostealer distribution, scanning infrastructure, and targeted intrusion activity.
The hosting layer is where that concentration becomes most visible, so that is where we start.
Top Russian Infrastructure Providers
The Host Radar summary for the top five Russian infrastructure providers highlights the scale and diversity of malicious activity observed across these organizations over the last three months.
TimeWeb, a Russian web hosting and domain provider, exhibits the highest number of C2 servers among the analyzed Russian providers, with 311 detected over 90 days, alongside 7 malicious open directories, 91 port scanners, 0 IOCs, 3 IOC Hunter posts, and 9 phishing sites.
This activity suggests that large shared hosting environments with accessible infrastructure and flexible payment options can be attractive for attackers deploying C2 infrastructure and scanning operations.
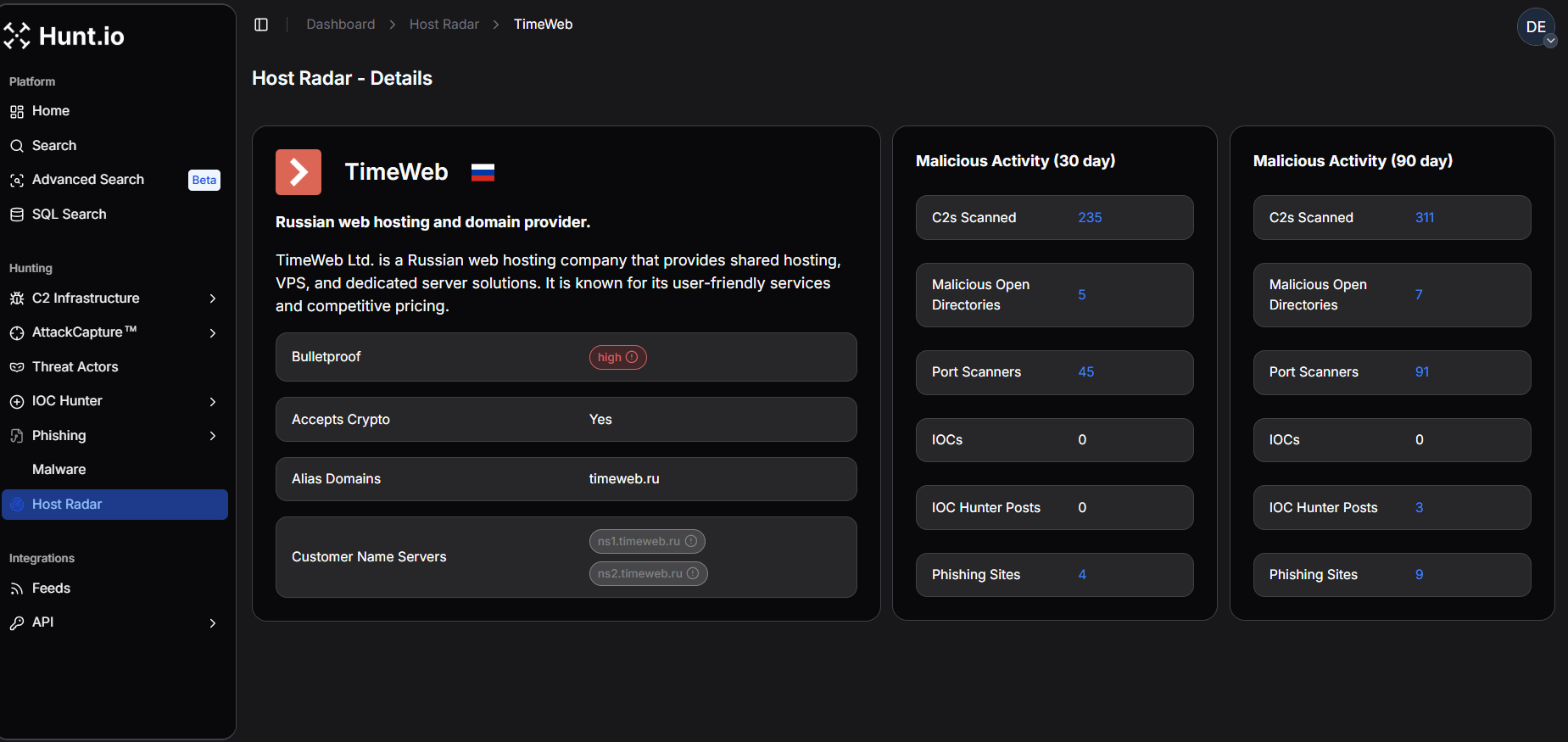 Figure 1. TimeWeb - Host Radar Detailed View: Per-provider Host Radar breakdown for TimeWeb, hi1ghlighting elevated C2 activity and associated scanning infrastructure.
Figure 1. TimeWeb - Host Radar Detailed View: Per-provider Host Radar breakdown for TimeWeb, hi1ghlighting elevated C2 activity and associated scanning infrastructure.Similarly, WebHost1, a hosting provider offering shared, VPS, and dedicated services, shows moderate C2 activity with 140 servers observed over 90 days, with no malicious open directories, port scanners, IOCs, IOC Hunter posts, or phishing sites detected.
This pattern indicates that while C2 infrastructure is present in the environment, there is little evidence of broader malicious artifacts, suggesting more isolated infrastructure use rather than large-scale abuse.
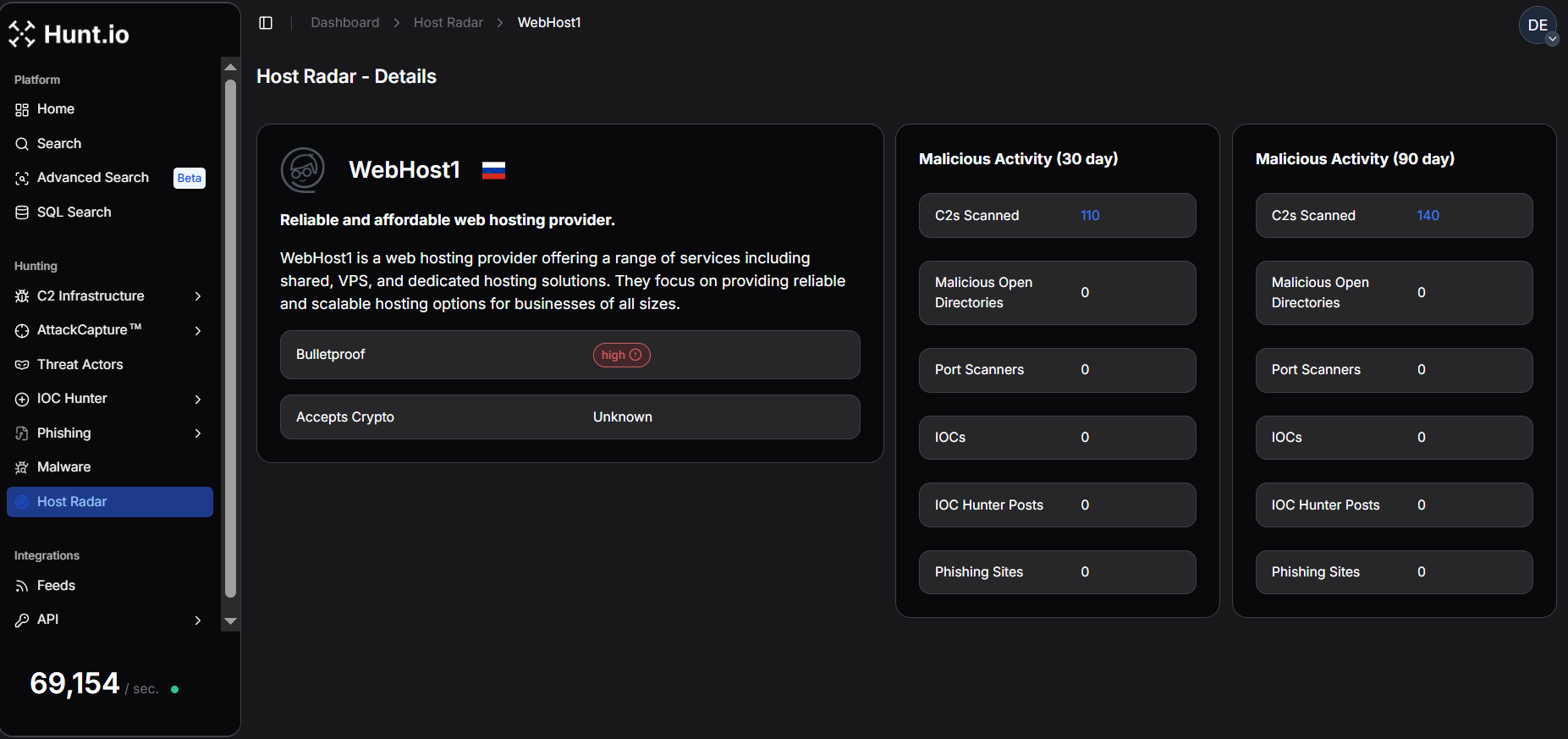 Figure 2. WebHost1 - Host Radar Detailed View: Host Radar metrics for WebHost1 illustrating moderate C2 infrastructure presence with limited associated malicious artifacts.
Figure 2. WebHost1 - Host Radar Detailed View: Host Radar metrics for WebHost1 illustrating moderate C2 infrastructure presence with limited associated malicious artifacts.REG.RU, one of Russia's leading domain registrars and hosting providers, exhibits a diverse malicious footprint. Over 90 days, it hosted 138 C2 servers, 38 port scanners, 0 IOCs, 4 IOC Hunter posts, and 2 phishing sites, while no malicious open directories were observed.
The presence of both scanning infrastructure and phishing campaigns indicates that domain and hosting providers supporting large numbers of customers may be leveraged for multiple stages of cyber operations, including reconnaissance and credential harvesting.
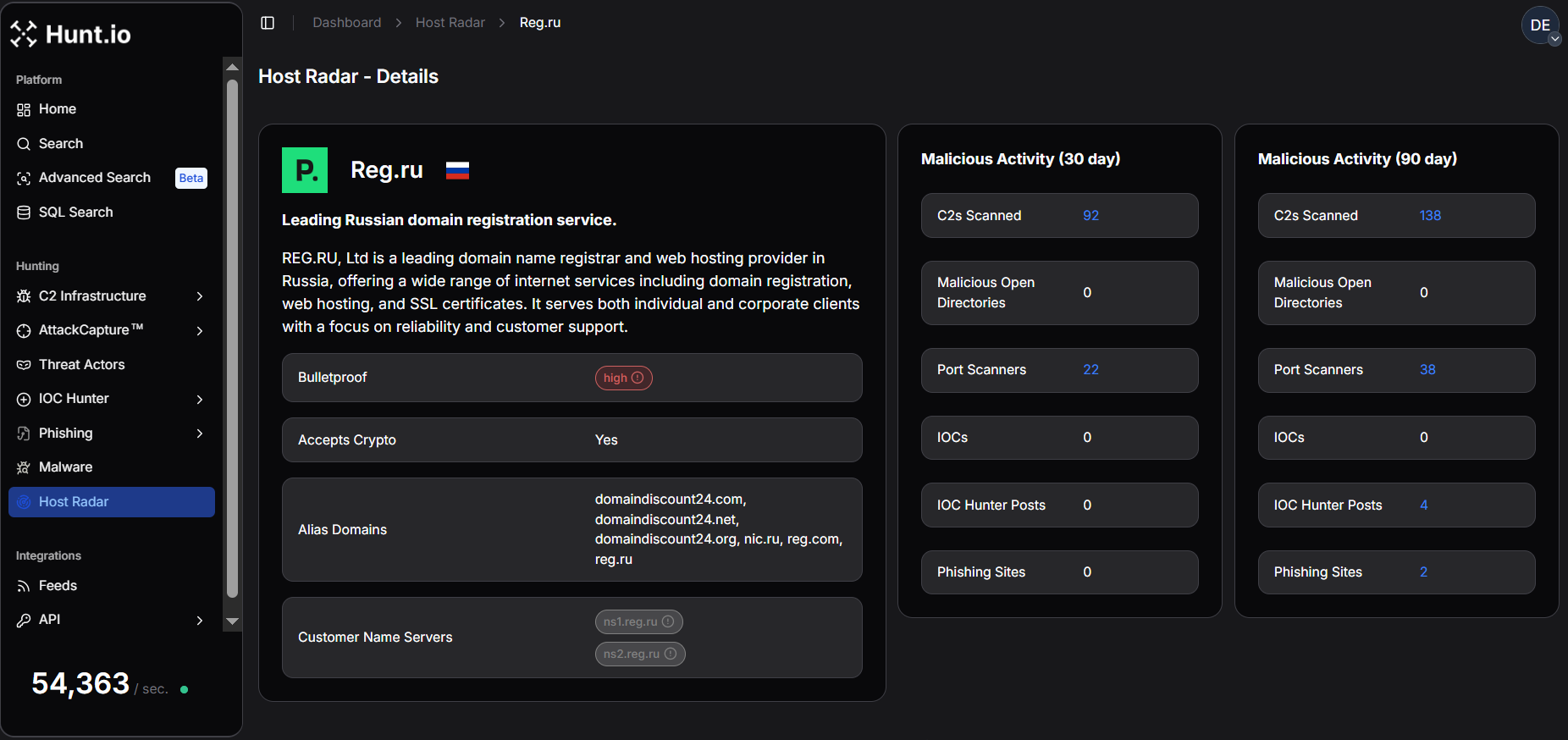 Figure 3. REG.RU - Host Radar Detailed View: Detailed Host Radar metrics showing REG.RU's mix of C2 infrastructure, port scanning activity, and phishing sites.
Figure 3. REG.RU - Host Radar Detailed View: Detailed Host Radar metrics showing REG.RU's mix of C2 infrastructure, port scanning activity, and phishing sites.In contrast, VDSina, a provider focused on virtual dedicated servers and cloud infrastructure, shows comparatively lower malicious activity, with 86 C2 servers, 2 malicious open directories, 4 port scanners, 4 IOCs, and 4 IOC Hunter posts detected over 90 days, while no phishing sites were observed.
This suggests a more limited but persistent presence of malicious infrastructure, likely tied to individual compromised or abused VPS instances.
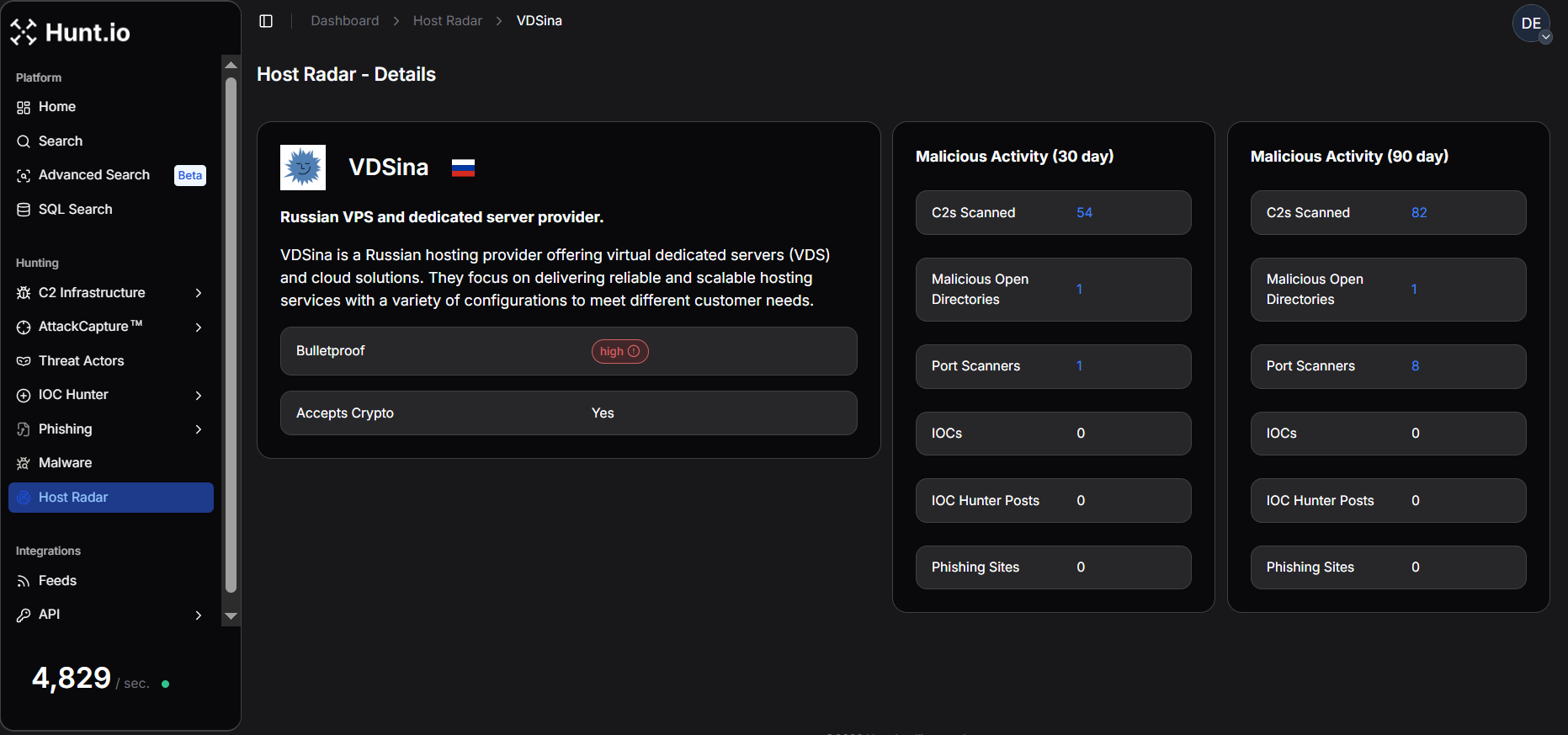 Figure 4. VDSina - Host Radar Detailed View: Host Radar metrics for VDSina reflecting relatively low but ongoing malicious infrastructure presence.
Figure 4. VDSina - Host Radar Detailed View: Host Radar metrics for VDSina reflecting relatively low but ongoing malicious infrastructure presence.PROSPERO OOO, a technology solutions provider offering hosting and infrastructure-related services, demonstrates a notable malicious footprint. Over 90 days, it hosted 80 C2 servers, 30 malicious open directories, 24 port scanners, 50 phishing sites, and 16 IOC Hunter posts, while no direct IOCs were recorded.
This combination indicates active reconnaissance and infrastructure staging, with scanning activity and exposed directories serving as precursors to broader malicious campaigns.
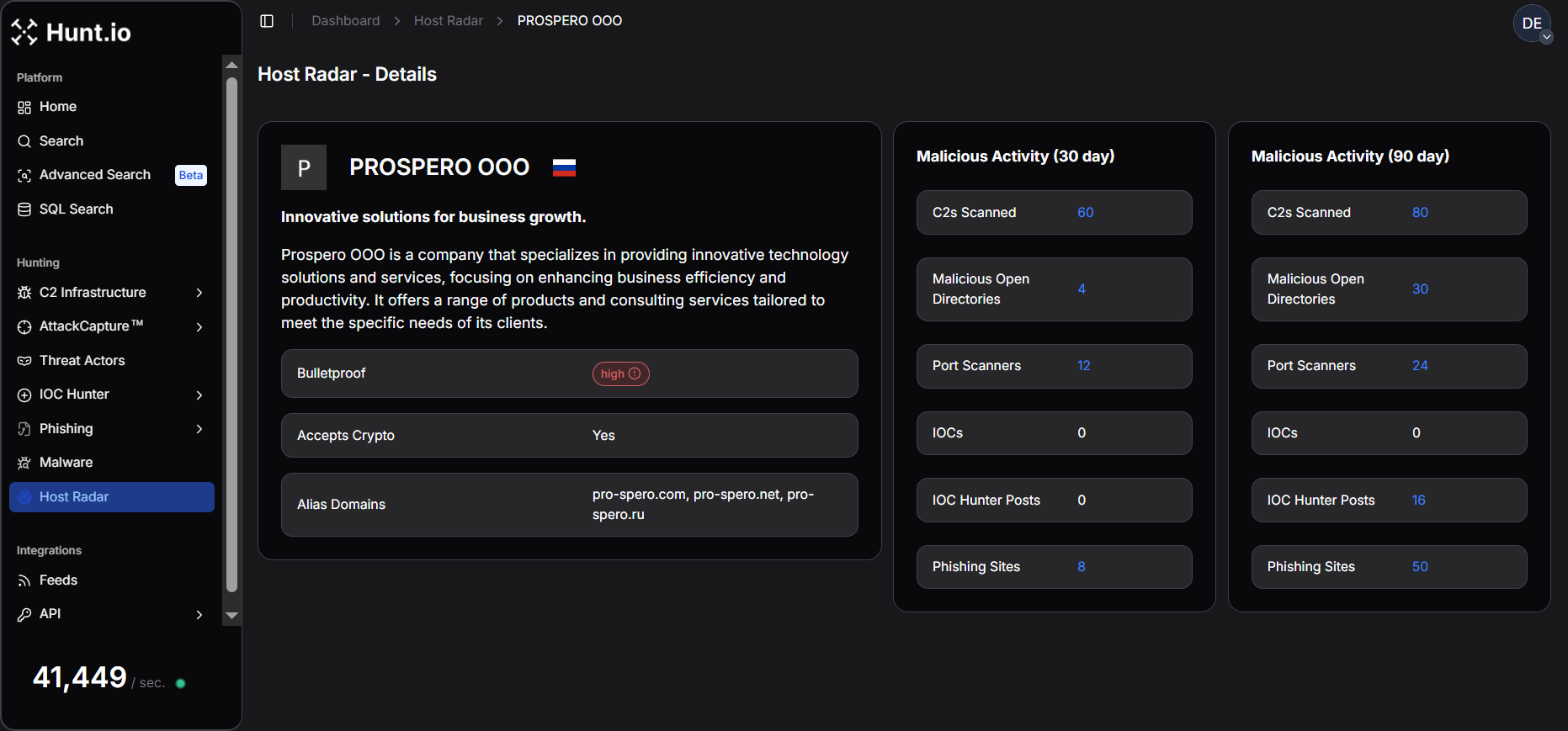 Figure 5. PROSPERO OOO - Host Radar Detailed View: Host Radar summary for the provider, highlighting command-and-control infrastructure alongside scanning activity.
Figure 5. PROSPERO OOO - Host Radar Detailed View: Host Radar summary for the provider, highlighting command-and-control infrastructure alongside scanning activity.With the top russian infrastructure hosting providers in mind, let's now focus on analyzing e the C2 infrastructure across different ISPs.
C2 Infrastructure Across Russian ISPs
This section describes how Host Radar was used to detect and attribute command-and-control (C2) infrastructure and related malicious artifacts operating within Russian hosting environments over a three-month observation window.
After applying the Russia country filter and restricting the observation window to the last three months, the Host Radar summary view reveals 165 distinct infrastructure providers and network entities operating within Russian ISPs, hosting providers, and cloud ecosystems that were associated with malicious activity.
This broad distribution shows the diversity of Russia's hosting ecosystem, where malicious infrastructure is spread across a large number of providers rather than concentrated in only a few networks.
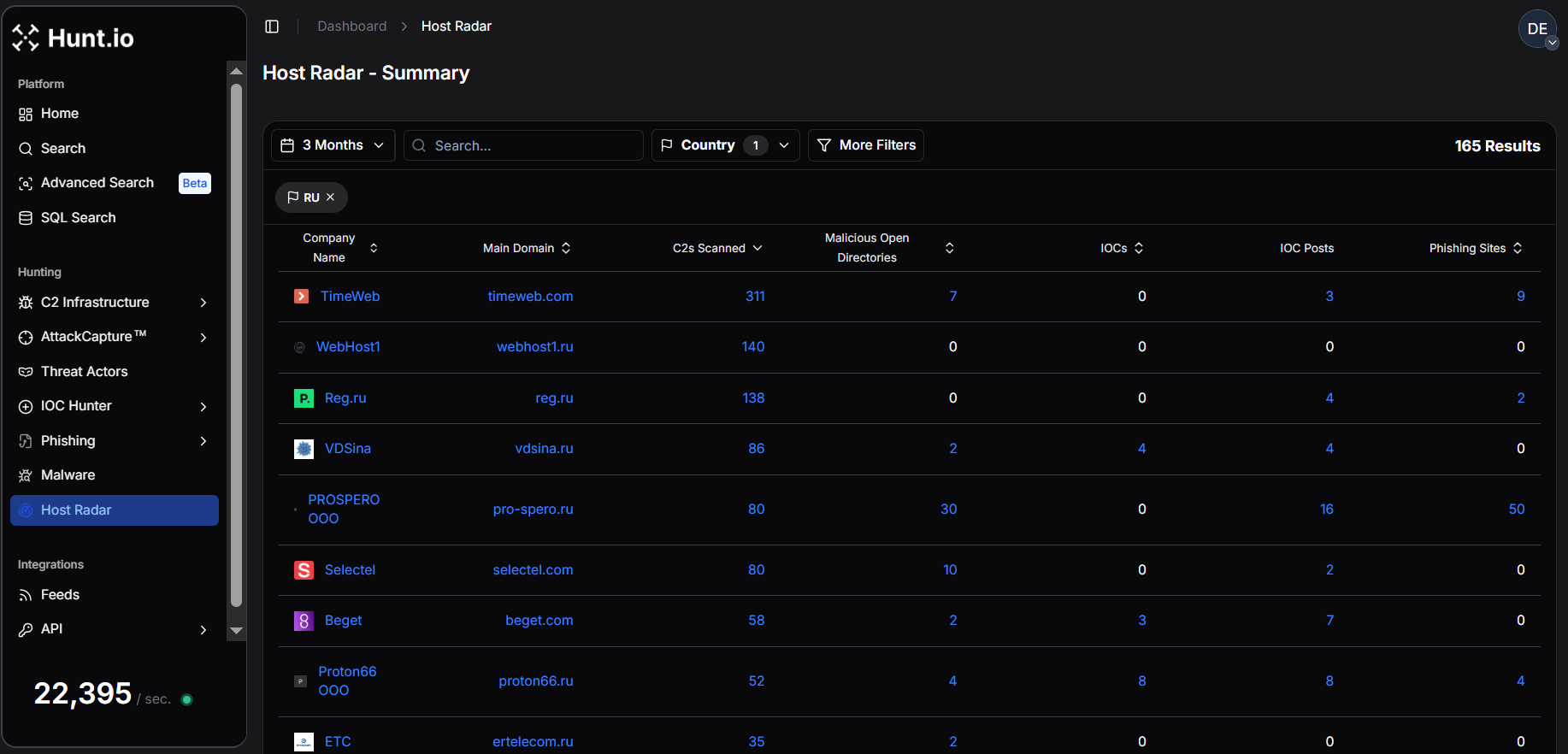 Figure 6. Host Radar summary view showing malicious infrastructure detected across 165 Russian ISPs and hosting providers over a three-month analysis window.
Figure 6. Host Radar summary view showing malicious infrastructure detected across 165 Russian ISPs and hosting providers over a three-month analysis window.Dataset Scope and Observed Infrastructure Landscape Over Russia
Across the full set of 165 Russian infrastructure providers, Host Radar recorded approximately 1,290 malicious artifacts during the three-month observation period. This includes 1,252 command-and-control (C2) servers, 75 malicious open directories, 17 indicators of compromise (IOCs) referenced in public research, and 69 phishing sites.
The data reveals that C2 infrastructure overwhelmingly dominates observed malicious activity, accounting for approximately 88.6% of all detected malicious artifacts. In comparison, malicious open directories represent about 5.3%, phishing infrastructure accounts for roughly 4.9%, while publicly reported IOCs contribute approximately 1.2% of the dataset.
This distribution suggests that Russian hosting environments are primarily leveraged for C2 operations, with fewer cases of exposed artifacts or publicly documented indicators compared to other infrastructure ecosystems.
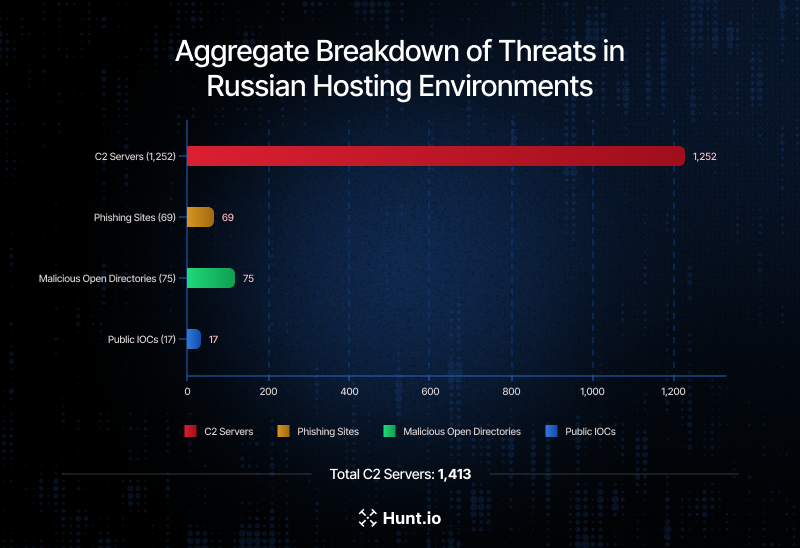 Figure 7. Aggregate breakdown of C2 servers (1,252), phishing sites (69), malicious open directories (75), and public IOCs (17) detected within Russian hosting environments.
Figure 7. Aggregate breakdown of C2 servers (1,252), phishing sites (69), malicious open directories (75), and public IOCs (17) detected within Russian hosting environments.Concentration of C2 Infrastructure Across Russian Providers
Moreover, the bar graph below visualizes the Top 10 companies by C2 server detections, where TimeWeb emerges as the most significant contributor with 311 detected C2 servers, representing the largest concentration of command-and-control infrastructure in this dataset.
This is followed by WebHost1 (140 C2 detections) and REG.RU (138 C2 detections), both large hosting providers serving a broad customer base. VDSina (86) and PROSPERO OOO (80) also appear among the most frequently abused infrastructure providers.
Other prominent providers include Selectel (80), Beget (58), Proton66 OOO (52), Er-Telecom (ETC) (35), and Rostelecom (27).
The presence of both commercial hosting companies and large telecommunications providers within the top rankings illustrates how virtual server platforms, cloud environments, and ISP networks can all be leveraged for malware C2 infrastructure deployment.
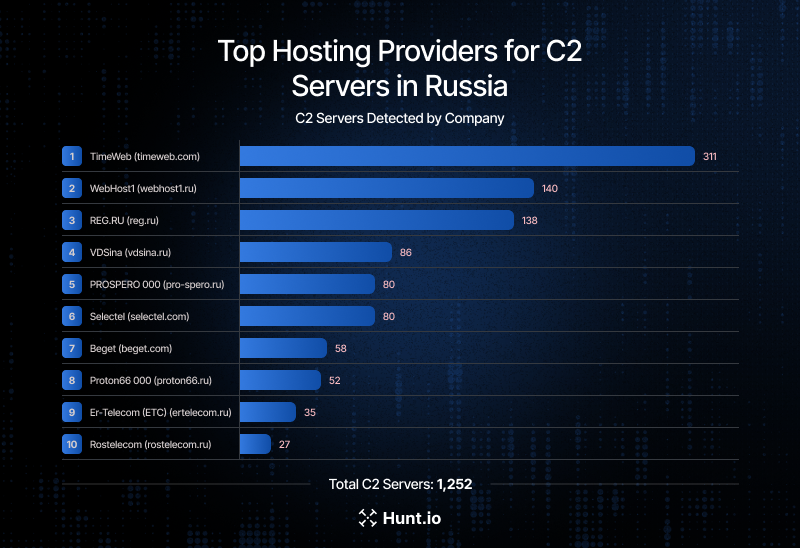 Figure 8. Top 10 Russian infrastructure providers by number of detected C2 servers over a three-month window, highlighting the distribution of malicious command-and-control infrastructure across hosting and telecom providers.
Figure 8. Top 10 Russian infrastructure providers by number of detected C2 servers over a three-month window, highlighting the distribution of malicious command-and-control infrastructure across hosting and telecom providers.Malware Family Distribution Within Russian Networks
Using HuntSQL, we analyzed the distribution of command-and-control (C2) infrastructure across malware families hosted within Russian networks over three months.
Example Query:
SELECT
malware.name,
uniq(ip) AS COUNTS
FROM
malware
WHERE
asn.country_name = 'Russia'
AND timestamp > NOW - 3 MONTH
GROUP BY
malware.name
ORDER BY
COUNTS DESC
CopyOutput Example:
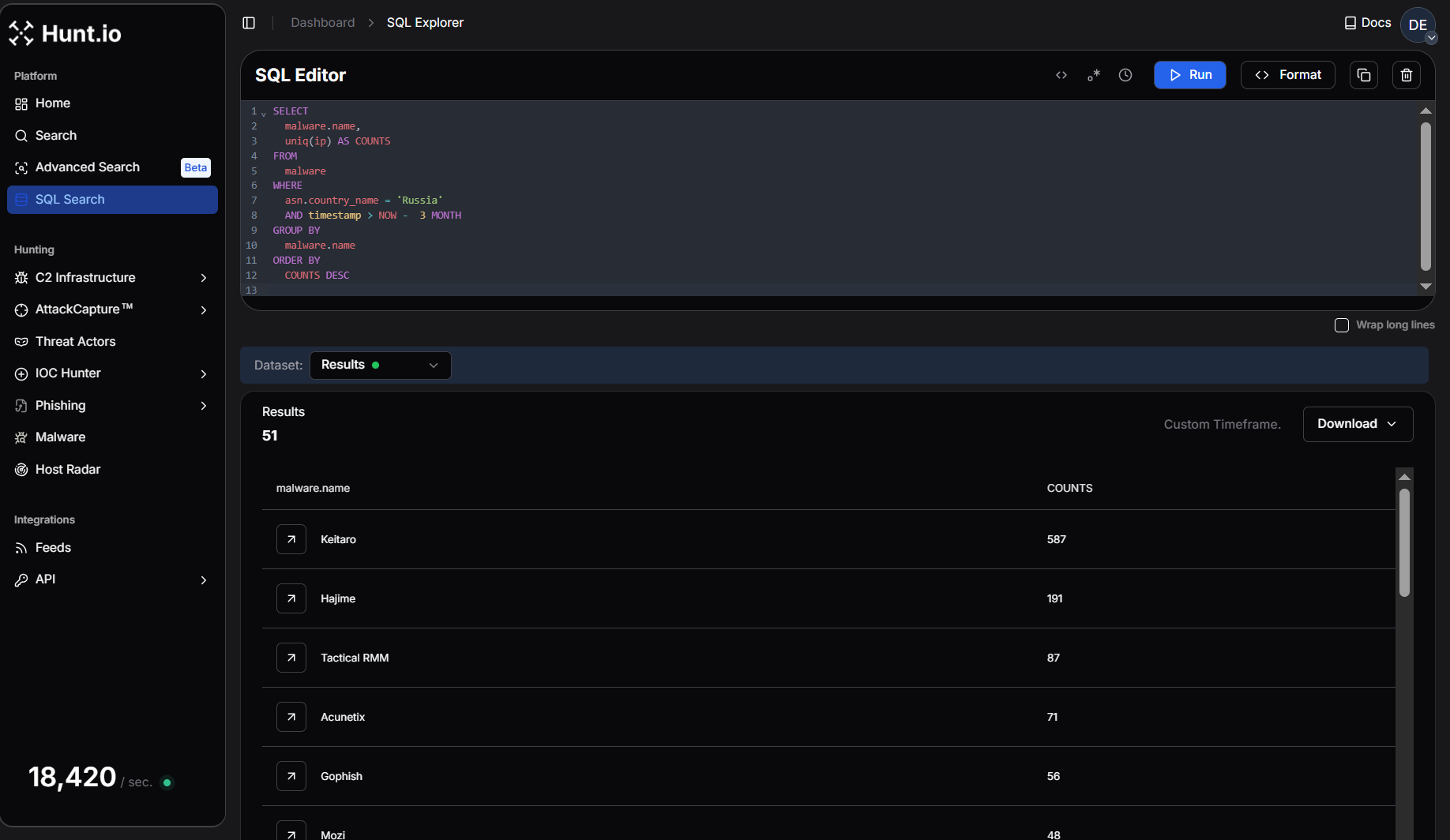 Figure 9. HuntSQL query output showing the dominant malware families hosting C2 infrastructure within Russian networks over three months.
Figure 9. HuntSQL query output showing the dominant malware families hosting C2 infrastructure within Russian networks over three months.The results reveal that Keitaro overwhelmingly leads the dataset with 587 unique C2 IPs, representing the largest concentration of command-and-control infrastructure observed in Russian hosting environments.
The second largest cluster, Hajime (191 C2s), reflects continued activity associated with IoT-focused botnet infrastructure, indicating that compromised embedded devices and routers continue to play a role in distributed malicious operations, followed by Mozi (48) and Mirai (13).
Several offensive security frameworks and post-exploitation platforms also appear prominently in the dataset. These include Tactical RMM (87), Cobalt Strike (25), Cobalt Strike Unverified (30), Sliver (24), and Ligolo-ng (10).
Scanning and phishing infrastructure tools such as Acunetix (71) and Interactsh (21) indicate vulnerability scanning, while Gophish (56) demonstrates the continued presence of phishing campaign infrastructure operating from Russian hosting environments.
This concentration lets defenders focus on shared infrastructure rather than individual malware variants rather than chasing individual malware variants.
.png) Figure 10. Bar graph illustrating the distribution of the Top 10 Malware Command-and-Control (C2) Families observed in Russia over the last three months.
Figure 10. Bar graph illustrating the distribution of the Top 10 Malware Command-and-Control (C2) Families observed in Russia over the last three months.Infrastructure Providers Hosting the Widest Malware Diversity
A HuntSQL query was designed to surface organizations hosting the widest variety of malware activity within Russian networks over the last three months. The query aggregates telemetry by org.name and calculates the number of distinct C2 IPs attributed to an organization (Unique_C2) as well as Unique_Malware, which reflects the diversity of malware families observed within that infrastructure.
Example Query:
SELECT
org.name,
uniq(ip) AS Unique_C2,
uniq(malware.name) AS Unique_Malware
FROM
malware
WHERE
org.name != ""
AND asn.country_name = 'Russia'
AND timestamp > NOW - 3 MONTH
GROUP BY
org.name
ORDER BY
Unique_Malware DESC
CopyOutput Example:
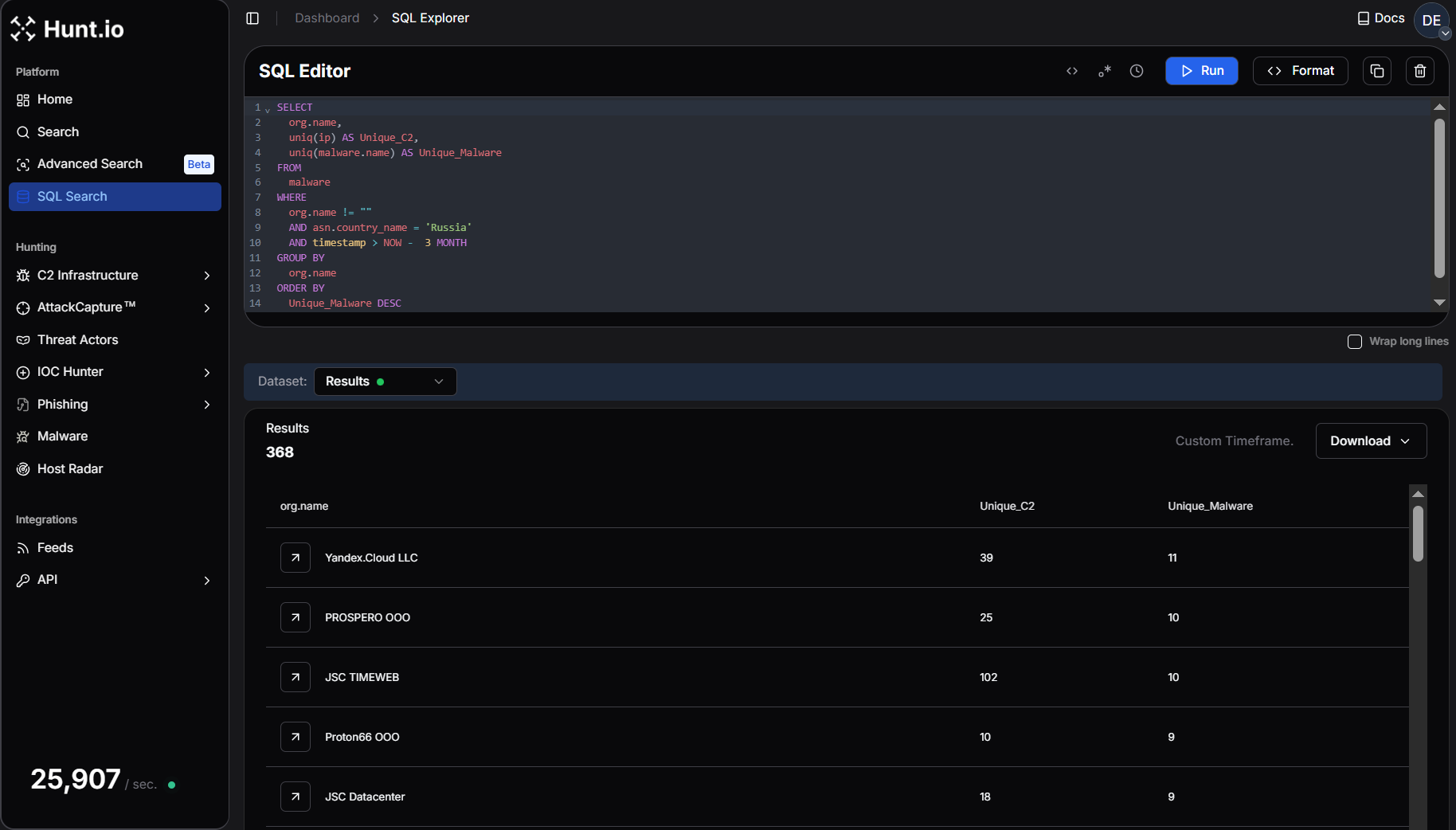 Figure 11. A HuntSQL query aggregating malware telemetry by a Russian organization to identify providers hosting the widest variety of malware families.
Figure 11. A HuntSQL query aggregating malware telemetry by a Russian organization to identify providers hosting the widest variety of malware families.The results reveal that malware activity is concentrated within a relatively small set of hosting and cloud providers, many of which support large-scale virtual server and hosting environments.
Yandex.Cloud LLC leads in malware diversity, hosting 11 distinct malware families across 39 unique C2 endpoints, followed by JSC TIMEWEB, which hosts 10 distinct malware families across 102 unique C2 endpoints. PROSPERO OOO also hosts 10 malware families associated with 25 unique C2 endpoints, while JSC Datacenter hosts 9 malware families across 18 C2 endpoints.
Other providers with notable malware diversity include Proton66 OOO (9 malware families), Hosting Technology LTD (8), LLC Baxet (8), and Selectel Network (7).
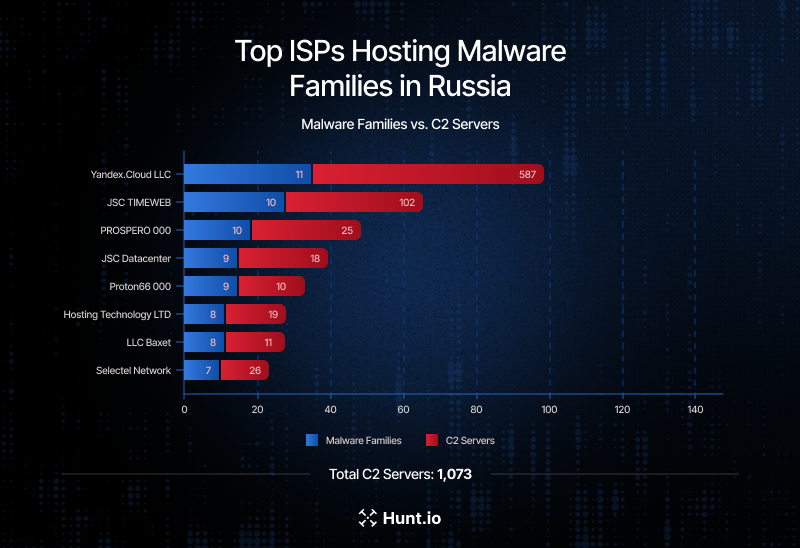 Figure 12. Malware Diversity vs. C2 Volume Across Russian ISPs - TIMEWEB leads in C2 density, while Yandex.Cloud hosts the widest range of malware families.
Figure 12. Malware Diversity vs. C2 Volume Across Russian ISPs - TIMEWEB leads in C2 density, while Yandex.Cloud hosts the widest range of malware families.Malicious Campaigns Observed Across Russian Hosting Environments
The following examples illustrate how the infrastructure patterns identified above translate into active malware campaigns, phishing operations, botnet activity, and targeted intrusion campaigns within Russian hosting environments.
Over the same period, Hunt.io tracking surfaced several malicious command-and-control (C2) endpoints hosted across Russian infrastructure providers, beginning with activity linked to Latrodectus malware hosted on JSC TIMEWEB infrastructure. The IP 85.239.54[.]130 was associated with a campaign analyzed by CERT Polska, where attackers leveraged a fake CAPTCHA "ClickFix" technique to trick users into executing a curl-to-PowerShell command.
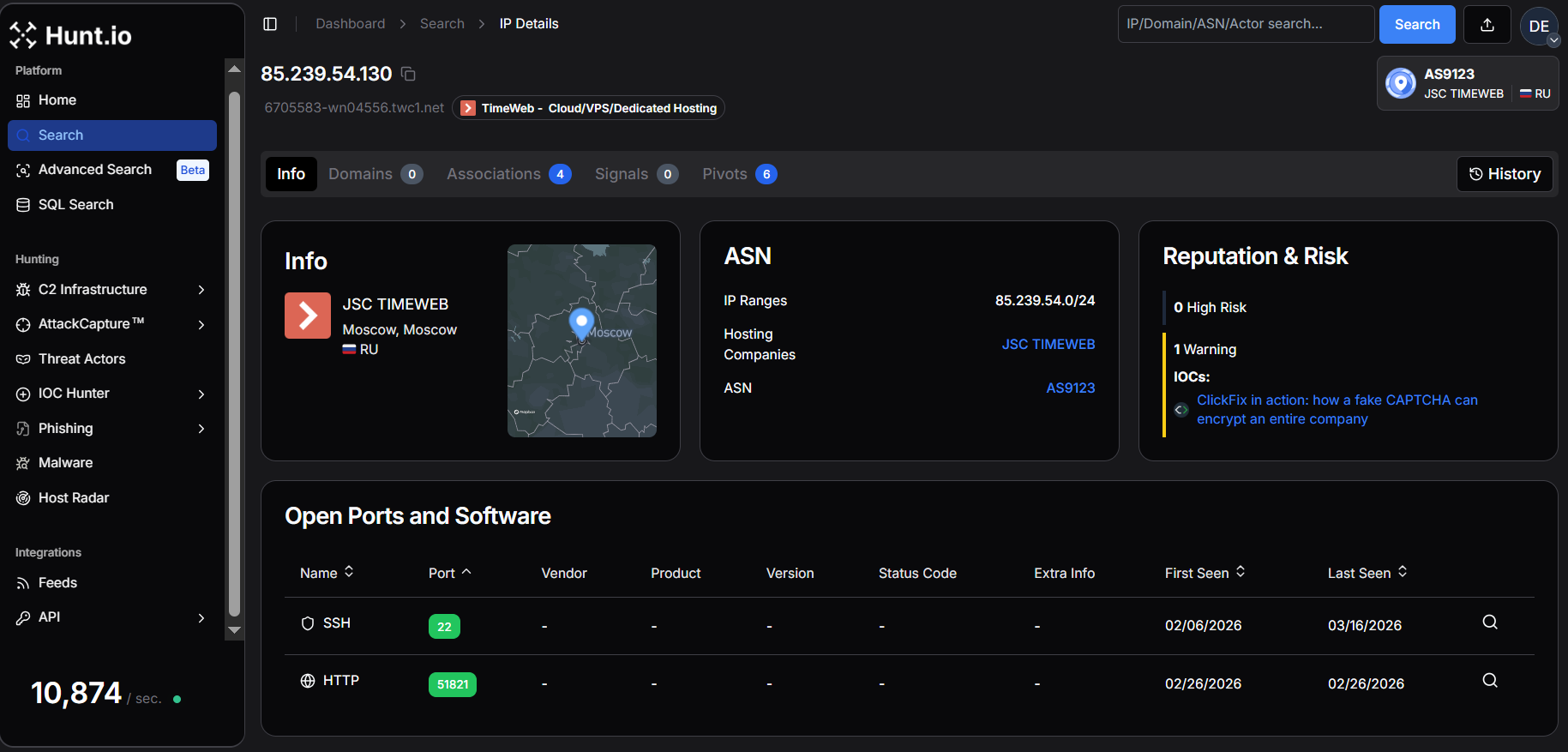 Figure 13. Hunt.io IP intelligence highlighting JSC TimeWeb infrastructure (AS9123) with ClickFix (Fake CAPTCHA Attack) risk indicators.
Figure 13. Hunt.io IP intelligence highlighting JSC TimeWeb infrastructure (AS9123) with ClickFix (Fake CAPTCHA Attack) risk indicators.Once executed, the command downloaded malicious payloads including Latrodectus v2.3, which communicated with attacker-controlled domains such as gasrobariokley[.]com and fadoklismokley[.]com.
Another example involved infrastructure hosted on REG.RU, where the IP 89.111.170[.]100 was linked to a Lumma Stealer malware campaign documented by CTM360. The operation abused Google Groups and Google-hosted redirectors to distribute malicious payloads across both Windows and Linux systems. Windows victims received large padded archives reconstructing AutoIt-based Lumma Stealer payloads, while Linux users were targeted with a trojanized Chromium variant known as Ninja Browser that installed malicious extensions and enabled persistent remote control of infected systems.
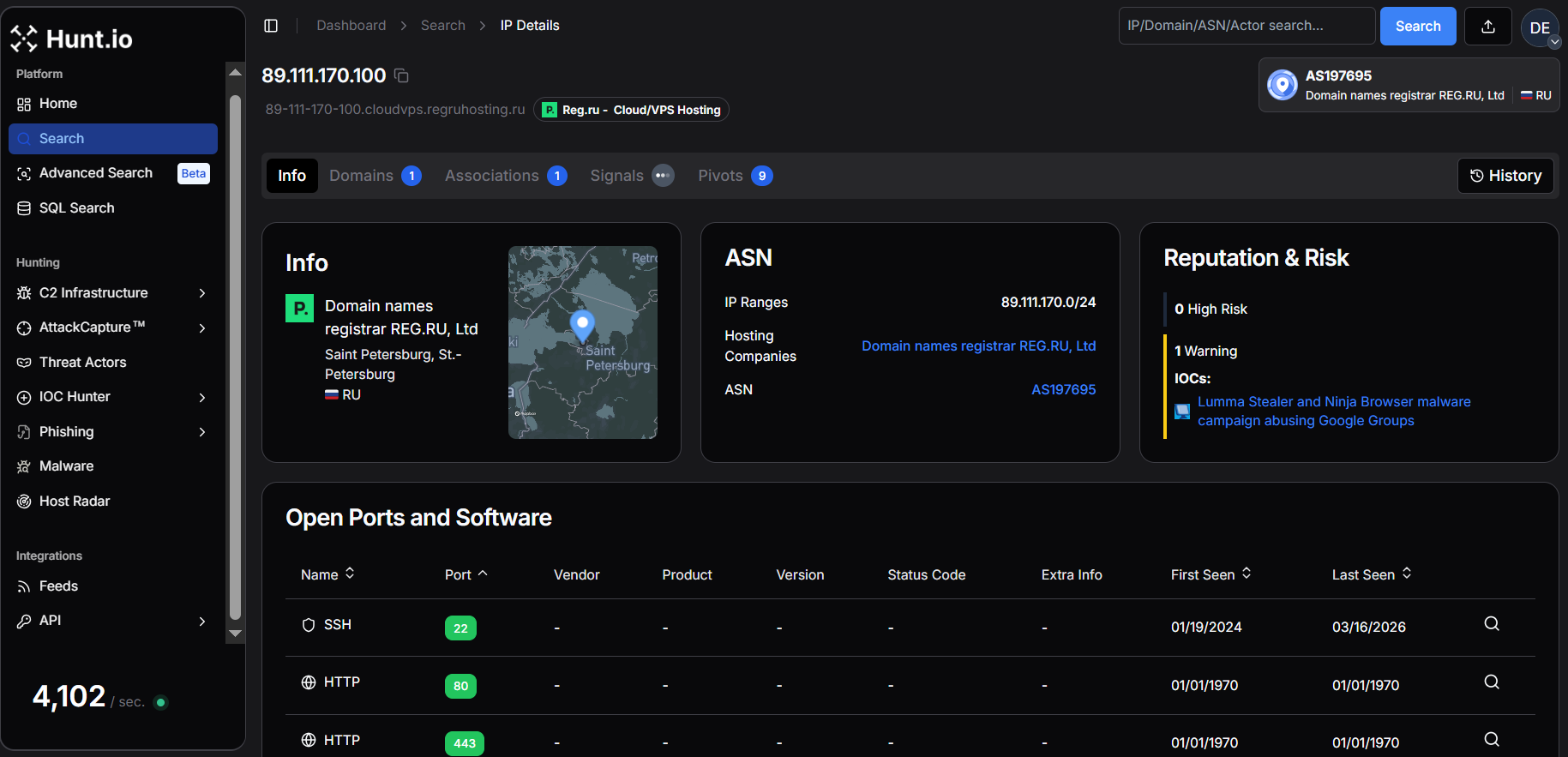 Figure 14. Hunt.io IP intelligence for 89.111.170[.]100 hosted by REG.RU Ltd (AS197695), linked to Lumma Stealer & Ninja Browser malware campaign.
Figure 14. Hunt.io IP intelligence for 89.111.170[.]100 hosted by REG.RU Ltd (AS197695), linked to Lumma Stealer & Ninja Browser malware campaign.Additional post-exploitation activity was identified on infrastructure belonging to Hosting Technology LTD, where the IP 193.178.170[.]155 was tied to the SmartApeSG campaign delivering Remcos RAT. In this campaign, attackers injected malicious JavaScript into compromised websites that displayed fake CAPTCHA prompts instructing users to execute commands copied to the clipboard. The execution downloaded a ZIP archive disguised as a PDF file that installed Remcos RAT via DLL sideloading, establishing persistence and connecting back to the attacker-controlled C2 server over TLS.
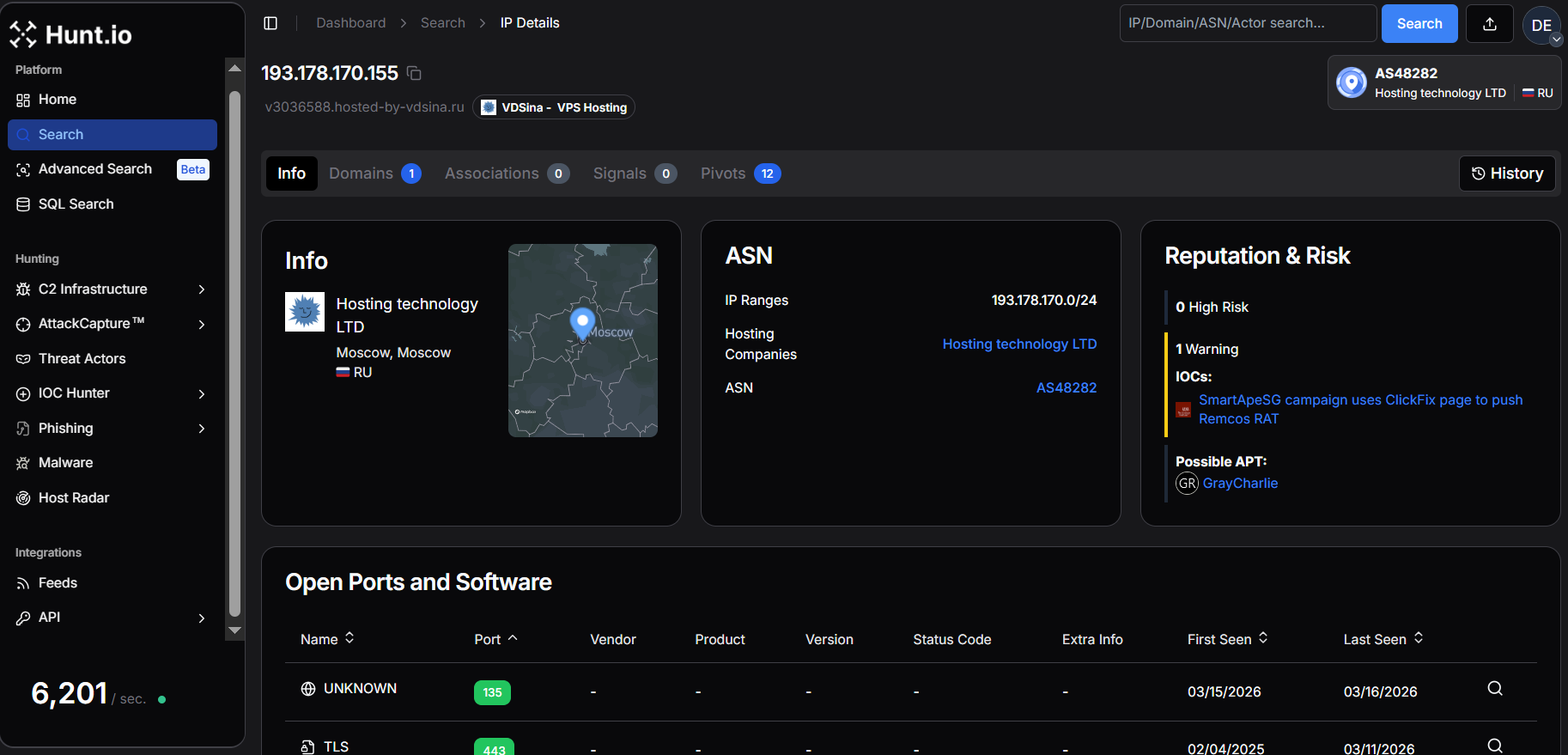 Figure 15. Hunt.io IP intelligence for 193.178.170[.]155 hosted by Hosting Technology LTD (AS48282), linked to SmartApeSG campaign delivering Remcos RAT and possible GrayCharlie APT activity.
Figure 15. Hunt.io IP intelligence for 193.178.170[.]155 hosted by Hosting Technology LTD (AS48282), linked to SmartApeSG campaign delivering Remcos RAT and possible GrayCharlie APT activity.Infrastructure hosted by Beget LLC appeared repeatedly across several campaigns. One example includes 85.198.98[.]75, which was associated with a phishing operation tracked as UAC-0252. The campaign impersonated Ukrainian government institutions and distributed archives containing executable files that ultimately deployed SHADOWSNIFF and SALATSTEALER infostealers, alongside a DEAFTICK backdoor. The operation relied on GitHub-hosted payloads and exploited a WinRAR vulnerability (CVE-2025-8088) to facilitate infection.
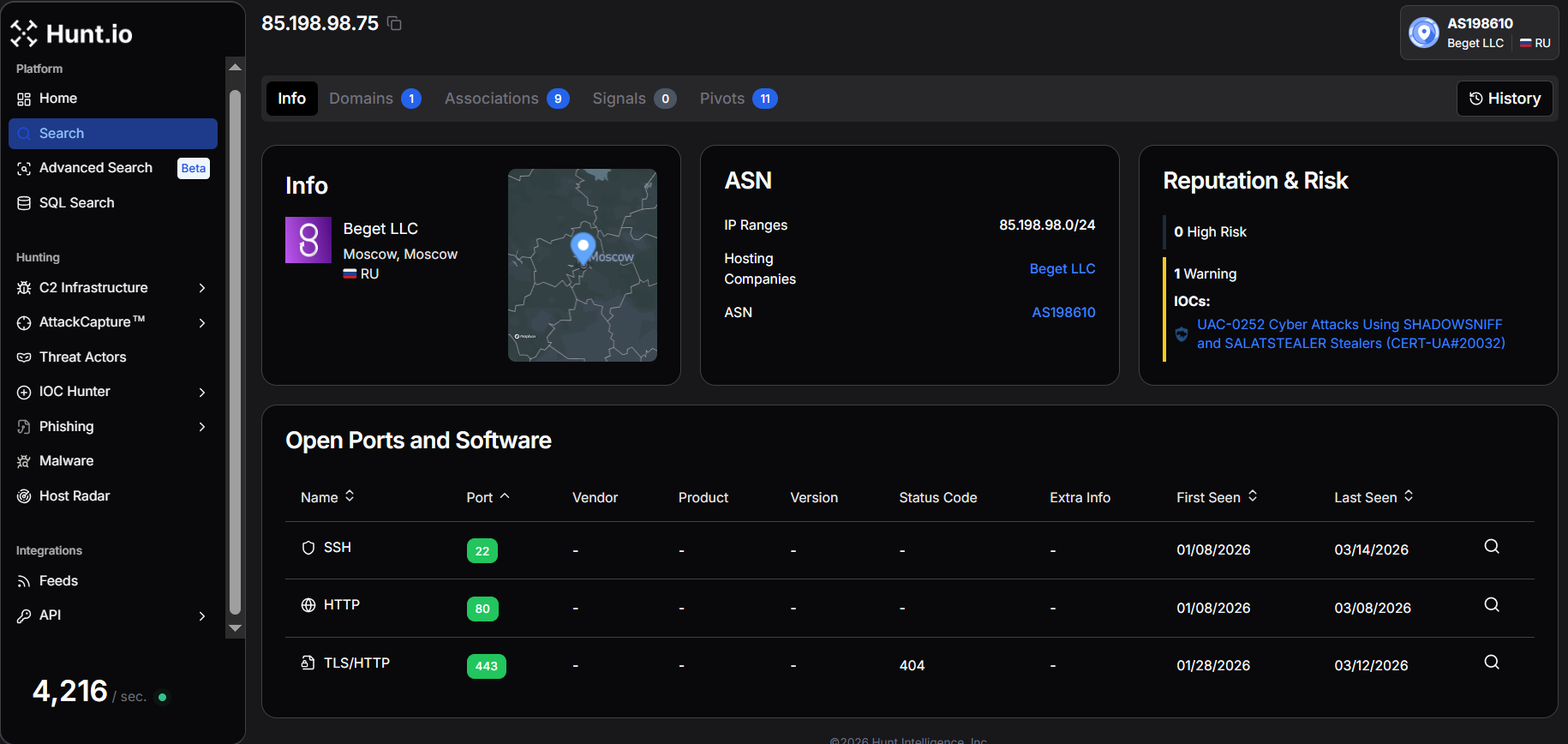 Figure 16. Hunt.io IP intelligence for 85.198.98[.]75 hosted by Beget LLC (AS198610), linked to UAC-0252 activity using SHADOWSNIFF & SALATSTEALER
Figure 16. Hunt.io IP intelligence for 85.198.98[.]75 hosted by Beget LLC (AS198610), linked to UAC-0252 activity using SHADOWSNIFF & SALATSTEALERSimilarly, another IP 45.130.41[.]81 was linked to the Diesel Vortex operation, a phishing-as-a-service platform branded Global Profit / MC Profit Always targeting logistics and transportation companies. Researchers recovered campaign infrastructure revealing Telegram-based coordination between operators, large-scale credential harvesting, and social-engineering operations, including voice phishing designed to enable cargo diversion and financial fraud.
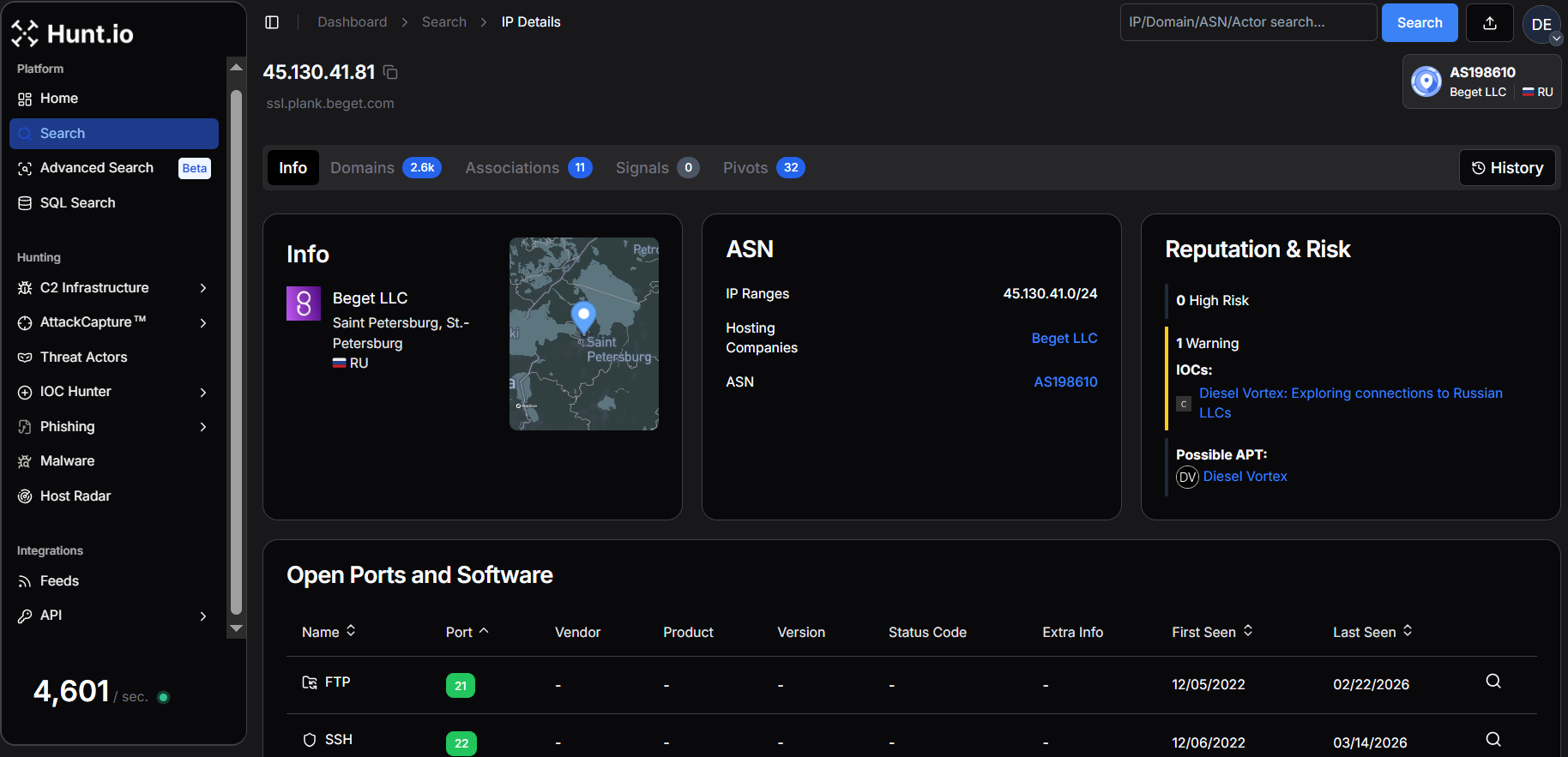 Figure 17. Hunt.io IP intelligence for 45.130.41[.]81 hosted by Beget LLC (AS198610), linked to Diesel Vortex activity and related infrastructure.
Figure 17. Hunt.io IP intelligence for 45.130.41[.]81 hosted by Beget LLC (AS198610), linked to Diesel Vortex activity and related infrastructure.Another IP 45.146.164[.]110 appeared in SSH honeypot telemetry, where analysts used HASSH fingerprinting to identify coordinated botnet activity leveraging the same libssh-based tooling across multiple IP addresses.
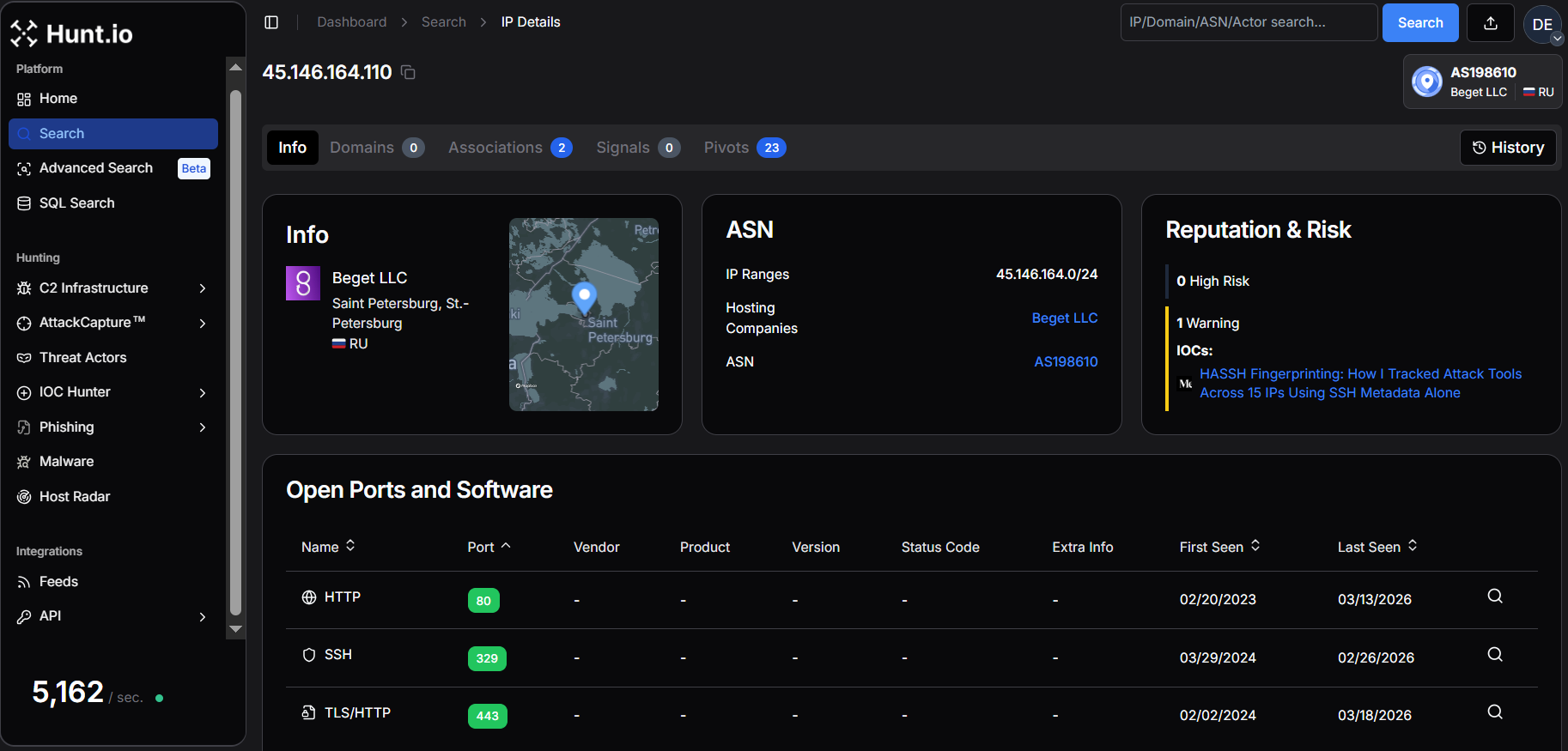 Figure 18. Hunt.io IP intelligence for 45.146.164[.]110 hosted by Beget LLC (AS198610), linked to HASSH fingerprinting-based threat tracking activity.
Figure 18. Hunt.io IP intelligence for 45.146.164[.]110 hosted by Beget LLC (AS198610), linked to HASSH fingerprinting-based threat tracking activity.In another research by Recorded Future, the researchers identified a campaign attributed to GrayCharlie, where compromised WordPress sites injected malicious JavaScript redirecting visitors to NetSupport RAT payloads. Infrastructure linked to this campaign included 217.114.15[.]253 and 45.153.191[.]245, both hosted by Beget LLC, demonstrating how compromised websites can serve as staging infrastructure for broader malware distribution.
A targeted intrusion activity was identified within infrastructure hosted by LLC Smart Ape, where multiple IPs, including 178.255.127[.]65, 188.127.227[.]46, and 188.127.254[.]233 were associated with operations attributed to the Head Mare threat group. According to Kaspersky's analysis, the campaign deployed a PowerShell backdoor called PhantomHeart alongside a rewritten proxy tool PhantomProxyLite. The malware leveraged AES-encrypted C2 communications, persistence through scheduled tasks, and reverse SSH tunneling to maintain long-term access within compromised environments.
Another notable campaign leveraged infrastructure hosted by Proton66 OOO, where the IP 193.143.1[.]104 was linked to a large-scale BoryptGrab infostealer operation. Researchers identified more than 100 public GitHub repositories being abused to distribute malware, with attackers using SEO manipulation and deceptive GitHub Pages (github[.]io) sites posing as legitimate tools and game cheats.
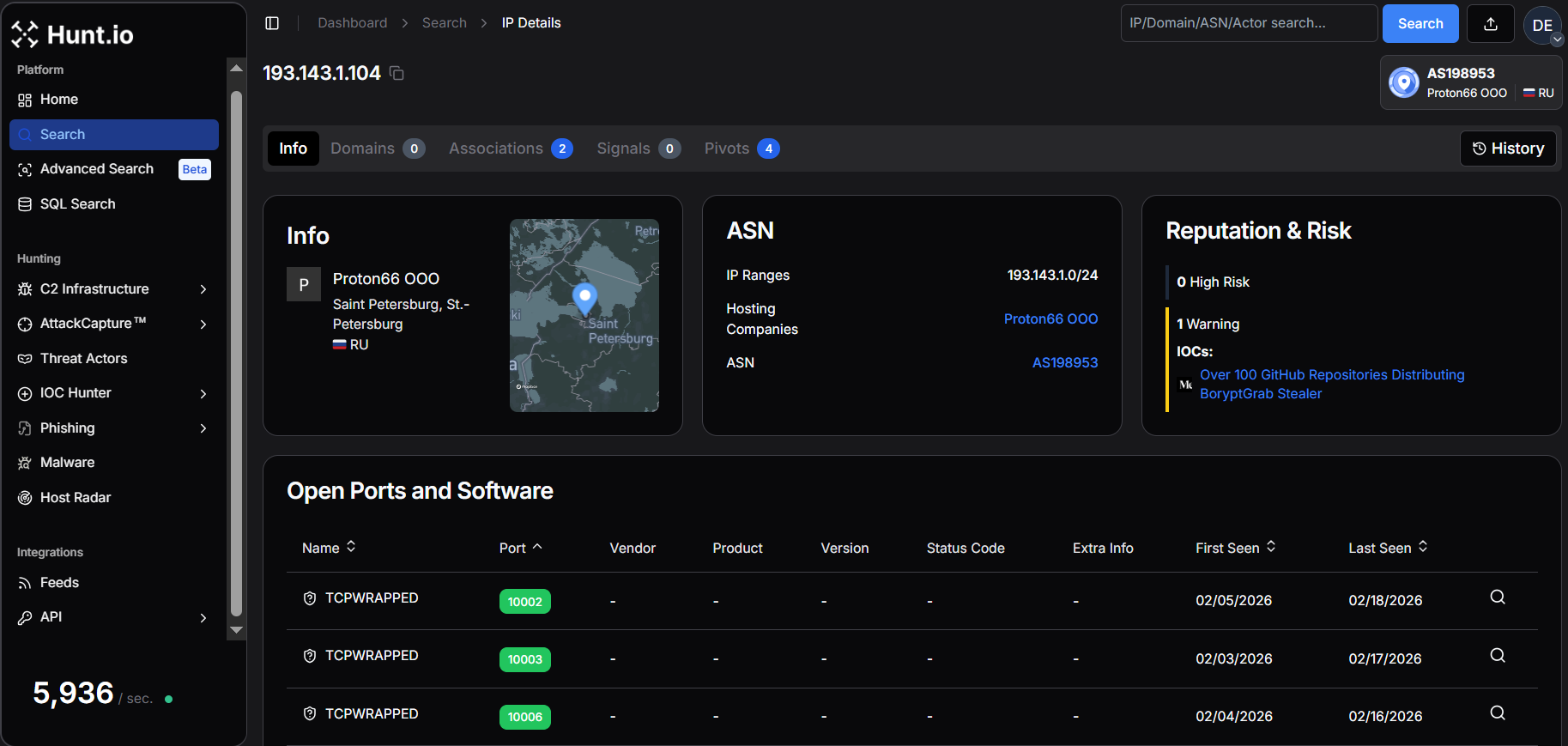 Figure 19. Hunt.io IP intelligence for 193.143.1[.]104 hosted by Proton66 OOO (AS198953), linked to BoryptGrab stealer distribution campaign.
Figure 19. Hunt.io IP intelligence for 193.143.1[.]104 hosted by Proton66 OOO (AS198953), linked to BoryptGrab stealer distribution campaign.These examples demonstrate how Russian hosting providers support a diverse threat landscape, ranging from phishing-driven infostealer campaigns and botnet activity to advanced intrusion operations and malware distribution infrastructure.
Infrastructure Observables
This research is based on a large set of infrastructure-level observables, including IP addresses, domains, and C2 endpoints that Hunt.io has identified and labeled as malicious infrastructure, active malware command-and-control, phishing infrastructure, or related abuse across Russian ISPs and hosting providers.
Given the scale of the dataset, with more than 1,250 active C2 endpoints observed over three months, publishing a static list here would provide limited operational value.
Teams interested in accessing this data with proper context, attribution, and historical tracking can reach out to discuss research collaboration or operational access to the full dataset.
Conclusion
This research shows the malicious activity in Russian hosting environments is heavily concentrated, with over 1,250 C2 servers spread across 165 providers, with TimeWeb, REG.RU, WebHost1, VDSina, and PROSPERO OOO hosting the majority of high-risk infrastructure, highlighting persistent reuse by threat actors.
A host-centric view of Russian infrastructure allows security teams to prioritize high-risk providers, track malware reuse, and implement mitigation strategies that disrupt attacker operations at scale, providing clearer visibility into the nation's threat landscape.
For security teams, this approach enables more resilient detection, faster prioritization, and infrastructure-level disruption strategies that are difficult for adversaries to evade. Host Radar and HuntSQL make this type of analysis practical by combining large-scale telemetry with flexible, analyst-driven investigation workflows.
If you want to explore this host-centric view of malicious infrastructure firsthand, you can see how Host Radar works in practice by booking a demo today.
Infrastructure analytics and ISP mapping reveal the hidden backbone of cyber threats. By examining hosting providers, cloud services, and telecom networks, analysts can identify patterns of persistent malware, phishing campaigns, and C2 infrastructure.
During the last three months (1 Jan 2026 - 1 Apr 2026) analysis window, we identified more than 1,250 active command-and-control (C2) servers operating across 165 Russian infrastructure providers, spanning shared hosting platforms, virtual server providers, and telecommunications networks.
That provider-level view is what separates actionable intelligence from an endless list of disposable indicators.
How We Analyzed Russian Malicious Infrastructure
Host Radar, a core module of Hunt.io, was designed to address this gap by correlating command-and-control servers, phishing infrastructure, malicious open directories, and public IOCs back to the hosting providers and network operators that sustain them.
Using Host Radar, we analyzed telemetry associated with Russian infrastructure providers. The results reveal not only the scale of active C2 infrastructure, but also the dominance of specific malware families, and the role of major cloud and telecom providers in supporting both commodity cybercrime and advanced threat operations.
This analysis surfaced clear patterns in how malicious infrastructure is distributed, reused, and concentrated across Russian hosting environments.
Before going deeper, these are the findings that shaped the entire analysis.
Key Takeaways
More than 1,250 C2 servers were identified across 165 Russian infrastructure providers within the past 3 months.
C2 infrastructure dominates malicious activity (~88.6%), far exceeding phishing infrastructure (~4.9%), while malicious open directories (~5.3%) and publicly reported IOCs (~1.2%) represent a much smaller portion of observed artifacts.
A small set of hosting providers accounts for a disproportionate share of malicious infrastructure, with TimeWeb, WebHost1, REG.RU, VDSina, and PROSPERO OOO hosting the largest volumes of detected C2 servers.
A small set of malware families (Keitaro, Hajime, Tactical RMM, Cobalt Strike, Sliver, and Ligolo-ng) showing framework-driven, repeatable abuse.
IoT-focused botnets (Hajime, Mozi, and Mirai) remain present within Russian infrastructure, reflecting ongoing abuse of compromised embedded devices and routers.
Russian hosting environments support diverse malicious operations, including phishing campaigns, infostealer distribution, scanning infrastructure, and targeted intrusion activity.
The hosting layer is where that concentration becomes most visible, so that is where we start.
Top Russian Infrastructure Providers
The Host Radar summary for the top five Russian infrastructure providers highlights the scale and diversity of malicious activity observed across these organizations over the last three months.
TimeWeb, a Russian web hosting and domain provider, exhibits the highest number of C2 servers among the analyzed Russian providers, with 311 detected over 90 days, alongside 7 malicious open directories, 91 port scanners, 0 IOCs, 3 IOC Hunter posts, and 9 phishing sites.
This activity suggests that large shared hosting environments with accessible infrastructure and flexible payment options can be attractive for attackers deploying C2 infrastructure and scanning operations.
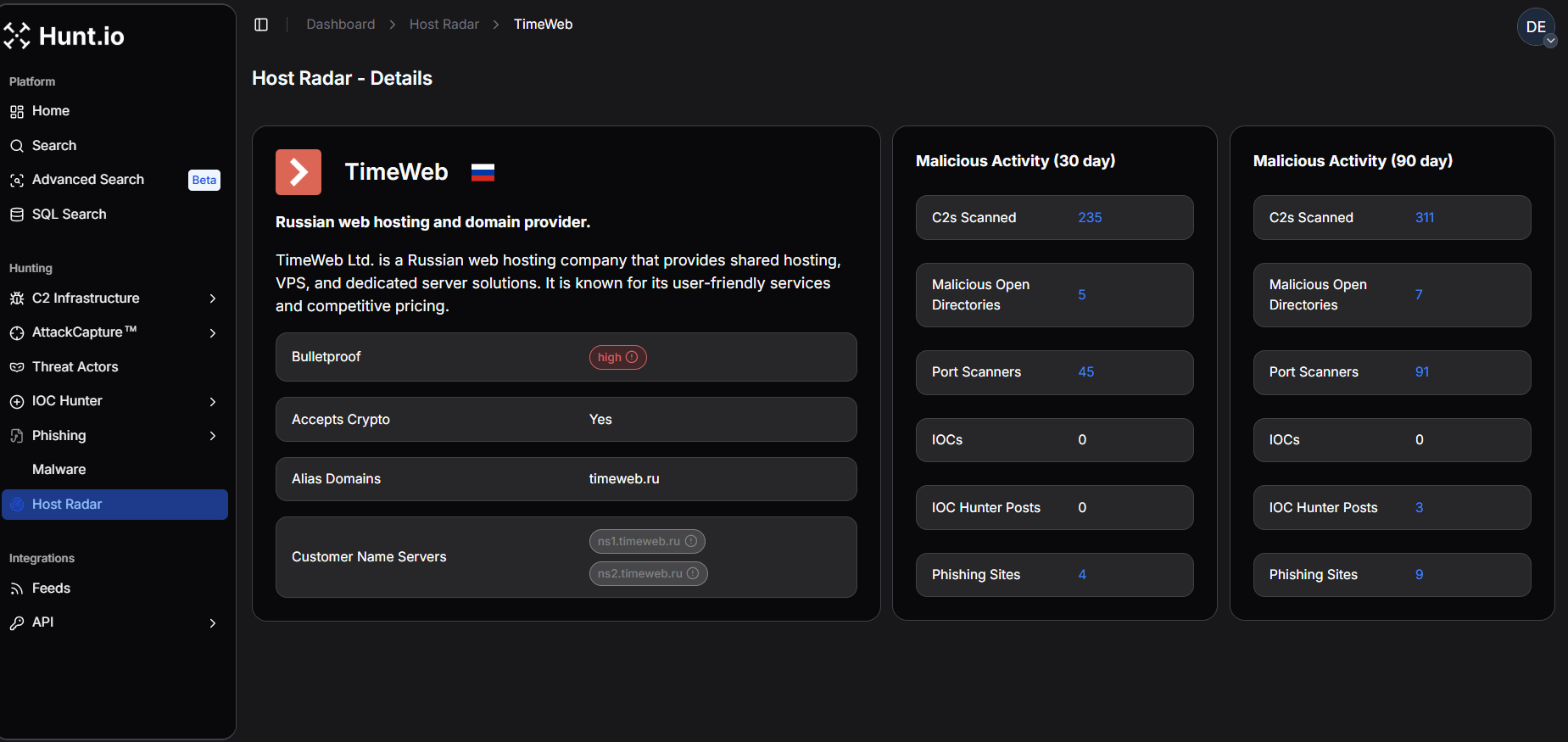 Figure 1. TimeWeb - Host Radar Detailed View: Per-provider Host Radar breakdown for TimeWeb, hi1ghlighting elevated C2 activity and associated scanning infrastructure.
Figure 1. TimeWeb - Host Radar Detailed View: Per-provider Host Radar breakdown for TimeWeb, hi1ghlighting elevated C2 activity and associated scanning infrastructure.Similarly, WebHost1, a hosting provider offering shared, VPS, and dedicated services, shows moderate C2 activity with 140 servers observed over 90 days, with no malicious open directories, port scanners, IOCs, IOC Hunter posts, or phishing sites detected.
This pattern indicates that while C2 infrastructure is present in the environment, there is little evidence of broader malicious artifacts, suggesting more isolated infrastructure use rather than large-scale abuse.
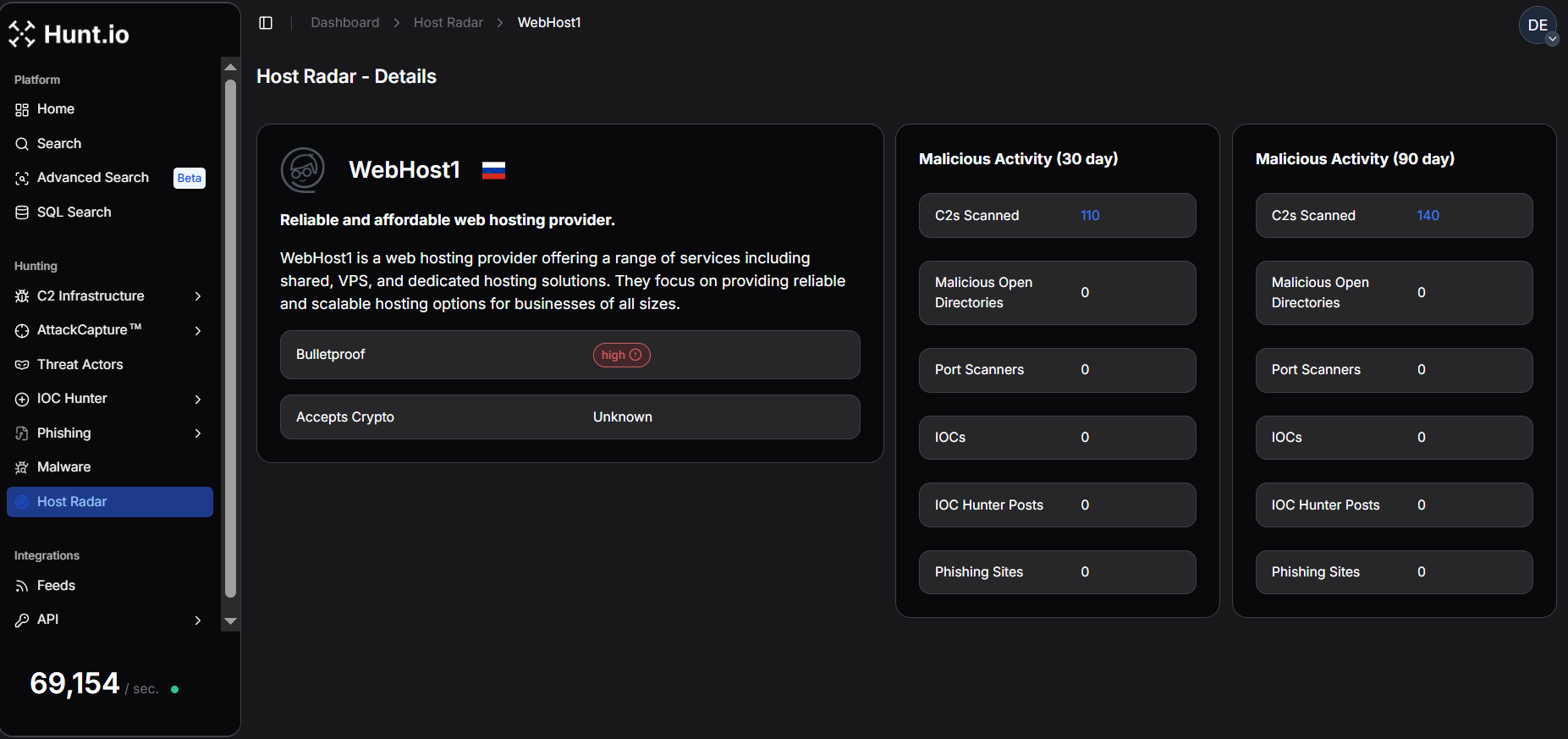 Figure 2. WebHost1 - Host Radar Detailed View: Host Radar metrics for WebHost1 illustrating moderate C2 infrastructure presence with limited associated malicious artifacts.
Figure 2. WebHost1 - Host Radar Detailed View: Host Radar metrics for WebHost1 illustrating moderate C2 infrastructure presence with limited associated malicious artifacts.REG.RU, one of Russia's leading domain registrars and hosting providers, exhibits a diverse malicious footprint. Over 90 days, it hosted 138 C2 servers, 38 port scanners, 0 IOCs, 4 IOC Hunter posts, and 2 phishing sites, while no malicious open directories were observed.
The presence of both scanning infrastructure and phishing campaigns indicates that domain and hosting providers supporting large numbers of customers may be leveraged for multiple stages of cyber operations, including reconnaissance and credential harvesting.
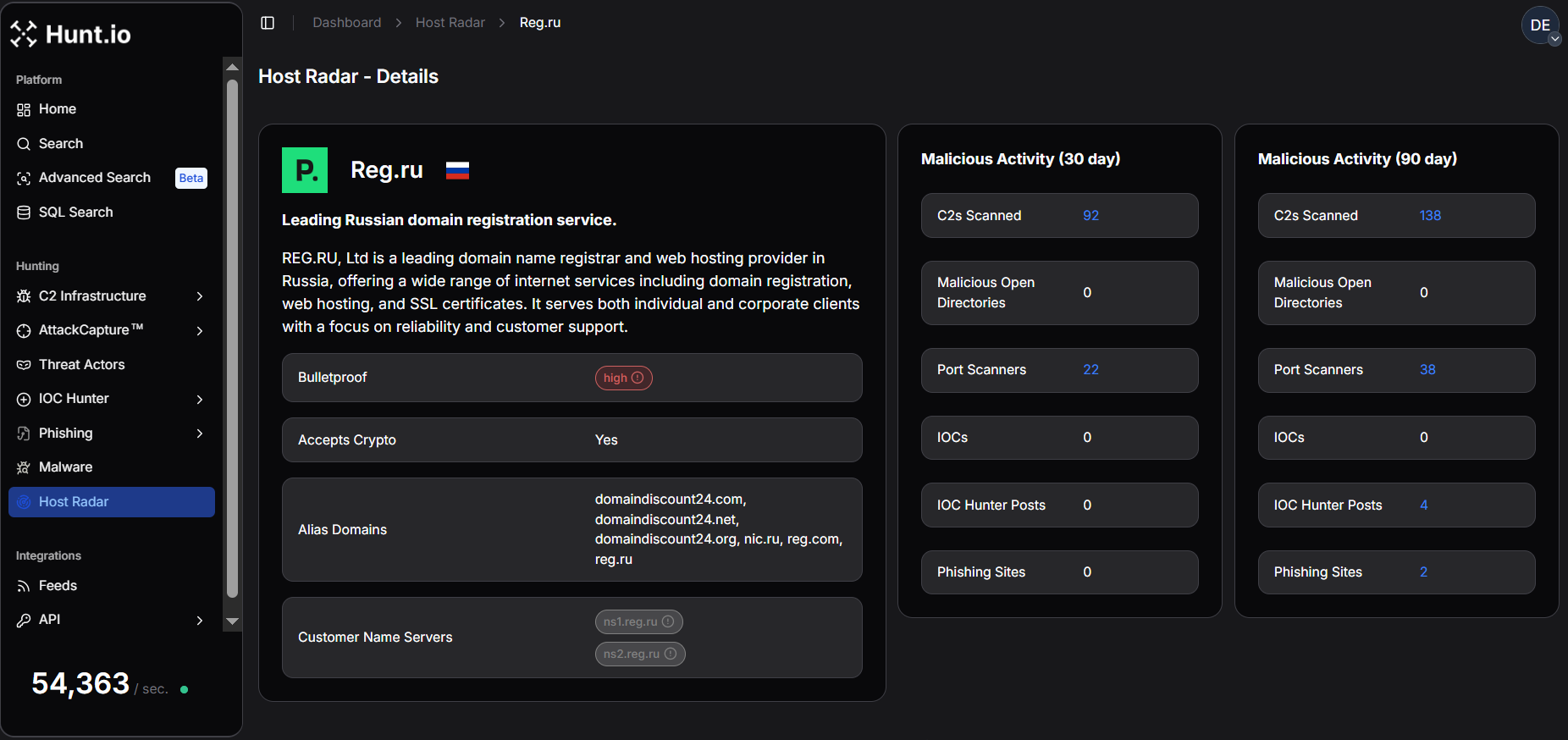 Figure 3. REG.RU - Host Radar Detailed View: Detailed Host Radar metrics showing REG.RU's mix of C2 infrastructure, port scanning activity, and phishing sites.
Figure 3. REG.RU - Host Radar Detailed View: Detailed Host Radar metrics showing REG.RU's mix of C2 infrastructure, port scanning activity, and phishing sites.In contrast, VDSina, a provider focused on virtual dedicated servers and cloud infrastructure, shows comparatively lower malicious activity, with 86 C2 servers, 2 malicious open directories, 4 port scanners, 4 IOCs, and 4 IOC Hunter posts detected over 90 days, while no phishing sites were observed.
This suggests a more limited but persistent presence of malicious infrastructure, likely tied to individual compromised or abused VPS instances.
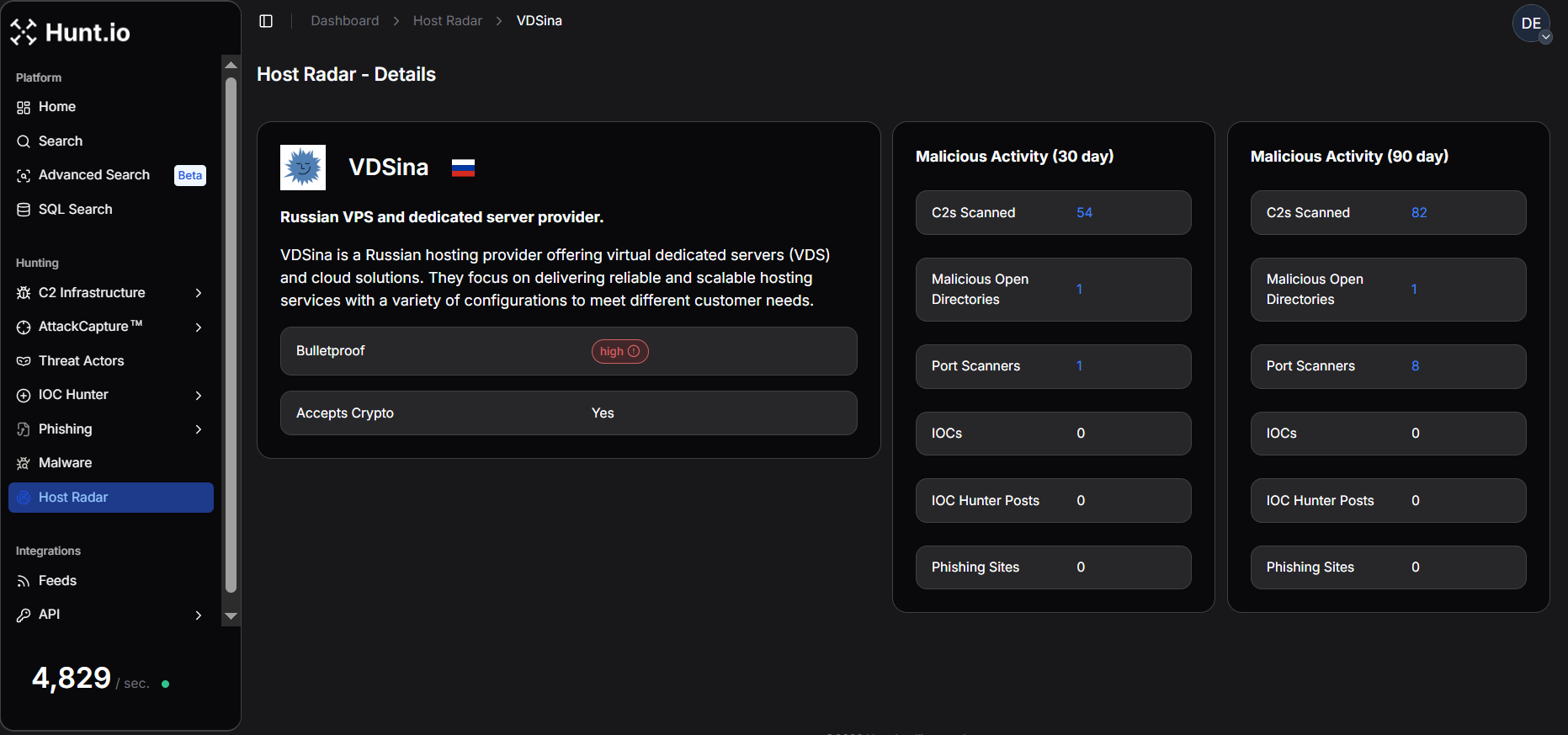 Figure 4. VDSina - Host Radar Detailed View: Host Radar metrics for VDSina reflecting relatively low but ongoing malicious infrastructure presence.
Figure 4. VDSina - Host Radar Detailed View: Host Radar metrics for VDSina reflecting relatively low but ongoing malicious infrastructure presence.PROSPERO OOO, a technology solutions provider offering hosting and infrastructure-related services, demonstrates a notable malicious footprint. Over 90 days, it hosted 80 C2 servers, 30 malicious open directories, 24 port scanners, 50 phishing sites, and 16 IOC Hunter posts, while no direct IOCs were recorded.
This combination indicates active reconnaissance and infrastructure staging, with scanning activity and exposed directories serving as precursors to broader malicious campaigns.
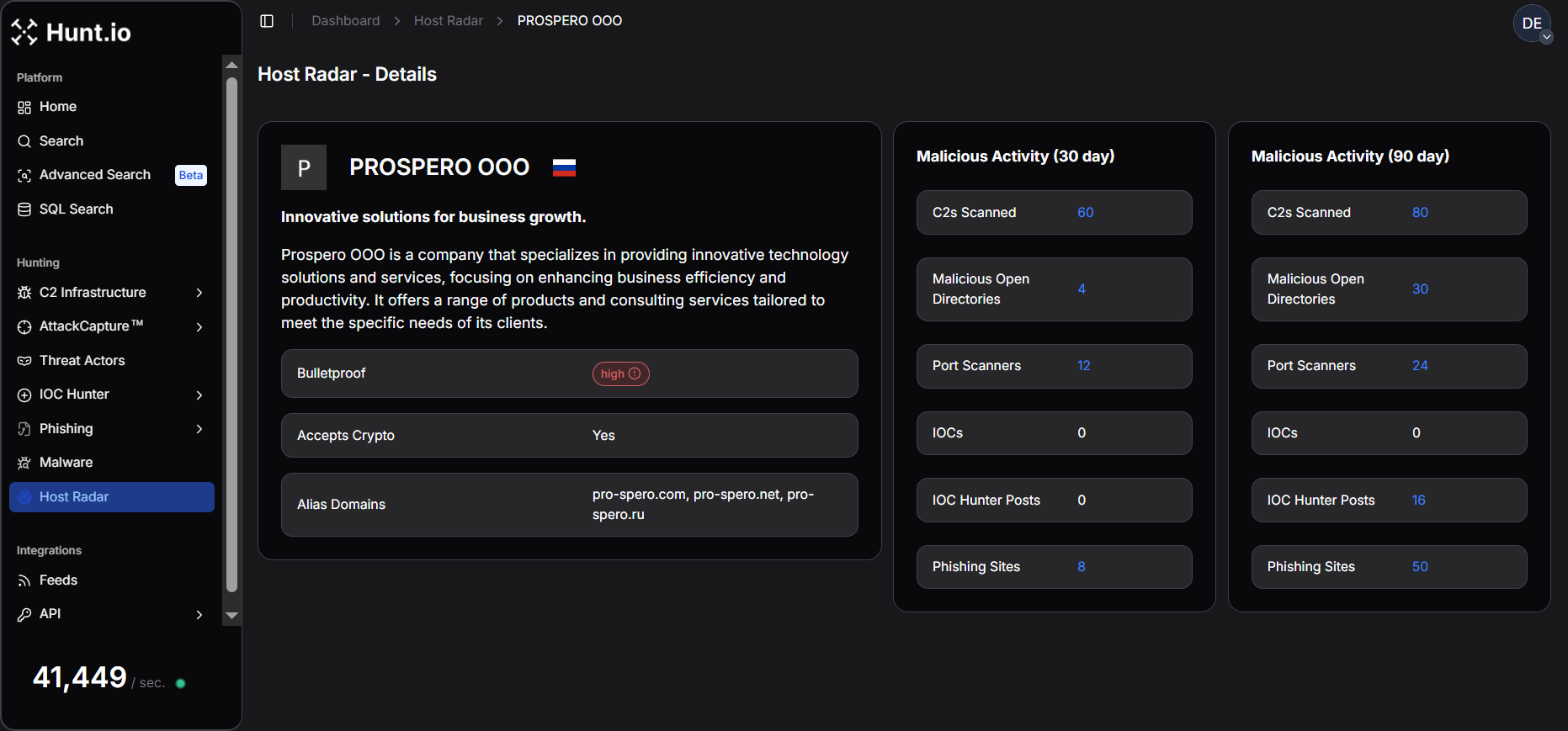 Figure 5. PROSPERO OOO - Host Radar Detailed View: Host Radar summary for the provider, highlighting command-and-control infrastructure alongside scanning activity.
Figure 5. PROSPERO OOO - Host Radar Detailed View: Host Radar summary for the provider, highlighting command-and-control infrastructure alongside scanning activity.With the top russian infrastructure hosting providers in mind, let's now focus on analyzing e the C2 infrastructure across different ISPs.
C2 Infrastructure Across Russian ISPs
This section describes how Host Radar was used to detect and attribute command-and-control (C2) infrastructure and related malicious artifacts operating within Russian hosting environments over a three-month observation window.
After applying the Russia country filter and restricting the observation window to the last three months, the Host Radar summary view reveals 165 distinct infrastructure providers and network entities operating within Russian ISPs, hosting providers, and cloud ecosystems that were associated with malicious activity.
This broad distribution shows the diversity of Russia's hosting ecosystem, where malicious infrastructure is spread across a large number of providers rather than concentrated in only a few networks.
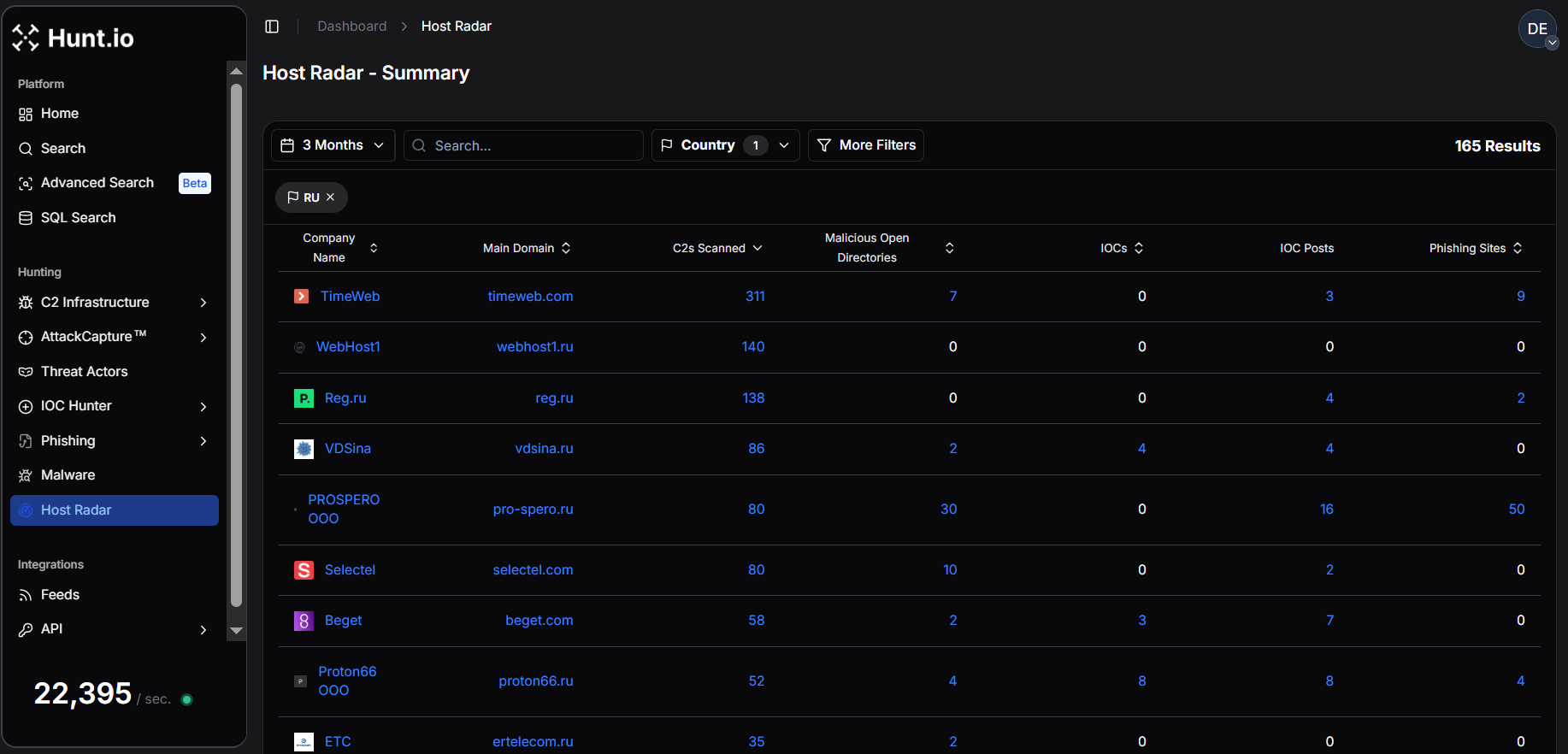 Figure 6. Host Radar summary view showing malicious infrastructure detected across 165 Russian ISPs and hosting providers over a three-month analysis window.
Figure 6. Host Radar summary view showing malicious infrastructure detected across 165 Russian ISPs and hosting providers over a three-month analysis window.Dataset Scope and Observed Infrastructure Landscape Over Russia
Across the full set of 165 Russian infrastructure providers, Host Radar recorded approximately 1,290 malicious artifacts during the three-month observation period. This includes 1,252 command-and-control (C2) servers, 75 malicious open directories, 17 indicators of compromise (IOCs) referenced in public research, and 69 phishing sites.
The data reveals that C2 infrastructure overwhelmingly dominates observed malicious activity, accounting for approximately 88.6% of all detected malicious artifacts. In comparison, malicious open directories represent about 5.3%, phishing infrastructure accounts for roughly 4.9%, while publicly reported IOCs contribute approximately 1.2% of the dataset.
This distribution suggests that Russian hosting environments are primarily leveraged for C2 operations, with fewer cases of exposed artifacts or publicly documented indicators compared to other infrastructure ecosystems.
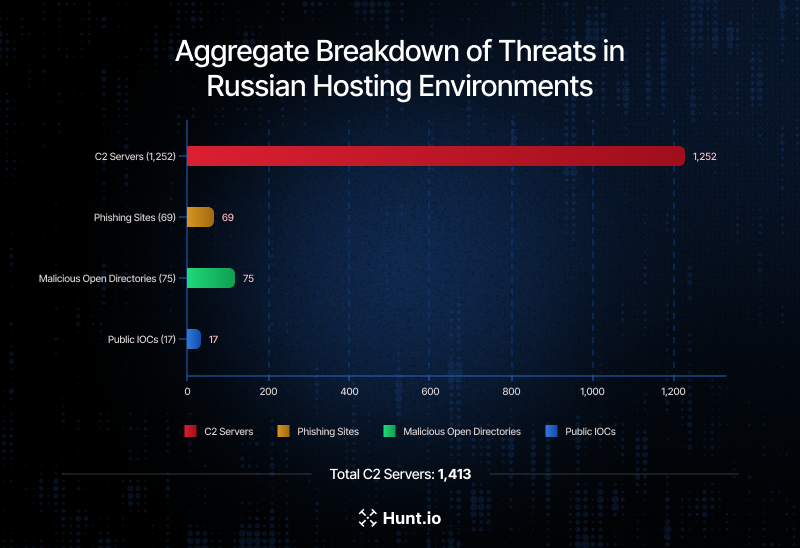 Figure 7. Aggregate breakdown of C2 servers (1,252), phishing sites (69), malicious open directories (75), and public IOCs (17) detected within Russian hosting environments.
Figure 7. Aggregate breakdown of C2 servers (1,252), phishing sites (69), malicious open directories (75), and public IOCs (17) detected within Russian hosting environments.Concentration of C2 Infrastructure Across Russian Providers
Moreover, the bar graph below visualizes the Top 10 companies by C2 server detections, where TimeWeb emerges as the most significant contributor with 311 detected C2 servers, representing the largest concentration of command-and-control infrastructure in this dataset.
This is followed by WebHost1 (140 C2 detections) and REG.RU (138 C2 detections), both large hosting providers serving a broad customer base. VDSina (86) and PROSPERO OOO (80) also appear among the most frequently abused infrastructure providers.
Other prominent providers include Selectel (80), Beget (58), Proton66 OOO (52), Er-Telecom (ETC) (35), and Rostelecom (27).
The presence of both commercial hosting companies and large telecommunications providers within the top rankings illustrates how virtual server platforms, cloud environments, and ISP networks can all be leveraged for malware C2 infrastructure deployment.
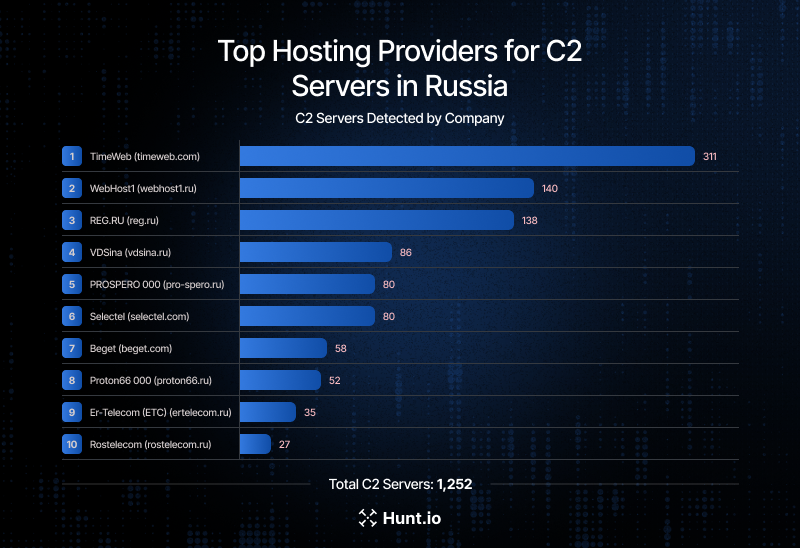 Figure 8. Top 10 Russian infrastructure providers by number of detected C2 servers over a three-month window, highlighting the distribution of malicious command-and-control infrastructure across hosting and telecom providers.
Figure 8. Top 10 Russian infrastructure providers by number of detected C2 servers over a three-month window, highlighting the distribution of malicious command-and-control infrastructure across hosting and telecom providers.Malware Family Distribution Within Russian Networks
Using HuntSQL, we analyzed the distribution of command-and-control (C2) infrastructure across malware families hosted within Russian networks over three months.
Example Query:
SELECT
malware.name,
uniq(ip) AS COUNTS
FROM
malware
WHERE
asn.country_name = 'Russia'
AND timestamp > NOW - 3 MONTH
GROUP BY
malware.name
ORDER BY
COUNTS DESC
CopyOutput Example:
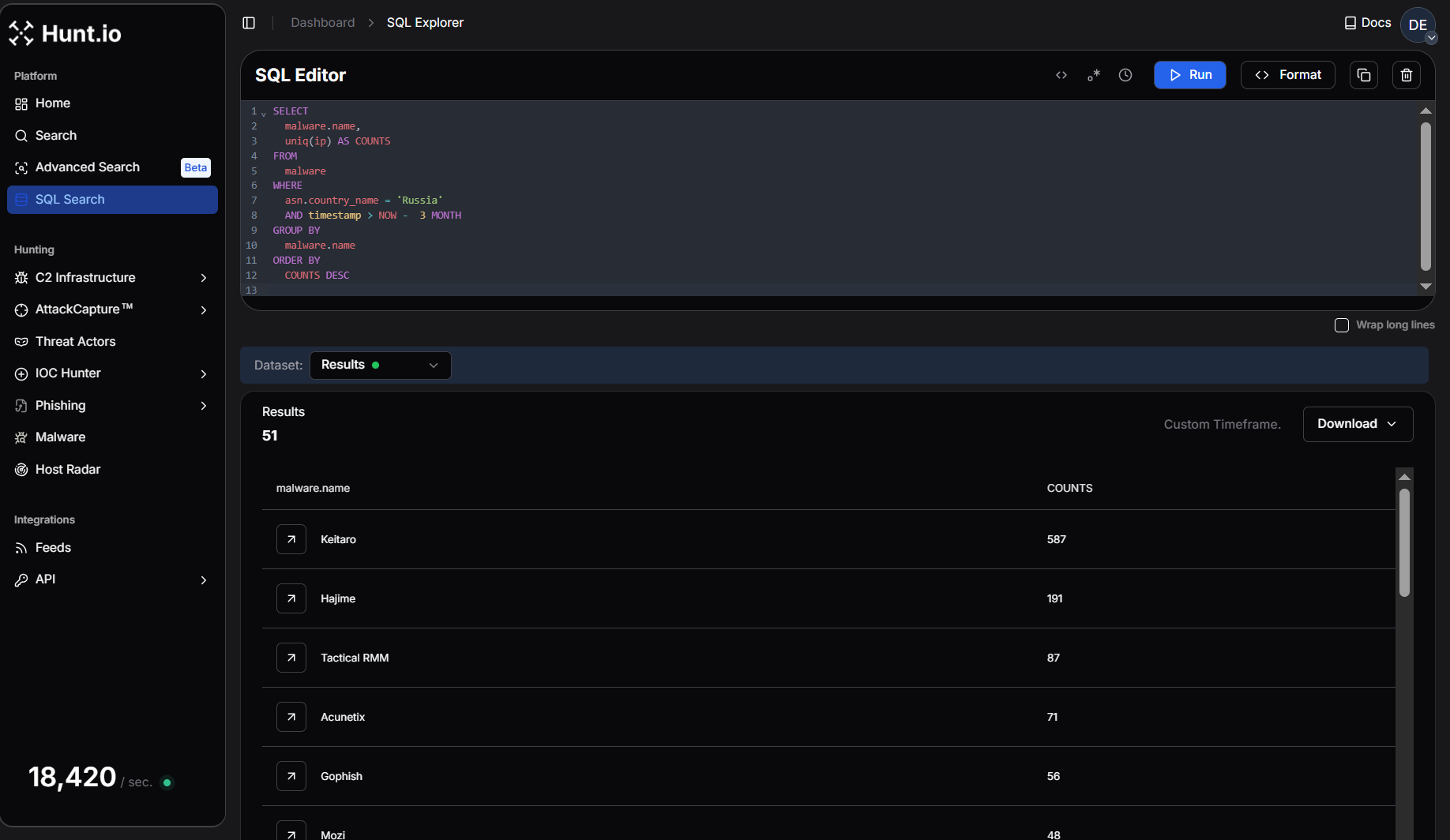 Figure 9. HuntSQL query output showing the dominant malware families hosting C2 infrastructure within Russian networks over three months.
Figure 9. HuntSQL query output showing the dominant malware families hosting C2 infrastructure within Russian networks over three months.The results reveal that Keitaro overwhelmingly leads the dataset with 587 unique C2 IPs, representing the largest concentration of command-and-control infrastructure observed in Russian hosting environments.
The second largest cluster, Hajime (191 C2s), reflects continued activity associated with IoT-focused botnet infrastructure, indicating that compromised embedded devices and routers continue to play a role in distributed malicious operations, followed by Mozi (48) and Mirai (13).
Several offensive security frameworks and post-exploitation platforms also appear prominently in the dataset. These include Tactical RMM (87), Cobalt Strike (25), Cobalt Strike Unverified (30), Sliver (24), and Ligolo-ng (10).
Scanning and phishing infrastructure tools such as Acunetix (71) and Interactsh (21) indicate vulnerability scanning, while Gophish (56) demonstrates the continued presence of phishing campaign infrastructure operating from Russian hosting environments.
This concentration lets defenders focus on shared infrastructure rather than individual malware variants rather than chasing individual malware variants.
.png) Figure 10. Bar graph illustrating the distribution of the Top 10 Malware Command-and-Control (C2) Families observed in Russia over the last three months.
Figure 10. Bar graph illustrating the distribution of the Top 10 Malware Command-and-Control (C2) Families observed in Russia over the last three months.Infrastructure Providers Hosting the Widest Malware Diversity
A HuntSQL query was designed to surface organizations hosting the widest variety of malware activity within Russian networks over the last three months. The query aggregates telemetry by org.name and calculates the number of distinct C2 IPs attributed to an organization (Unique_C2) as well as Unique_Malware, which reflects the diversity of malware families observed within that infrastructure.
Example Query:
SELECT
org.name,
uniq(ip) AS Unique_C2,
uniq(malware.name) AS Unique_Malware
FROM
malware
WHERE
org.name != ""
AND asn.country_name = 'Russia'
AND timestamp > NOW - 3 MONTH
GROUP BY
org.name
ORDER BY
Unique_Malware DESC
CopyOutput Example:
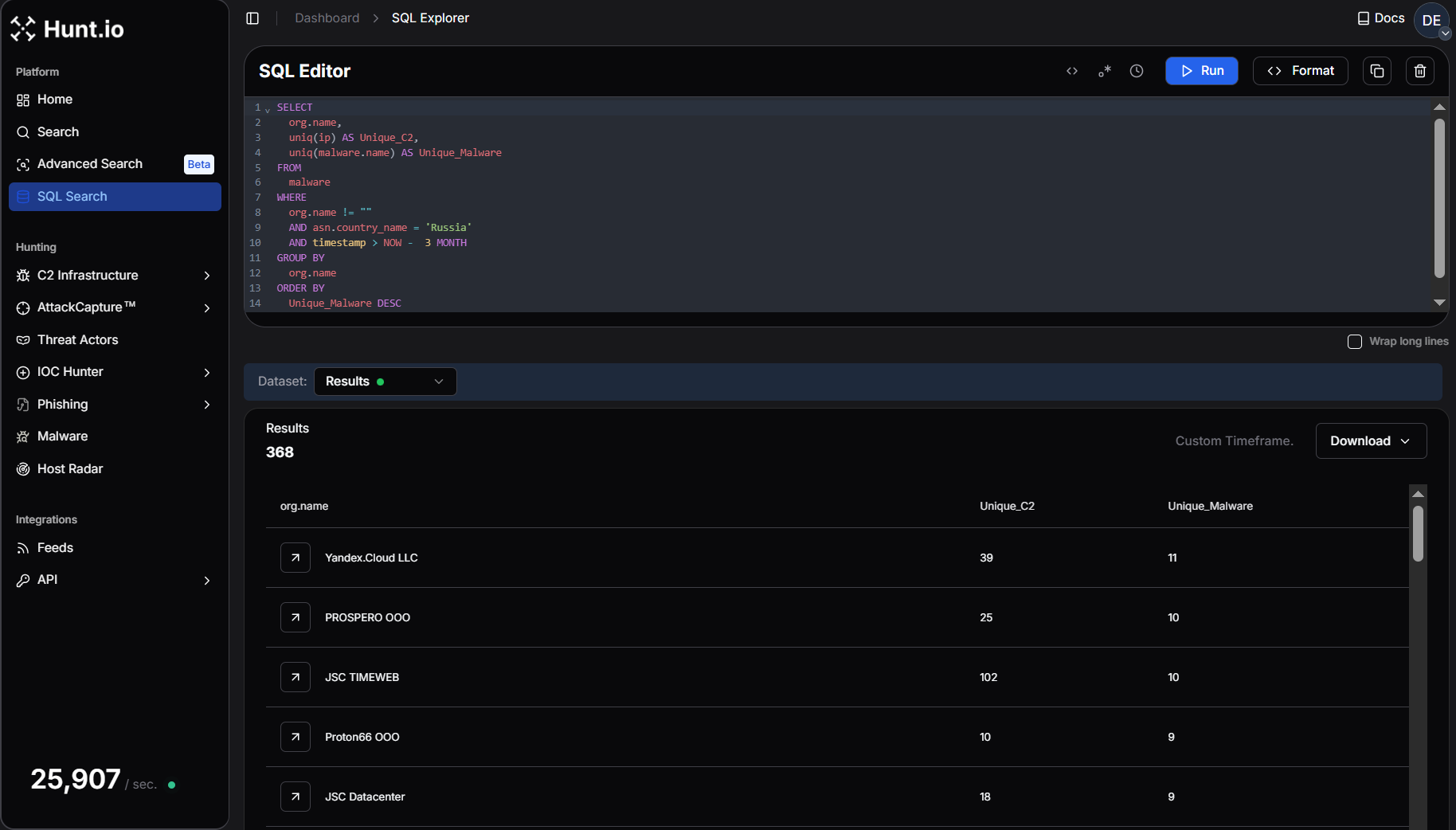 Figure 11. A HuntSQL query aggregating malware telemetry by a Russian organization to identify providers hosting the widest variety of malware families.
Figure 11. A HuntSQL query aggregating malware telemetry by a Russian organization to identify providers hosting the widest variety of malware families.The results reveal that malware activity is concentrated within a relatively small set of hosting and cloud providers, many of which support large-scale virtual server and hosting environments.
Yandex.Cloud LLC leads in malware diversity, hosting 11 distinct malware families across 39 unique C2 endpoints, followed by JSC TIMEWEB, which hosts 10 distinct malware families across 102 unique C2 endpoints. PROSPERO OOO also hosts 10 malware families associated with 25 unique C2 endpoints, while JSC Datacenter hosts 9 malware families across 18 C2 endpoints.
Other providers with notable malware diversity include Proton66 OOO (9 malware families), Hosting Technology LTD (8), LLC Baxet (8), and Selectel Network (7).
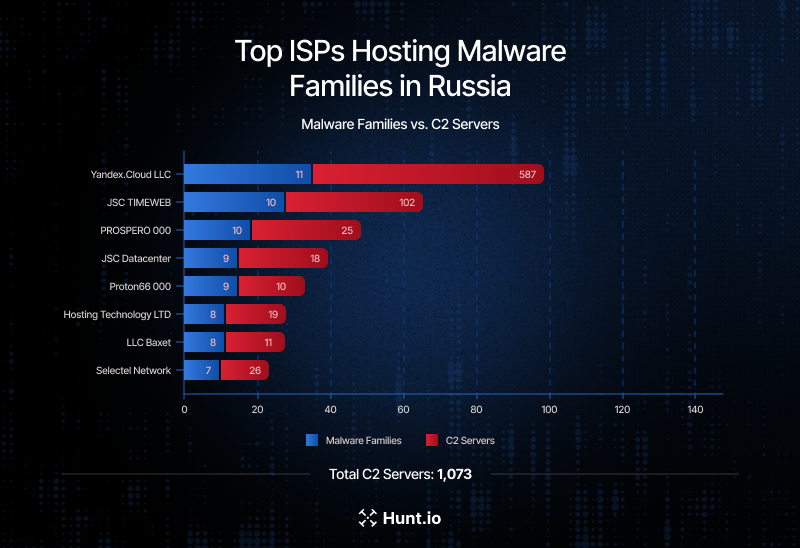 Figure 12. Malware Diversity vs. C2 Volume Across Russian ISPs - TIMEWEB leads in C2 density, while Yandex.Cloud hosts the widest range of malware families.
Figure 12. Malware Diversity vs. C2 Volume Across Russian ISPs - TIMEWEB leads in C2 density, while Yandex.Cloud hosts the widest range of malware families.Malicious Campaigns Observed Across Russian Hosting Environments
The following examples illustrate how the infrastructure patterns identified above translate into active malware campaigns, phishing operations, botnet activity, and targeted intrusion campaigns within Russian hosting environments.
Over the same period, Hunt.io tracking surfaced several malicious command-and-control (C2) endpoints hosted across Russian infrastructure providers, beginning with activity linked to Latrodectus malware hosted on JSC TIMEWEB infrastructure. The IP 85.239.54[.]130 was associated with a campaign analyzed by CERT Polska, where attackers leveraged a fake CAPTCHA "ClickFix" technique to trick users into executing a curl-to-PowerShell command.
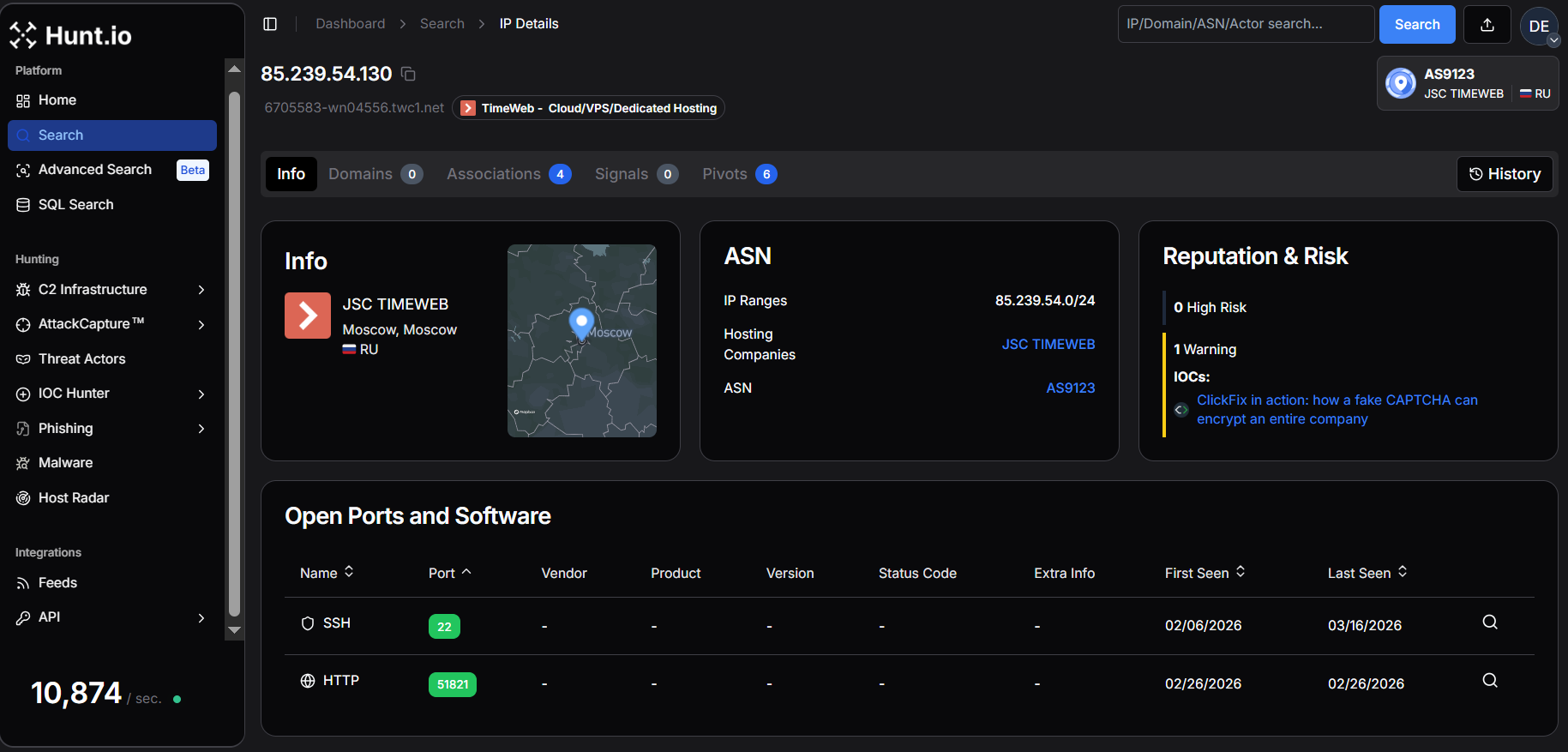 Figure 13. Hunt.io IP intelligence highlighting JSC TimeWeb infrastructure (AS9123) with ClickFix (Fake CAPTCHA Attack) risk indicators.
Figure 13. Hunt.io IP intelligence highlighting JSC TimeWeb infrastructure (AS9123) with ClickFix (Fake CAPTCHA Attack) risk indicators.Once executed, the command downloaded malicious payloads including Latrodectus v2.3, which communicated with attacker-controlled domains such as gasrobariokley[.]com and fadoklismokley[.]com.
Another example involved infrastructure hosted on REG.RU, where the IP 89.111.170[.]100 was linked to a Lumma Stealer malware campaign documented by CTM360. The operation abused Google Groups and Google-hosted redirectors to distribute malicious payloads across both Windows and Linux systems. Windows victims received large padded archives reconstructing AutoIt-based Lumma Stealer payloads, while Linux users were targeted with a trojanized Chromium variant known as Ninja Browser that installed malicious extensions and enabled persistent remote control of infected systems.
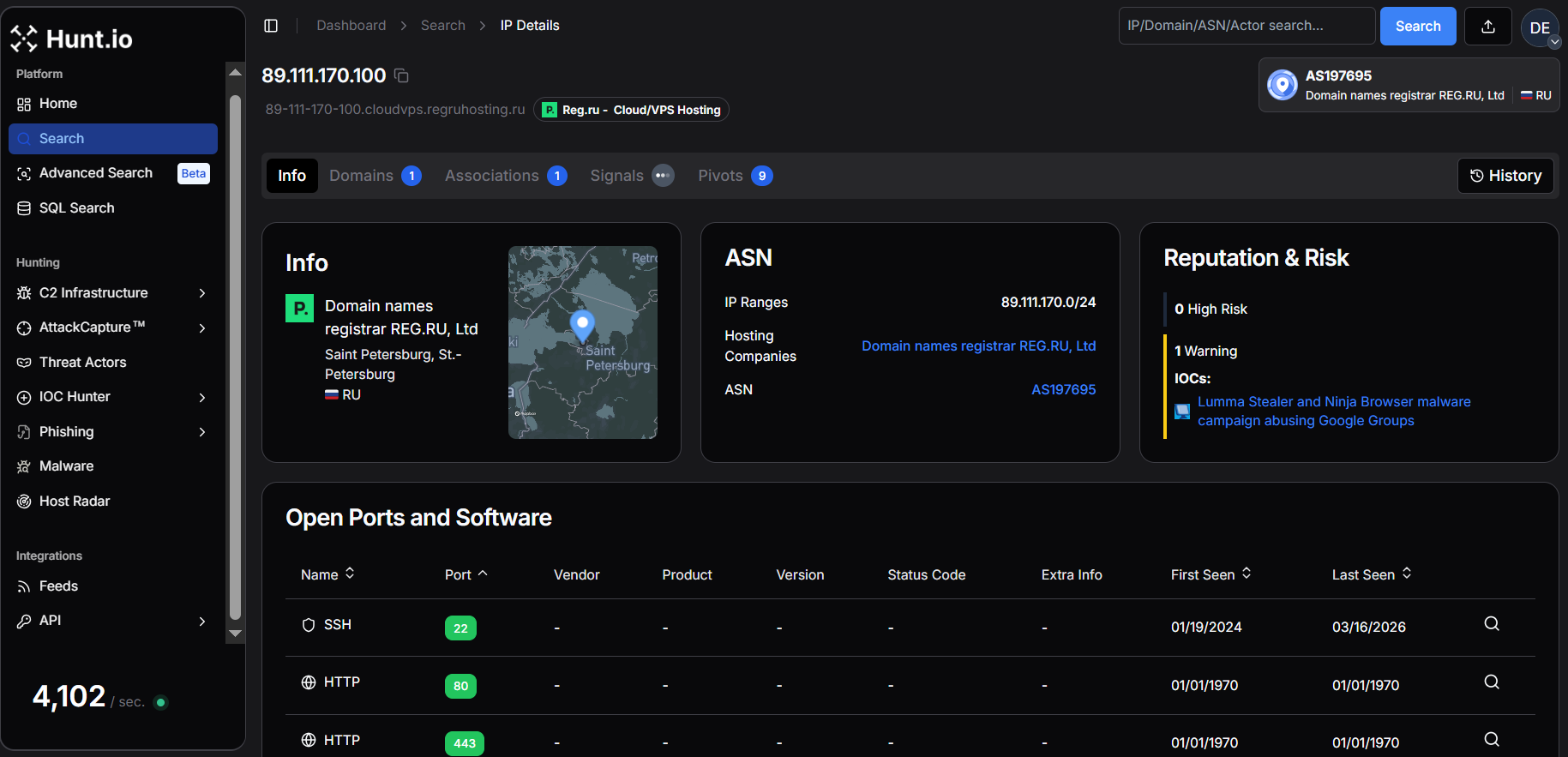 Figure 14. Hunt.io IP intelligence for 89.111.170[.]100 hosted by REG.RU Ltd (AS197695), linked to Lumma Stealer & Ninja Browser malware campaign.
Figure 14. Hunt.io IP intelligence for 89.111.170[.]100 hosted by REG.RU Ltd (AS197695), linked to Lumma Stealer & Ninja Browser malware campaign.Additional post-exploitation activity was identified on infrastructure belonging to Hosting Technology LTD, where the IP 193.178.170[.]155 was tied to the SmartApeSG campaign delivering Remcos RAT. In this campaign, attackers injected malicious JavaScript into compromised websites that displayed fake CAPTCHA prompts instructing users to execute commands copied to the clipboard. The execution downloaded a ZIP archive disguised as a PDF file that installed Remcos RAT via DLL sideloading, establishing persistence and connecting back to the attacker-controlled C2 server over TLS.
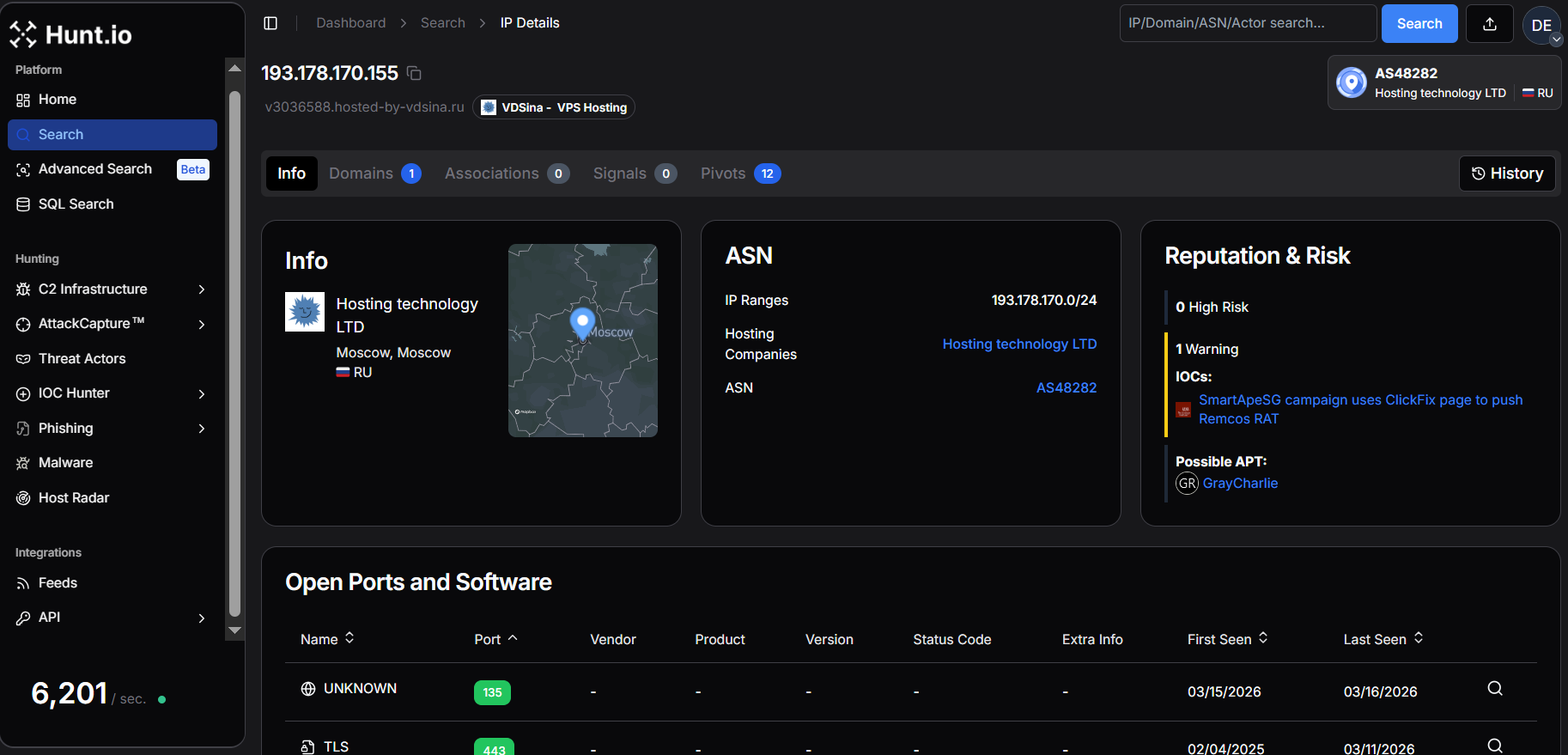 Figure 15. Hunt.io IP intelligence for 193.178.170[.]155 hosted by Hosting Technology LTD (AS48282), linked to SmartApeSG campaign delivering Remcos RAT and possible GrayCharlie APT activity.
Figure 15. Hunt.io IP intelligence for 193.178.170[.]155 hosted by Hosting Technology LTD (AS48282), linked to SmartApeSG campaign delivering Remcos RAT and possible GrayCharlie APT activity.Infrastructure hosted by Beget LLC appeared repeatedly across several campaigns. One example includes 85.198.98[.]75, which was associated with a phishing operation tracked as UAC-0252. The campaign impersonated Ukrainian government institutions and distributed archives containing executable files that ultimately deployed SHADOWSNIFF and SALATSTEALER infostealers, alongside a DEAFTICK backdoor. The operation relied on GitHub-hosted payloads and exploited a WinRAR vulnerability (CVE-2025-8088) to facilitate infection.
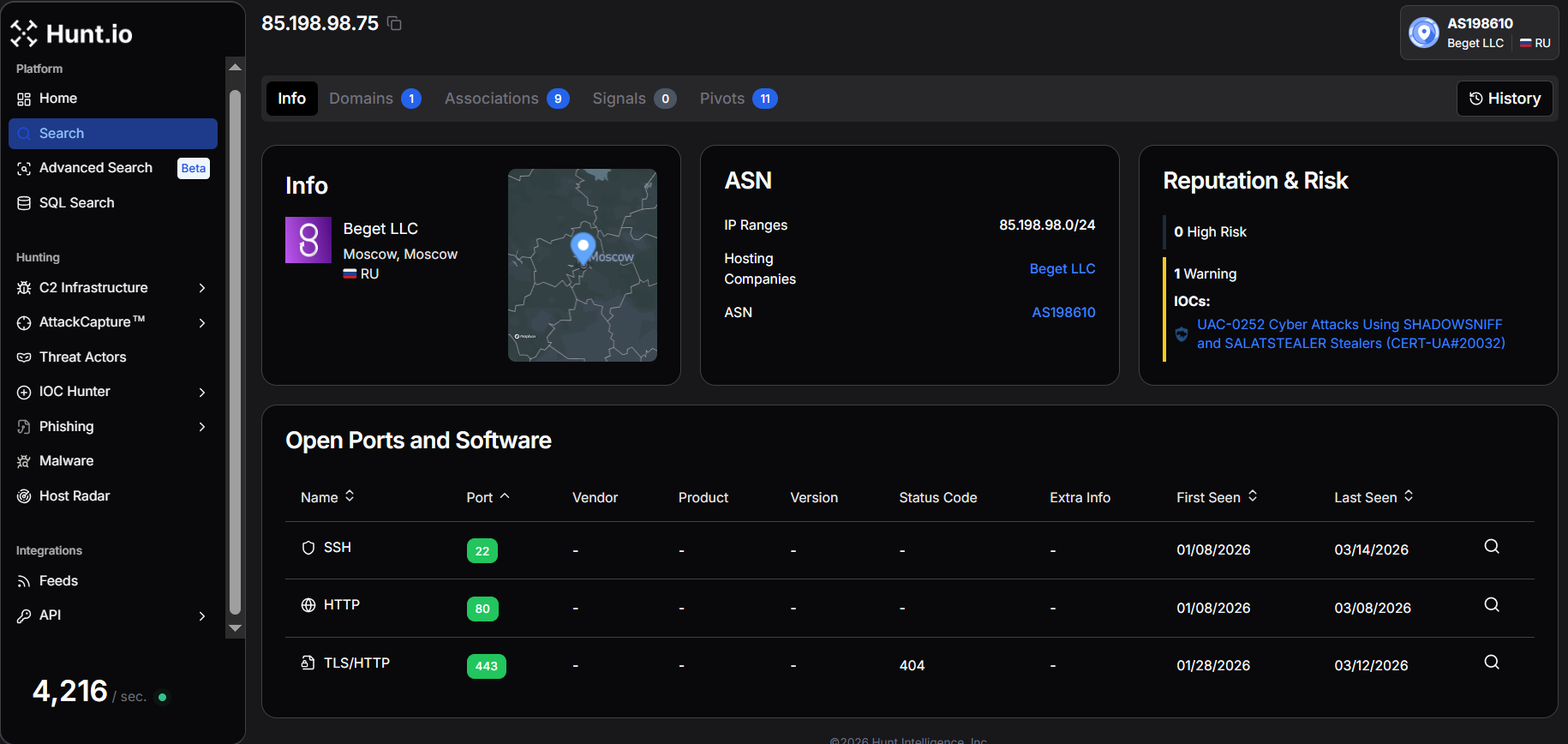 Figure 16. Hunt.io IP intelligence for 85.198.98[.]75 hosted by Beget LLC (AS198610), linked to UAC-0252 activity using SHADOWSNIFF & SALATSTEALER
Figure 16. Hunt.io IP intelligence for 85.198.98[.]75 hosted by Beget LLC (AS198610), linked to UAC-0252 activity using SHADOWSNIFF & SALATSTEALERSimilarly, another IP 45.130.41[.]81 was linked to the Diesel Vortex operation, a phishing-as-a-service platform branded Global Profit / MC Profit Always targeting logistics and transportation companies. Researchers recovered campaign infrastructure revealing Telegram-based coordination between operators, large-scale credential harvesting, and social-engineering operations, including voice phishing designed to enable cargo diversion and financial fraud.
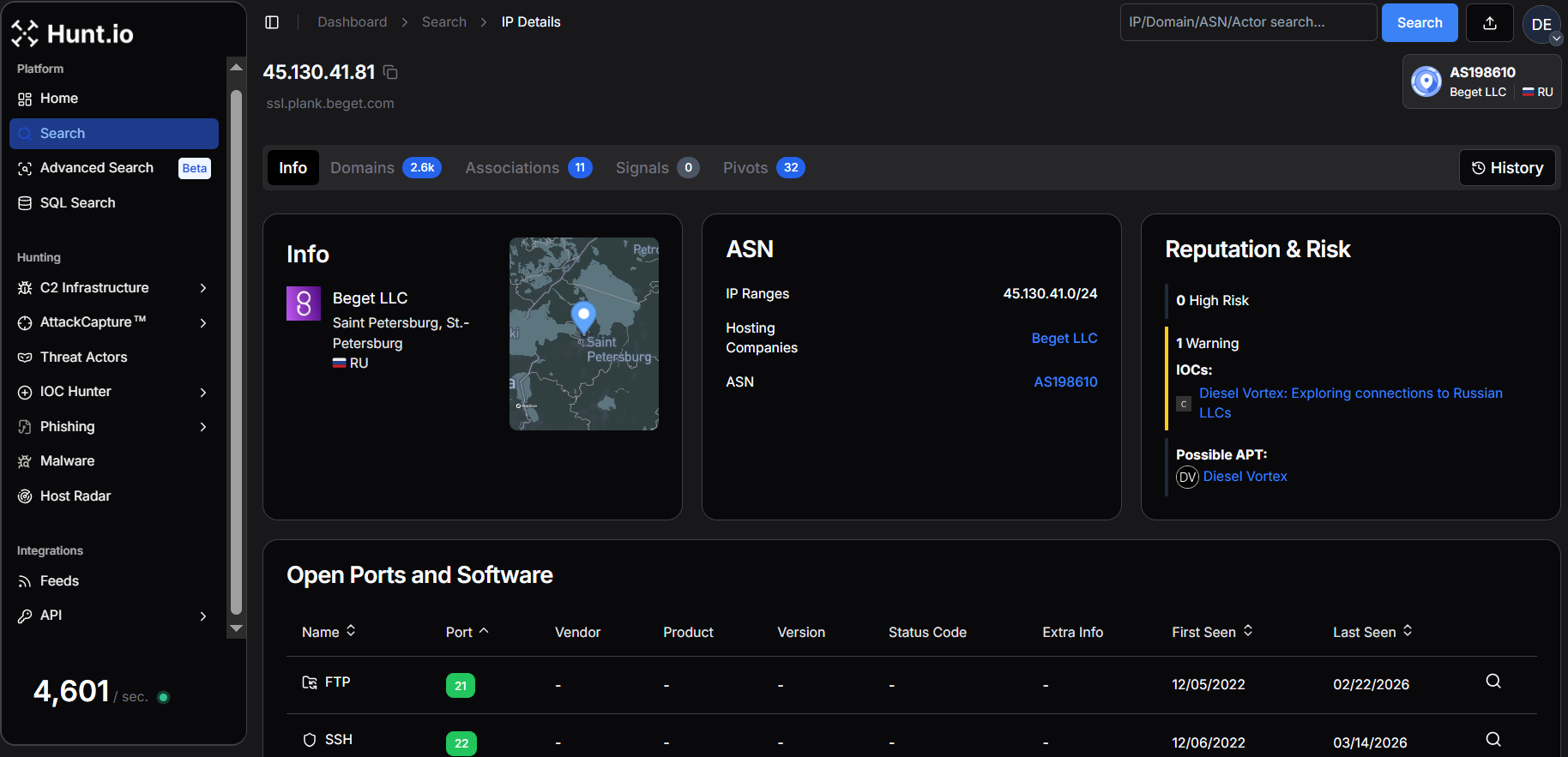 Figure 17. Hunt.io IP intelligence for 45.130.41[.]81 hosted by Beget LLC (AS198610), linked to Diesel Vortex activity and related infrastructure.
Figure 17. Hunt.io IP intelligence for 45.130.41[.]81 hosted by Beget LLC (AS198610), linked to Diesel Vortex activity and related infrastructure.Another IP 45.146.164[.]110 appeared in SSH honeypot telemetry, where analysts used HASSH fingerprinting to identify coordinated botnet activity leveraging the same libssh-based tooling across multiple IP addresses.
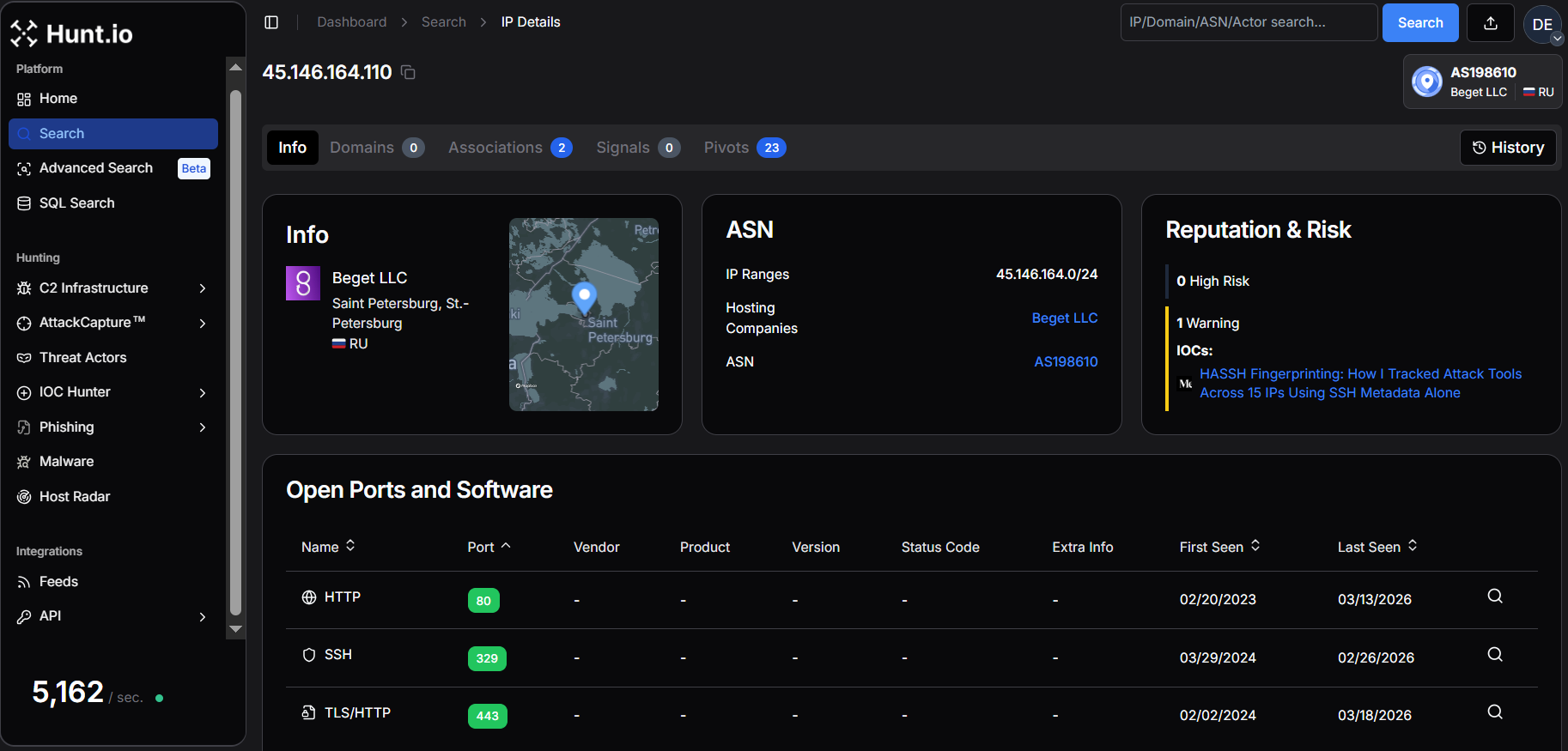 Figure 18. Hunt.io IP intelligence for 45.146.164[.]110 hosted by Beget LLC (AS198610), linked to HASSH fingerprinting-based threat tracking activity.
Figure 18. Hunt.io IP intelligence for 45.146.164[.]110 hosted by Beget LLC (AS198610), linked to HASSH fingerprinting-based threat tracking activity.In another research by Recorded Future, the researchers identified a campaign attributed to GrayCharlie, where compromised WordPress sites injected malicious JavaScript redirecting visitors to NetSupport RAT payloads. Infrastructure linked to this campaign included 217.114.15[.]253 and 45.153.191[.]245, both hosted by Beget LLC, demonstrating how compromised websites can serve as staging infrastructure for broader malware distribution.
A targeted intrusion activity was identified within infrastructure hosted by LLC Smart Ape, where multiple IPs, including 178.255.127[.]65, 188.127.227[.]46, and 188.127.254[.]233 were associated with operations attributed to the Head Mare threat group. According to Kaspersky's analysis, the campaign deployed a PowerShell backdoor called PhantomHeart alongside a rewritten proxy tool PhantomProxyLite. The malware leveraged AES-encrypted C2 communications, persistence through scheduled tasks, and reverse SSH tunneling to maintain long-term access within compromised environments.
Another notable campaign leveraged infrastructure hosted by Proton66 OOO, where the IP 193.143.1[.]104 was linked to a large-scale BoryptGrab infostealer operation. Researchers identified more than 100 public GitHub repositories being abused to distribute malware, with attackers using SEO manipulation and deceptive GitHub Pages (github[.]io) sites posing as legitimate tools and game cheats.
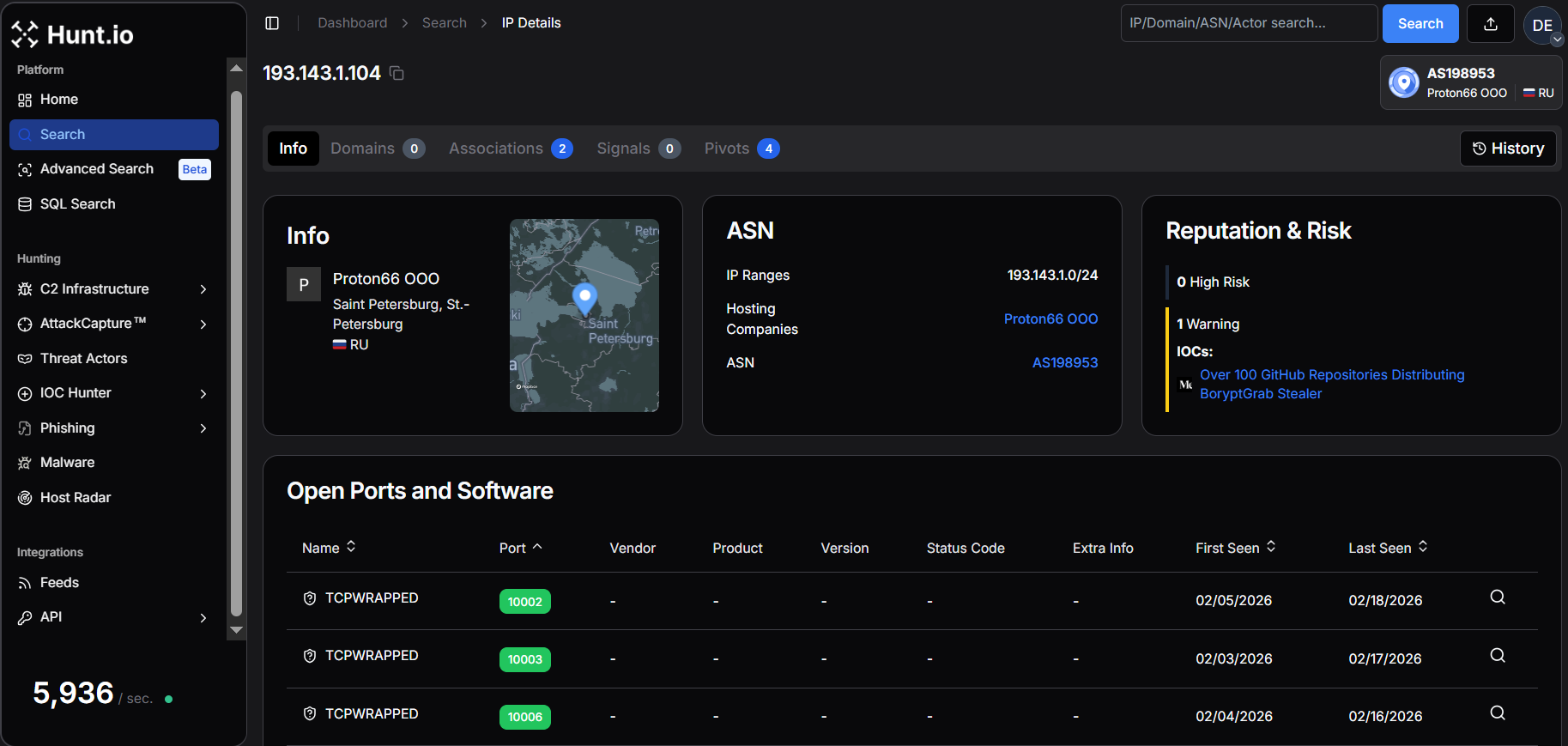 Figure 19. Hunt.io IP intelligence for 193.143.1[.]104 hosted by Proton66 OOO (AS198953), linked to BoryptGrab stealer distribution campaign.
Figure 19. Hunt.io IP intelligence for 193.143.1[.]104 hosted by Proton66 OOO (AS198953), linked to BoryptGrab stealer distribution campaign.These examples demonstrate how Russian hosting providers support a diverse threat landscape, ranging from phishing-driven infostealer campaigns and botnet activity to advanced intrusion operations and malware distribution infrastructure.
Infrastructure Observables
This research is based on a large set of infrastructure-level observables, including IP addresses, domains, and C2 endpoints that Hunt.io has identified and labeled as malicious infrastructure, active malware command-and-control, phishing infrastructure, or related abuse across Russian ISPs and hosting providers.
Given the scale of the dataset, with more than 1,250 active C2 endpoints observed over three months, publishing a static list here would provide limited operational value.
Teams interested in accessing this data with proper context, attribution, and historical tracking can reach out to discuss research collaboration or operational access to the full dataset.
Conclusion
This research shows the malicious activity in Russian hosting environments is heavily concentrated, with over 1,250 C2 servers spread across 165 providers, with TimeWeb, REG.RU, WebHost1, VDSina, and PROSPERO OOO hosting the majority of high-risk infrastructure, highlighting persistent reuse by threat actors.
A host-centric view of Russian infrastructure allows security teams to prioritize high-risk providers, track malware reuse, and implement mitigation strategies that disrupt attacker operations at scale, providing clearer visibility into the nation's threat landscape.
For security teams, this approach enables more resilient detection, faster prioritization, and infrastructure-level disruption strategies that are difficult for adversaries to evade. Host Radar and HuntSQL make this type of analysis practical by combining large-scale telemetry with flexible, analyst-driven investigation workflows.
If you want to explore this host-centric view of malicious infrastructure firsthand, you can see how Host Radar works in practice by booking a demo today.
Related Posts
Related Posts
Related Posts


